Critical cPanel and WHM Authentication Bypass Zero-Day Exploited Since February; PoC Released
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 from an administrator's point of view, checking CVE-2026-41940 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 2 corroborating sources supports that scope.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
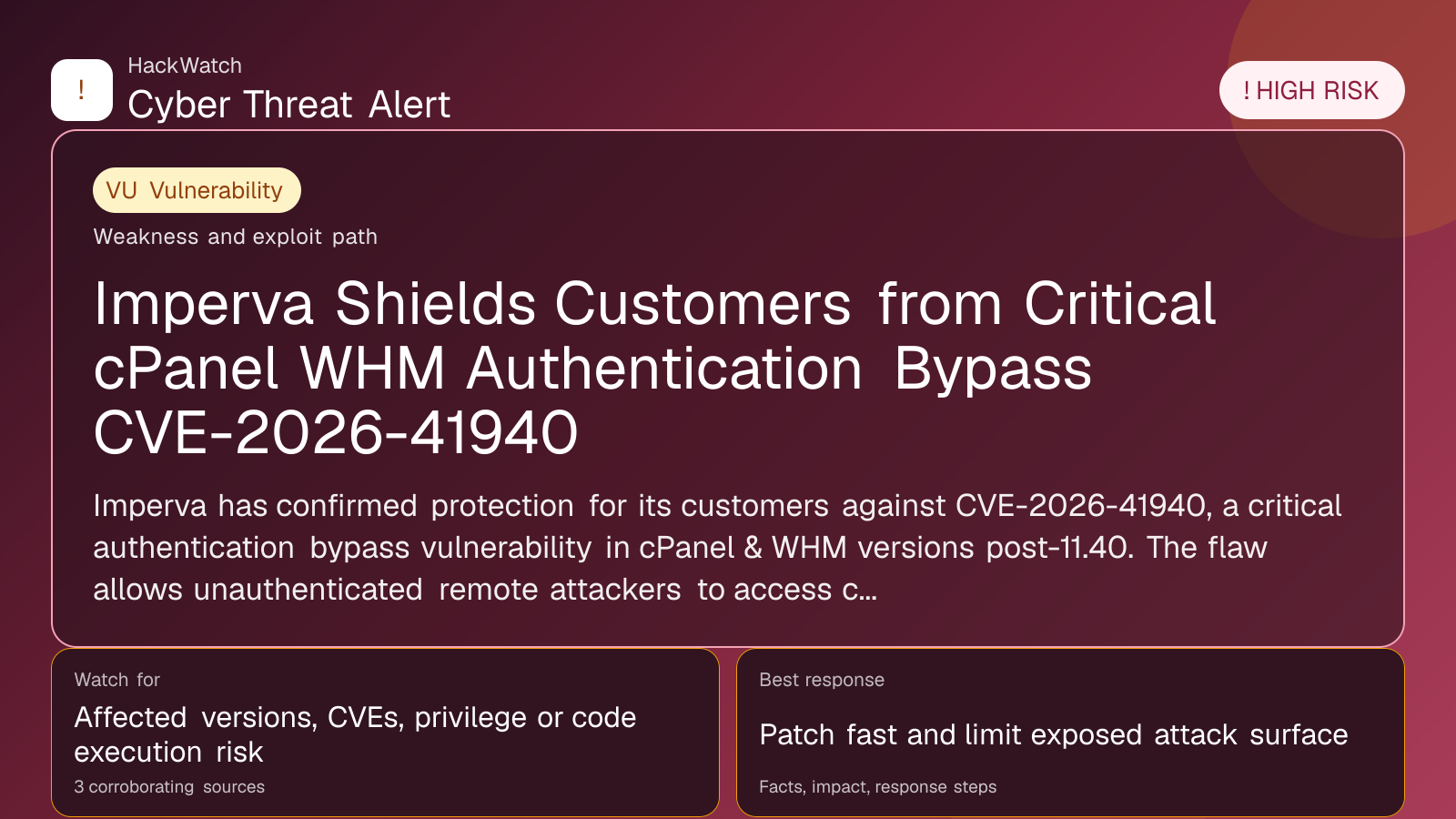
A severe authentication bypass vulnerability tracked as CVE-2026-41940 in cPanel, WHM, and WP Squared has been actively exploited since late February. Proof-of-concept code is now publicly available, increasing the risk of widespread attacks. Users are urged to apply patches immediately and review access logs for suspicious activity.
GLOBAL, April 30, 2026, 11:42 UTC
- CVE-2026-41940 is an authentication bypass flaw affecting cPanel, WHM, and WP Squared.
- Active exploitation has been ongoing since late February 2026.
- Proof-of-concept (PoC) exploit code was published recently, raising urgency for patching.
A critical authentication bypass vulnerability in cPanel, WHM, and WP Squared, tracked as CVE-2026-41940, has been exploited in the wild for several months. Researchers first observed active exploitation attempts dating back to late February 2026, according to reports from multiple security sources including BleepingComputer and SecurityWeek.
The flaw allows attackers to bypass authentication controls, granting unauthorized access to administrative interfaces. This can lead to full compromise of hosting environments managed via cPanel and WHM, widely used web hosting control panels.
The vulnerability's exploitation is particularly concerning given the broad adoption of these platforms by hosting providers and website administrators globally. Successful attacks could result in data theft, website defacement, or the deployment of malicious code.
Security researchers disclosed that proof-of-concept (PoC) exploit code has been publicly released. The availability of this code significantly lowers the barrier for attackers to exploit the vulnerability, increasing the likelihood of widespread attacks.
cPanel, the vendor, has released security patches addressing CVE-2026-41940. Users and hosting providers are strongly advised to apply these updates immediately to mitigate ongoing risks. Delays in patching could expose systems to unauthorized access and persistent compromise.
In addition to patching, administrators should conduct thorough reviews of access logs and system activity since February to identify potential breaches. Indicators of compromise may include unexpected administrative logins or configuration changes.
This vulnerability stands out for its high severity and active exploitation timeline, underscoring the importance of timely vulnerability management in hosting environments. It also highlights the risks posed by zero-day flaws—security weaknesses exploited before patches are available.
While cPanel and WHM remain critical infrastructure components for many web services, this incident serves as a reminder of the ongoing threat landscape targeting web hosting platforms.
Organizations relying on these control panels should also consider implementing additional security measures such as multi-factor authentication (MFA) and network-level access restrictions to reduce exposure.
The incident has parallels with previous zero-day exploits in popular hosting software, where rapid exploitation followed public disclosure, emphasizing the need for proactive defense.
SecurityWeek and BleepingComputer have provided detailed technical analyses and mitigation guidance, which administrators should consult to ensure comprehensive protection.
Looking ahead, the risk remains that attackers could develop more sophisticated exploits based on the PoC code. Continuous monitoring and swift incident response capabilities are essential to limit damage.
Users uncertain about their exposure or patch status should contact their hosting providers or cPanel support channels for assistance.
The vulnerability's discovery and exploitation timeline illustrate the persistent challenge of securing complex web hosting platforms against determined adversaries.
Source URLs:
- https://www.securityweek.com/critical-cpanel-whm-vulnerability-exploited-as-zero-day-for-months/
- https://www.bleepingcomputer.com/news/security/critical-cpanel-and-whm-bug-exploited-as-a-zero-day-poc-now-available/
---
Frequently Asked Questions
What is CVE-2026-41940?
It is a critical authentication bypass vulnerability affecting cPanel, WHM, and WP Squared that allows attackers to gain unauthorized administrative access.
Am I affected if I use cPanel or WHM?
If you run unpatched versions of these platforms, you are at risk. Apply the latest security updates immediately.
Has this vulnerability been exploited in the wild?
Yes, active exploitation has been ongoing since late February 2026.
What should I do now?
Update your cPanel and WHM installations with the latest patches, review logs for suspicious activity, and consider additional security controls.
Is there a public exploit?
Yes, proof-of-concept code is publicly available, increasing the urgency to patch.
Can multi-factor authentication help?
Yes, MFA can reduce the risk of unauthorized access even if the vulnerability is exploited.
Where can I find official patches?
Visit cPanel's official website or your hosting provider's security advisories for updates.
What if I suspect my system has been compromised?
Conduct a full incident response, including isolating affected systems and restoring from clean backups.
---
What to Do Now
- Immediately update cPanel, WHM, and WP Squared to the latest patched versions.
- Audit access logs from February 2026 onward for unusual administrative activity.
- Enable multi-factor authentication on all administrative accounts.
- Restrict access to control panel interfaces via IP whitelisting or VPN.
- Monitor security advisories for any follow-up patches or mitigation recommendations.
---
How to Secure Yourself
- Keep software up to date with vendor patches.
- Use strong, unique passwords combined with MFA.
- Limit administrative access to trusted networks.
- Regularly review system and access logs.
- Employ intrusion detection systems to flag abnormal behavior.
---
2026 Update
As of mid-2026, cPanel has released multiple updates addressing CVE-2026-41940 and related vulnerabilities. Adoption rates of these patches have improved, but some environments remain exposed. Attackers continue to probe for unpatched systems, making vigilance essential. The incident has prompted broader discussions about improving security in web hosting control panels and accelerating patch deployment cycles.
Sources used for this article
securityweek.com, BleepingComputer, Multiple verified sources
