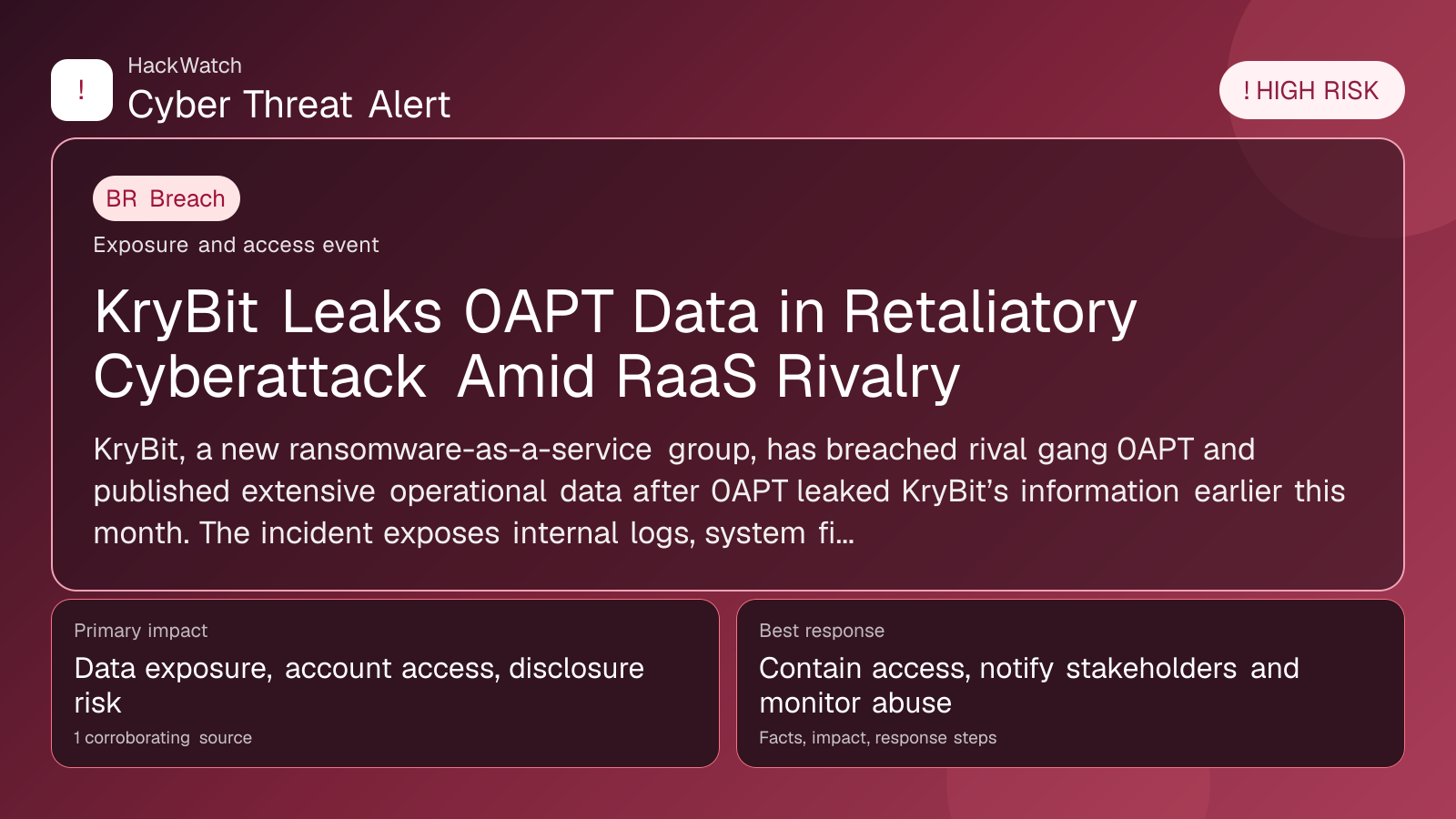
KryBit Leaks 0APT Data in Retaliatory Cyberattack Amid RaaS Rivalry
Breach coverage centered on exposed data, scope clarification and immediate containment priorities.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
KryBit, a new ransomware-as-a-service group, has breached rival gang 0APT and published extensive operational data after 0APT leaked KryBit’s information earlier this month. The incident exposes internal logs, system files, and source code, highlighting escalating conflicts within cybercrime communities.
GLOBAL, April 30, 2026, 16:38 UTC
- KryBit exposes 0APT’s operational data following prior data leak against itself
- Published information includes access logs, system files, and PHP source code
- Incident underscores growing infighting among emerging ransomware-as-a-service gangs
KryBit, a recently identified ransomware-as-a-service (RaaS) operation, has retaliated against rival group 0APT by leaking comprehensive internal data belonging to the latter. The exposed materials include 0APT’s access logs, system files, and PHP source code, according to a report by Infosecurity Magazine.
This tit-for-tat data breach follows 0APT’s earlier leak of some KryBit data earlier in April, marking a rare public feud between nascent ransomware gangs. Such conflicts can disrupt illicit operations but also risk collateral damage to victims and affiliates.
The leak reveals sensitive operational details that could allow security researchers and law enforcement to better understand 0APT’s infrastructure and tactics. Access logs may expose user activity and potential vulnerabilities within the gang’s systems.
Ransomware-as-a-service models rely on affiliate networks to distribute malware and negotiate ransoms, making operational secrecy critical. The publication of source code and system files undermines 0APT’s ability to maintain this secrecy and could lead to further disruptions.
Cybersecurity experts warn that these internal disputes may increase volatility in ransomware campaigns, potentially leading to more aggressive attacks or opportunistic targeting of victims during periods of instability.
While neither group has publicly commented on the incident, the leak has been verified by multiple sources within the cybersecurity community. Analysts note that such retaliatory leaks are uncommon but indicate shifting dynamics in the ransomware ecosystem.
Victims potentially affected by either gang’s ransomware should remain vigilant for signs of compromise and ensure backups and security measures are up to date. Organizations are advised to monitor for indicators of compromise related to both KryBit and 0APT.
The incident also highlights the importance of threat intelligence sharing and collaboration among defenders to track emerging ransomware groups and their evolving tactics.
As ransomware gangs continue to evolve, internal conflicts like this one may become more frequent, complicating efforts to predict and mitigate attacks.
Risk remains high that leaked source code and operational data could be repurposed by other threat actors, increasing the overall threat landscape.
Security teams should prioritize patching known vulnerabilities, enforcing multi-factor authentication, and conducting regular network monitoring to reduce exposure.
The KryBit-0APT feud serves as a reminder that ransomware operations are not monolithic and that internal rivalries can have real-world implications for cybersecurity defenses.
Further updates are expected as researchers analyze the leaked data and assess its impact on ongoing ransomware campaigns.
Sources used for this article
scmagazine.com
