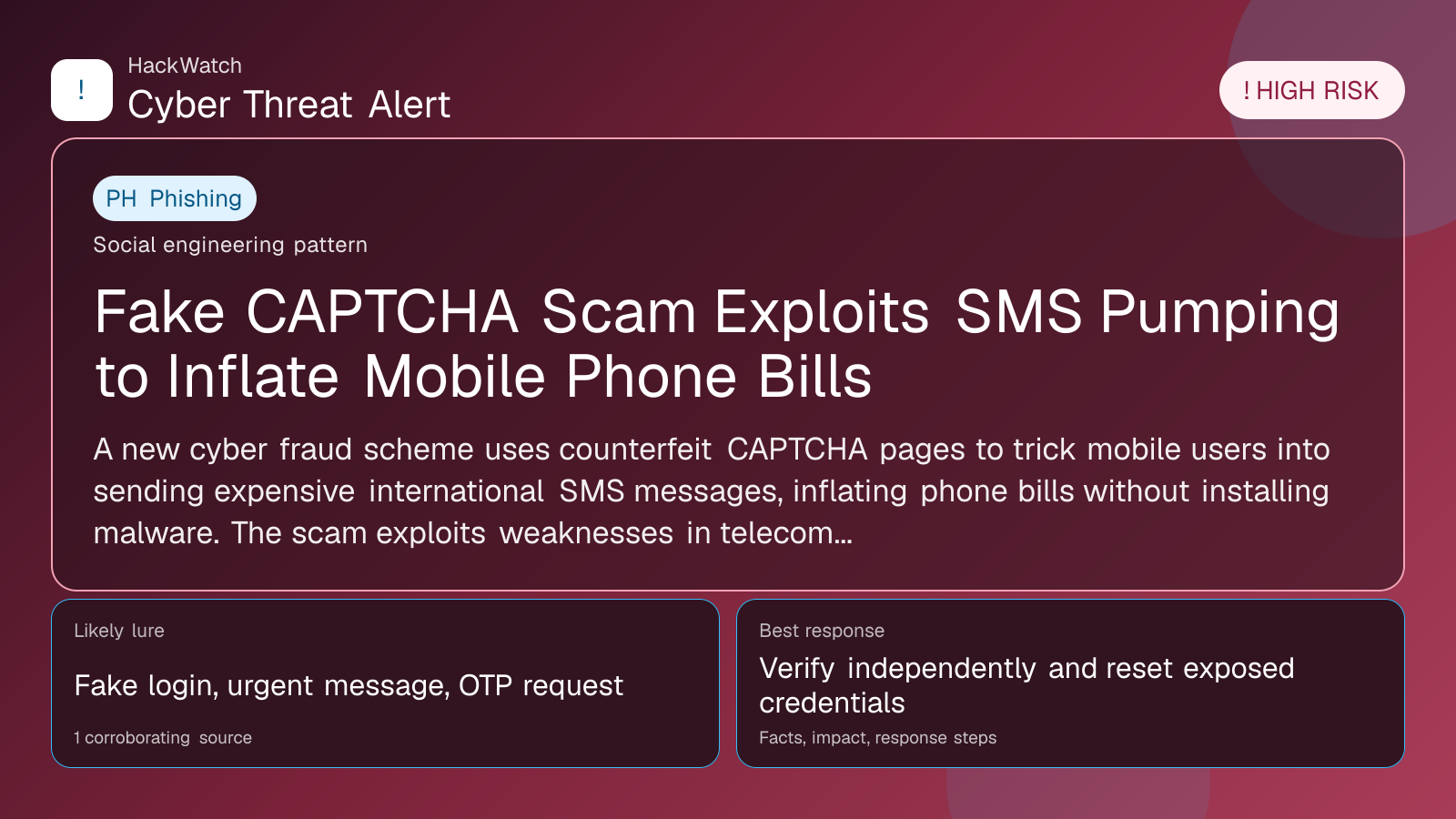
Fake CAPTCHA Scam Exploits SMS Pumping to Inflate Mobile Phone Bills
Verification-lure coverage focused on fake messages, cloned pages and account defense steps.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: May 01, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 for infrastructure impact, containment order and whether persistence or lateral-movement claims are supported by evidence. His administrator note is concrete: isolate the host or segment first, protect logs and network telemetry, then rebuild, rotate or patch only within the scope supported by the 1 corroborating source, the same cautious sequence he would use around managed router and server environments.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A new cyber fraud scheme uses counterfeit CAPTCHA pages to trick mobile users into sending expensive international SMS messages, inflating phone bills without installing malware. The scam exploits weaknesses in telecom billing and affiliate revenue systems to generate illicit profits.
GLOBAL, May 1, 2026, 05:06 UTC
- Fraudulent CAPTCHA pages coerce users into sending high-cost international SMS
- Scam inflates bills without malware, exploiting telecom and affiliate systems
- Attackers profit from premium SMS commissions through social engineering
Cybersecurity researchers at GBHackers Security have uncovered a new scam that targets mobile users by presenting fake CAPTCHA pages. These deceptive pages prompt victims to send multiple international SMS messages, resulting in substantial charges on their phone bills.
Unlike conventional cyberattacks that rely on malware, this campaign bypasses software installation entirely. Instead, it manipulates users into willingly sending premium-rate SMS messages under the guise of completing legitimate security checks.
The timing of the scam is significant as global mobile usage rises and CAPTCHA challenges become more common online. Attackers exploit users’ trust in these familiar verification steps to pressure them into sending costly SMS codes.
The counterfeit CAPTCHA pages are designed to closely mimic recognized websites or services, increasing their credibility. Once engaged, users are instructed to send several international SMS messages, which telecom providers bill at inflated rates.
This scheme leverages vulnerabilities in telecom billing processes and affiliate revenue models. Cybercriminals earn commissions from premium SMS services triggered by the victims’ messages, creating a profitable feedback loop for fraudsters.
Users often fail to spot the scam immediately since the SMS messages appear to originate from legitimate sources. The resulting inflated phone bills typically surface weeks later, complicating detection and remediation.
Industry experts caution that this scam could expand rapidly because it requires no technical skill or malware deployment, broadening the pool of potential perpetrators.
Telecom operators and regulators face difficulties in tracing and blocking these fraudulent SMS flows, especially when international numbers and complex affiliate networks are involved.
Users are urged to be wary of unexpected CAPTCHA prompts that demand sending SMS messages and to verify the authenticity of such requests before responding.
If targeted, consumers should review phone bills for unexplained international SMS charges and report suspicious activity to their carriers immediately.
This incident highlights the urgent need for stronger verification methods that do not rely solely on SMS and for increased user awareness regarding phishing and social engineering tactics.
While the full extent of affected users remains unknown, the scam’s reliance on social engineering over malware marks a shift in cybercriminal strategies toward exploiting human behavior and telecom infrastructure.
Ongoing monitoring will assess how telecom providers and cybersecurity firms respond to this evolving threat.
Source: https://gbhackers.com/fake-captcha-scam-2/
Sources used for this article
gbhackers.com
