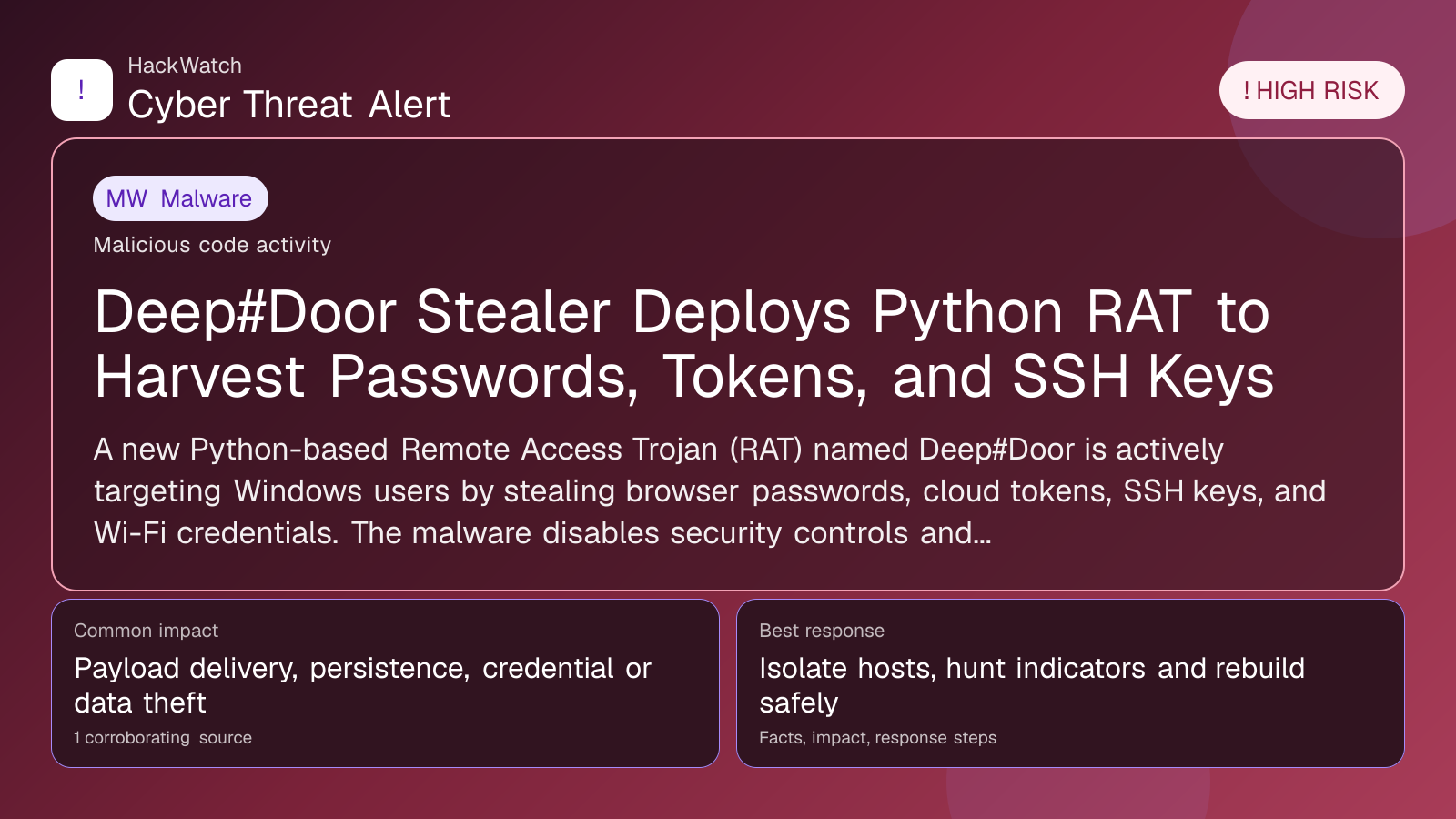
Deep#Door Stealer Deploys Python RAT to Harvest Passwords, Tokens, and SSH Keys
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: May 01, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 as a network administrator, looking first at device role, exposed management planes, VPN or routing impact and the order in which changes can be made without breaking production traffic. His note is deliberately operational: on Juniper-style edge or firewall environments, isolate admin access and preserve logs before patching, and do not claim broader exposure than the 1 corroborating source can prove.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A new Python-based Remote Access Trojan (RAT) named Deep#Door is actively targeting Windows users by stealing browser passwords, cloud tokens, SSH keys, and Wi-Fi credentials. The malware disables security controls and disguises its network traffic, raising significant risks for compromised systems.
GLOBAL, May 1, 2026, 06:44 UTC
- Deep#Door is a Python-based RAT that steals a broad range of credentials on Windows systems.
- It disables security controls and uses tunneling to hide its network activity.
Deep#Door is a newly identified Remote Access Trojan (RAT) that aggressively targets Windows users by extracting sensitive credentials including browser passwords, cloud authentication tokens, SSH keys, and Wi-Fi credentials. The malware uses an obfuscated batch loader to establish persistence and evade detection.
Researchers from GBHackers Security detailed that Deep#Door disables key security features on infected machines, allowing it to operate stealthily. It hides its data exfiltration behind the bore.pub tunneling service, complicating network monitoring efforts.
This threat matters now as credential theft remains a primary vector for lateral movement and further compromise in enterprise environments. The broad scope of data targeted by Deep#Door increases the risk of subsequent attacks such as account takeovers, unauthorized cloud access, and network infiltration.
Once executed, Deep#Door implants itself persistently, ensuring continued access even after system restarts. Its use of Python and batch scripts suggests the malware can be adapted or extended with relative ease, raising concerns about its potential evolution.
The inclusion of SSH keys and cloud tokens in its haul signals an intent to breach cloud infrastructure and remote servers, which could lead to significant data breaches or ransomware deployment.
Users and organizations should be particularly vigilant about credential hygiene and monitor for unusual network tunneling activity. The use of bore.pub as a cover channel is notable because it mimics legitimate traffic, making detection by traditional firewalls and intrusion detection systems challenging.
There is uncertainty about the initial infection vector for Deep#Door, though phishing and malicious downloads remain likely. The malware’s reliance on disabling security controls also means that systems with outdated or misconfigured defenses are especially vulnerable.
To mitigate risk, organizations should enforce multi-factor authentication, regularly rotate keys and tokens, and monitor endpoint behavior for signs of tampering. Network segmentation and strict egress filtering can help contain potential breaches.
Deep#Door’s emergence underscores the evolving threat landscape where attackers target diverse credential types to maximize access. Its stealth and persistence capabilities highlight the need for proactive detection and response strategies.
Security teams should prioritize scanning for indicators of compromise related to Deep#Door and update endpoint protection tools to recognize its batch loader and Python components.
Given the RAT’s ability to disable defenses, manual inspection and incident response may be necessary to fully eradicate infections.
This development follows a trend of increasingly sophisticated credential stealers that combine multiple attack techniques to evade detection and maintain long-term access.
Organizations relying heavily on SSH keys and cloud tokens should audit their usage and implement just-in-time access controls to limit exposure.
As of now, no public decryptors or removal tools specific to Deep#Door have been released, emphasizing the importance of prevention and early detection.
For users wondering if they are affected, signs include unexplained network traffic to bore.pub endpoints, disabled antivirus or firewall settings, and unexpected credential leaks. Immediate action involves isolating affected systems and conducting thorough credential resets.
Continued monitoring of threat intelligence feeds and applying security patches remain critical to defend against evolving RATs like Deep#Door.
Source: https://gbhackers.com/deepdoor-stealer/
Sources used for this article
gbhackers.com
