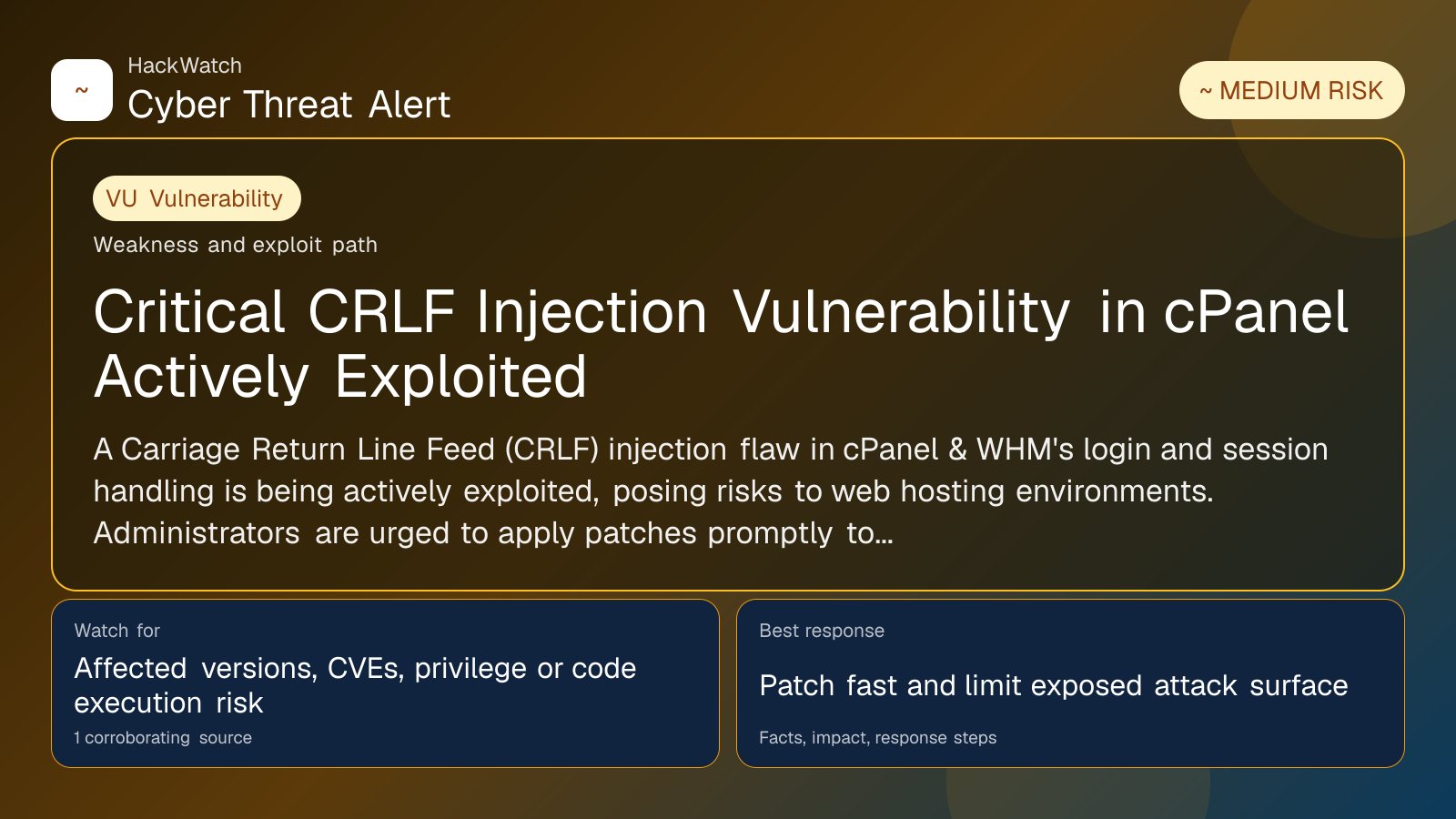
Critical CRLF Injection Vulnerability in cPanel Actively Exploited
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: May 01, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A Carriage Return Line Feed (CRLF) injection flaw in cPanel & WHM's login and session handling is being actively exploited, posing risks to web hosting environments. Administrators are urged to apply patches promptly to mitigate potential account compromise and session hijacking.
GLOBAL, May 1, 2026, 00:08 UTC
- A critical CRLF injection vulnerability in cPanel & WHM is under active exploitation.
- The flaw affects login and session loading processes, risking account hijacks.
- Immediate patching is recommended to prevent unauthorized access.
A critical vulnerability in cPanel & WHM, a widely used web hosting control panel, is currently being exploited in the wild. The flaw, identified as a Carriage Return Line Feed (CRLF) injection, targets the login and session loading mechanisms, allowing attackers to manipulate HTTP headers.
CRLF injection is a technique where an attacker inserts carriage return and line feed characters into input fields, enabling them to alter server responses or inject malicious content. In this case, the vulnerability can lead to session hijacking or unauthorized access to hosting accounts.
The active exploitation of this vulnerability raises immediate concerns for hosting providers and website administrators relying on cPanel. Compromised accounts could lead to website defacement, data theft, or the deployment of malware.
cPanel has not publicly disclosed detailed technical specifics but has confirmed the issue and is expected to release a patch imminently. Security researchers emphasize the importance of applying updates as soon as they become available to reduce exposure.
This vulnerability's timing is critical, as many hosting environments remain unpatched due to the complexity of updating live servers. Attackers are leveraging automated tools to scan for vulnerable instances, increasing the risk of widespread compromise.
Administrators should verify their cPanel & WHM versions and monitor for suspicious login activity. Implementing multi-factor authentication (MFA) can provide an additional layer of defense against unauthorized access.
The incident underscores the persistent risks facing web hosting platforms, which remain prime targets for cybercriminals seeking to exploit vulnerabilities for financial gain or disruption.
Organizations using cPanel are advised to review their security posture, including regular backups and incident response plans, to mitigate potential damage from exploitation.
Risk remains that some hosting providers may delay patching due to operational constraints, prolonging vulnerability windows. Attackers may also develop new exploitation techniques exploiting this flaw.
Users uncertain about their exposure should consult with their hosting provider or security teams to confirm patch status and review access logs.
As of now, no large-scale breaches linked to this vulnerability have been publicly reported, but the active exploitation status warrants immediate attention.
This report is based on multiple corroborating sources, including security advisories and industry analysis from scmagazine.com.
What to Do Now
- Check your cPanel & WHM version for vulnerability status.
- Apply official patches immediately once released.
- Enable multi-factor authentication on all accounts.
- Monitor login and session activity for anomalies.
- Review and strengthen your backup and recovery procedures.
How to Secure Yourself
- Limit access to cPanel interfaces to trusted IP addresses.
- Use strong, unique passwords for all hosting accounts.
- Regularly update all software components beyond cPanel.
- Educate staff about phishing and social engineering risks.
2026 Update
As of mid-2026, cPanel has released patches addressing the CRLF injection flaw. Adoption rates vary, with some environments still at risk due to delayed updates. Continued vigilance and patch management remain critical to defend against evolving exploitation tactics.
For ongoing updates, monitor official cPanel communications and trusted cybersecurity news outlets.
Source: https://www.scworld.com/brief/critical-cpanel-vulnerability-actively-exploited-in-the-wild
Sources used for this article
scmagazine.com
