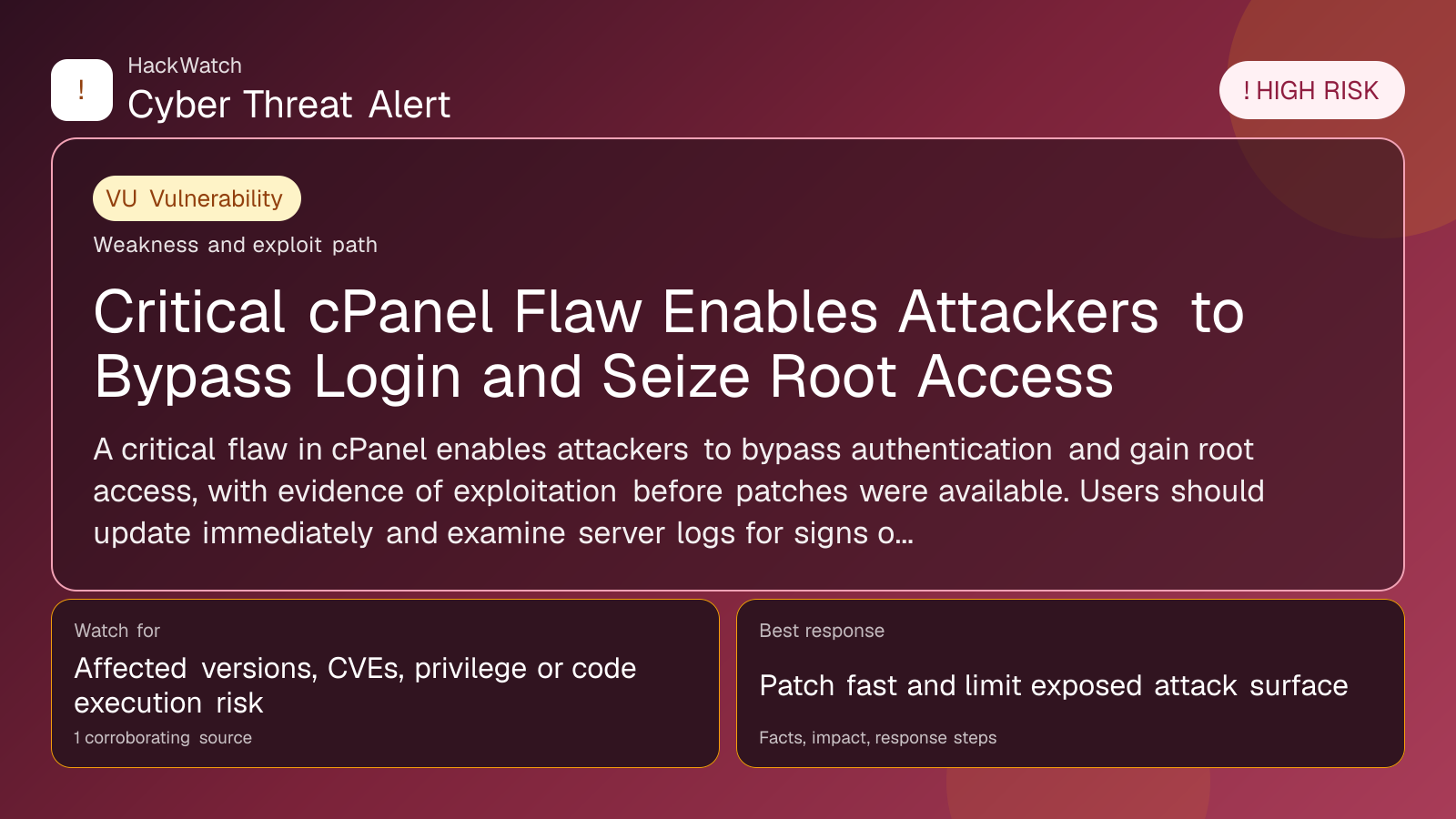
Critical cPanel Flaw Enables Attackers to Bypass Login and Seize Root Access
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: May 01, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
A critical flaw in cPanel enables attackers to bypass authentication and gain root access, with evidence of exploitation before patches were available. Users should update immediately and examine server logs for signs of compromise.
GLOBAL, May 1, 2026, 11:03 UTC
- A critical vulnerability in cPanel allows attackers to bypass login authentication and gain root privileges.
- Exploitation occurred before patches were released, heightening risks for hosting providers.
- Immediate patching and log review are advised to detect and prevent further breaches.
A severe security flaw has been identified in cPanel, a leading web hosting control panel. The vulnerability permits attackers to circumvent the login process and obtain root-level access to affected servers.
Reports and security researchers confirm that threat actors exploited this vulnerability before the vendor issued patches, exposing thousands of servers to potential takeover.
cPanel controls crucial server functions and user management. Root access grants attackers full control, allowing them to alter websites, exfiltrate data, or install malware.
The issue arises from a flaw in the authentication mechanism that fails to properly verify login credentials. Attackers can exploit this remotely without valid credentials, effectively bypassing the platform’s security.
In response, cPanel released an emergency advisory and patches shortly after discovery. Despite this, many systems remain unpatched, leaving them exposed.
Security analysts warn that attackers may use this flaw to implant backdoors, escalate privileges further, or move laterally within compromised networks. The pre-patch exploitation suggests either early disclosure to malicious actors or independent discovery.
Administrators and hosting providers are urged to apply updates immediately. Reviewing server logs for unusual login attempts or unauthorized root activity is critical to identify potential breaches.
This incident highlights the risks in shared hosting environments, where compromising a single server can impact multiple clients.
While cPanel continues to address the vulnerability, the exposure window before patch deployment underscores ongoing challenges in securing widely used server software.
Users uncertain about their exposure should contact their hosting provider or cPanel support. Delays in patching increase the chance of compromise.
No specific threat groups have been publicly linked to this vulnerability, but opportunistic attackers are actively targeting unpatched servers.
Additional protective steps include enabling multi-factor authentication and segmenting networks to limit the impact of any breach.
Unaddressed, the flaw risks data loss, service outages, and unauthorized access to sensitive information hosted on vulnerable servers.
Given the severity of root access compromise, organizations using cPanel should prioritize patching and monitoring efforts.
Source: https://hackread.com/cpanel-vulnerability-attacker-bypass-login-root-access/
Immediate Recommendations
- Verify your cPanel version and install the latest security patches.
- Audit server logs for unusual or unauthorized root logins.
- Inform your hosting provider if you do not manage your own environment.
- Restrict access to the cPanel interface using firewalls or VPNs until patched.
- Reset passwords and enable multi-factor authentication where possible.
Security Best Practices
- Maintain current backups of critical data.
- Use strong, unique passwords for all accounts.
- Limit administrative access to trusted IP addresses.
- Continuously monitor server activity for anomalies.
- Train staff to recognize phishing and social engineering attempts.
Outlook
By late 2026, cPanel has issued multiple patches addressing this and related vulnerabilities. Patch adoption varies across providers; some use automated updates to reduce exposure. However, unmanaged and legacy servers remain at risk, emphasizing the need for ongoing vigilance.
Proactive security measures and prompt patching remain essential to defend against threats exploiting this and similar vulnerabilities in server management platforms.
Sources used for this article
hackread.com
