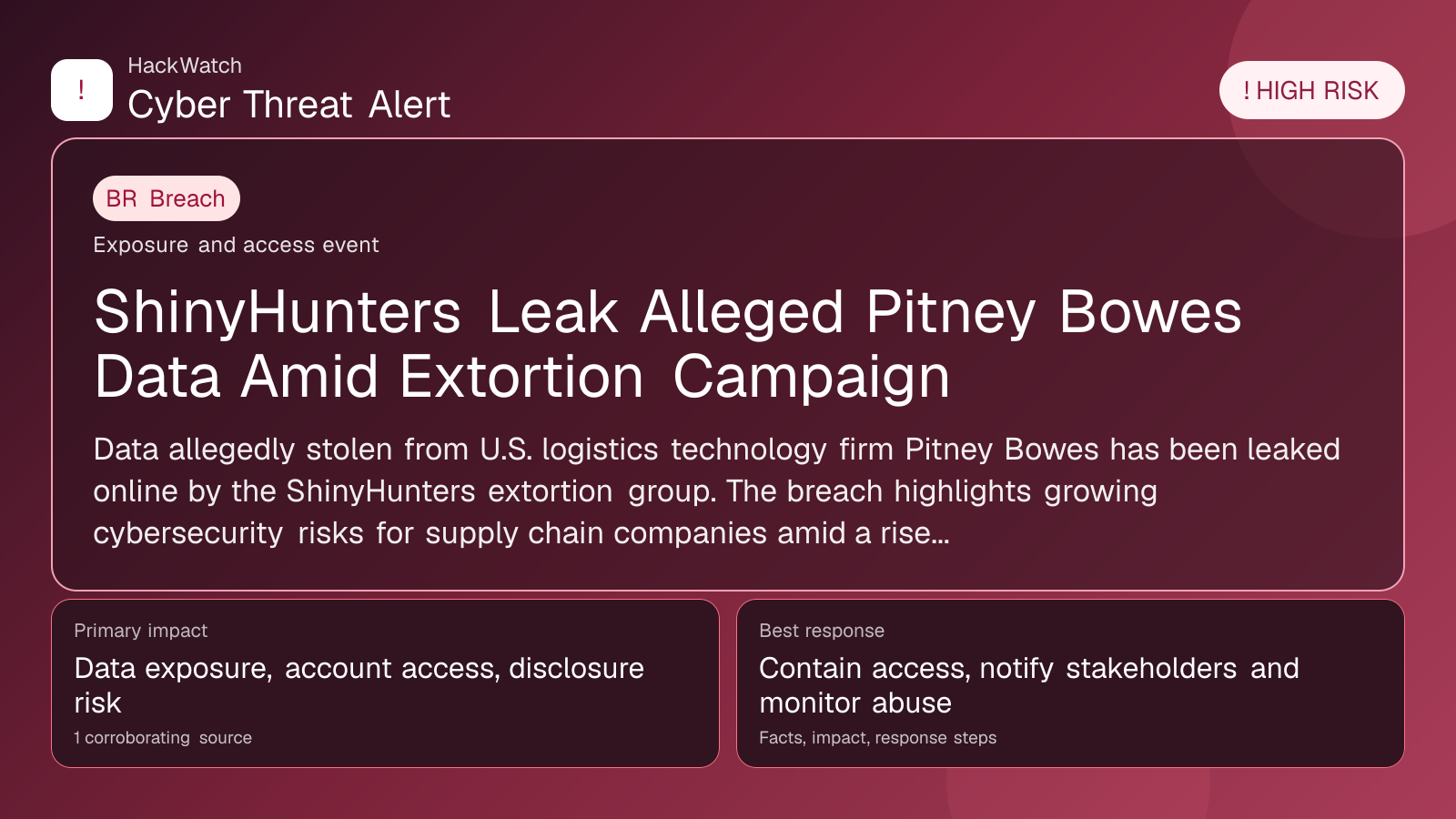
ShinyHunters Leak Alleged Pitney Bowes Data Amid Extortion Campaign
Breach coverage centered on exposed data, scope clarification and immediate containment priorities.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 for infrastructure impact, containment order and whether persistence or lateral-movement claims are supported by evidence. His administrator note is concrete: isolate the host or segment first, protect logs and network telemetry, then rebuild, rotate or patch only within the scope supported by the 1 corroborating source, the same cautious sequence he would use around managed router and server environments.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
Data allegedly stolen from U.S. logistics technology firm Pitney Bowes has been leaked online by the ShinyHunters extortion group. The breach highlights growing cybersecurity risks for supply chain companies amid a rise in ransomware and data theft attacks.
GLOBAL, April 30, 2026, 16:35 UTC
- ShinyHunters extortion group leaked data reportedly taken from Pitney Bowes
- Incident underscores rising cyber threats in logistics technology sector
- Affected parties advised to verify exposure and strengthen defenses
Pitney Bowes, a U.S.-based logistics technology provider, has reportedly suffered a data breach, with stolen information published online by the ShinyHunters extortion group. The leak appears to be part of ShinyHunters’ ongoing strategy of demanding ransom payments under threat of data disclosure.
The Register first reported the breach, citing multiple sources who confirmed that the leaked data originated from Pitney Bowes’ internal systems. ShinyHunters is known for exploiting security weaknesses and applying pressure on companies by releasing sensitive data when demands are unmet.
Pitney Bowes has not publicly detailed the scope of the breach or the specific data compromised. Given the company’s role in logistics and shipping technology, the exposure could impact clients and partners by revealing sensitive operational or customer information.
This incident comes amid an increase in cyberattacks targeting supply chain and logistics firms, sectors attractive to cybercriminals due to their critical role in global commerce. Attackers often seek to monetize breaches through ransomware or by selling stolen data on underground markets.
Security experts warn the leaked data may include customer records, shipment details, or proprietary business information. Such data can be leveraged for fraud, identity theft, or competitive intelligence. However, the exact contents have not been publicly verified.
Pitney Bowes has issued limited comment and has not disclosed mitigation measures or customer notifications at this time. Industry specialists recommend that users of Pitney Bowes services monitor for unusual activity and review cybersecurity protocols.
ShinyHunters has a track record of targeting prominent companies and releasing data when ransom demands are declined. Their attacks often exploit weak access controls or unpatched system vulnerabilities.
Experts advise logistics companies to prioritize patch management, enforce multi-factor authentication, and conduct regular security audits to reduce risk. End users should be alert to phishing attempts that may follow such breaches.
The potential for further data exposure or follow-on attacks remains until Pitney Bowes completes its investigation and remediation. Customers and partners should seek direct updates from the company.
This breach underscores the persistent cyber threat facing technology providers integral to supply chains. With attackers increasingly focusing on this sector, robust cybersecurity practices are essential to protect operations and maintain trust.
If you are a Pitney Bowes customer or partner, verify your exposure by consulting official communications or contacting the company directly. Monitor accounts closely and report suspicious activity promptly.
Implement strong, unique passwords and enable multi-factor authentication where available. Exercise caution with unsolicited requests for credentials. Ensure software and systems are kept up to date with security patches.
As of mid-2026, Pitney Bowes has begun notifying affected clients and has engaged third-party experts to conduct a forensic investigation. Continued vigilance is advised as remediation efforts progress.
For more information, see the original report by The Register and related cybersecurity advisories.
https://www.scworld.com/brief/allegedly-stolen-pitney-bowes-data-leaked-by-shinyhunters
Sources used for this article
scmagazine.com
