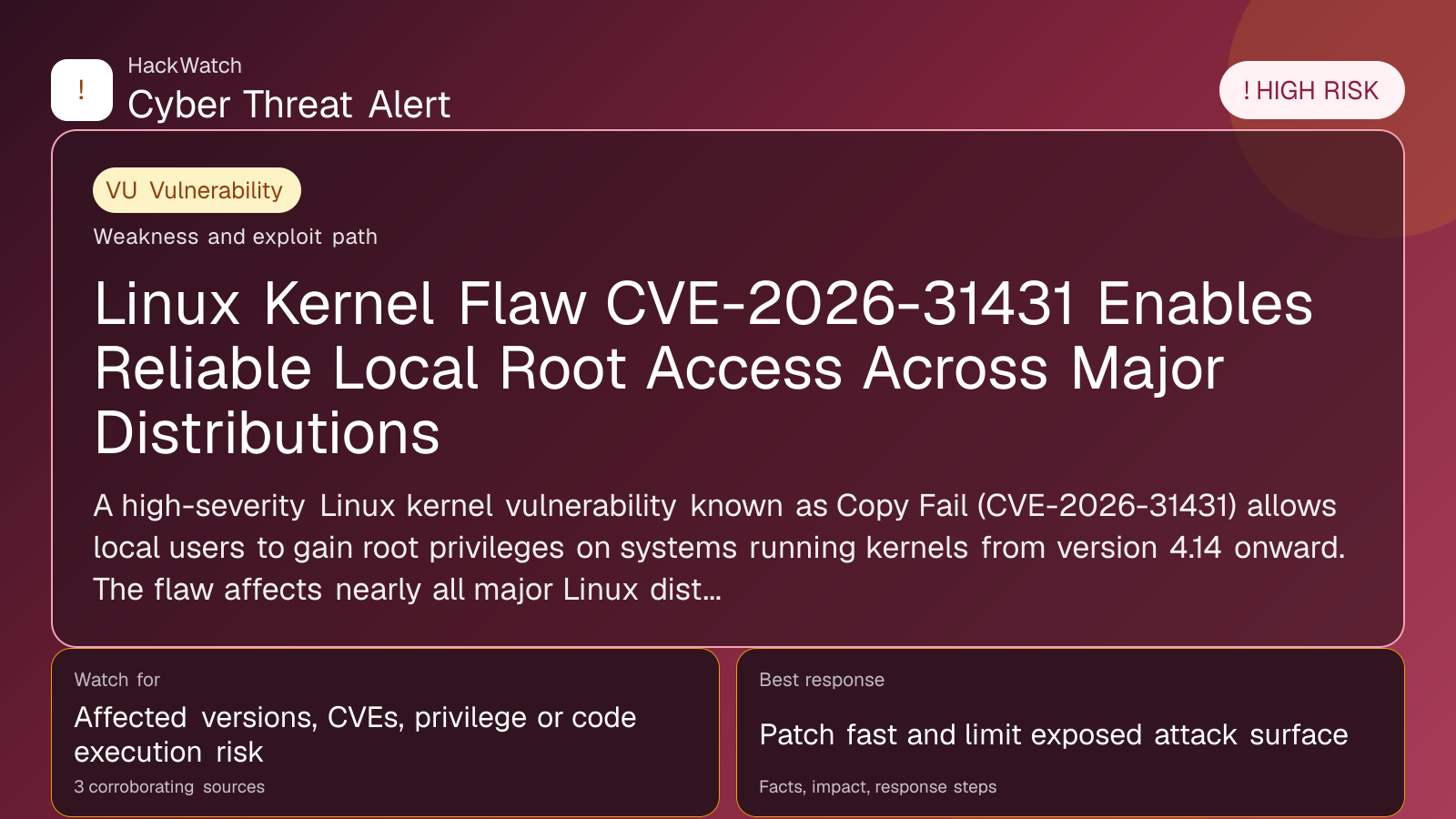
Linux Kernel Flaw CVE-2026-31431 Enables Reliable Local Root Access Across Major Distributions
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 from an administrator's point of view, checking CVE-2026-31431, CVE-2016-5195, CVE-2022-0847, CVE-2026-31431 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 3 corroborating sources supports that scope.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
A high-severity Linux kernel vulnerability known as Copy Fail (CVE-2026-31431) allows local users to gain root privileges on systems running kernels from version 4.14 onward. The flaw affects nearly all major Linux distributions, with patches available but not universally deployed. The exploit bypasses disk forensics by modifying cached file copies in memory, posing significant risks to multi-tenant and containerized environments.
GLOBAL, April 30, 2026, 17:24 UTC
- CVE-2026-31431 is a local privilege escalation vulnerability affecting Linux kernels since 2017.
- Exploit works reliably without race conditions or write constraints, unlike previous flaws Dirty Cow and Dirty Pipe.
- Patches exist but some major distributions remain vulnerable, raising concerns for cloud and container users.
A critical Linux kernel vulnerability dubbed Copy Fail (CVE-2026-31431) allows any local user to escalate privileges to root on systems running kernel versions 4.14 and later. The flaw, publicly disclosed on April 29, 2026, affects virtually every major Linux distribution released since 2017.
Discovered by researcher Taeyang Lee of Theori and reported to the Linux kernel security team in late March, the vulnerability exploits a logical bug in the kernel's cryptographic subsystem. Unlike memory corruption bugs, Copy Fail manipulates the kernel's page cache — a memory-resident copy of files — without altering the underlying file on disk.
This means attackers can modify privileged binaries in memory to gain root access, while standard disk forensics would show no changes. The altered cache resets after a reboot or memory pressure, but the exploit can be executed repeatedly to maintain elevated privileges.
Copy Fail draws direct comparisons to Dirty Cow (CVE-2016-5195) and Dirty Pipe (CVE-2022-0847), two infamous Linux kernel privilege escalation vulnerabilities. However, Copy Fail reportedly works consistently without relying on race conditions or constraints on where data can be written within a file, making it more reliable and easier to exploit.
The vulnerability carries a CVSSv3 score of 7.8, indicating high severity. It poses the greatest risk in environments where multiple users or workloads share a Linux kernel, such as cloud infrastructure, multi-tenant servers, container clusters, and CI/CD pipelines running untrusted code. Because the exploit targets the shared page cache, it can cross container boundaries, increasing the attack surface.
Single-user systems face a lower risk since an attacker would already require local access. Still, the presence of a public proof-of-concept exploit on GitHub raises concerns about widespread exploitation attempts.
As of April 30, major distributions are at varying stages of patch deployment. Ubuntu, SUSE, Red Hat, and Arch Linux are actively patching or have patched affected kernels. Debian and Amazon Linux remain vulnerable, exposing users to potential compromise.
System administrators are urged to verify kernel versions and apply vendor patches promptly. Failing to patch leaves systems exposed to privilege escalation attacks that can undermine security controls and data integrity.
The flaw's discovery highlights the ongoing risks posed by logical bugs in complex kernel subsystems, which can be as dangerous as memory corruption vulnerabilities. Theori's use of AI-assisted security scanning tools like Xint Code underscores the growing role of automated methods in uncovering subtle security flaws.
Organizations relying on Linux for critical workloads should prioritize patching and consider additional mitigations such as restricting local user access and monitoring for unusual privilege escalations.
Looking ahead, the persistence of such vulnerabilities across nearly a decade of kernel releases signals the need for enhanced code auditing and security testing in open-source projects.
Risk remains that some environments may delay patching due to compatibility concerns or operational constraints, prolonging exposure. Attackers may also develop variants that evade detection or exploit related kernel features.
Users should monitor vendor advisories closely and validate that kernel updates are applied. Regular system reboots may temporarily clear the altered page cache but do not eliminate the underlying vulnerability.
For detailed technical analysis, refer to the Xint Code blog and Theori's disclosures.
https://securityboulevard.com/2026/04/linux-kernel-flaw-copy-fail-exposes-widespread-privilege-escalation-risk/
https://securityboulevard.com/2026/04/copy-fail-cve-2026-31431-frequently-asked-questions-about-linux-kernel-privilege-escalation-vulnerability/
---
Frequently Asked Questions
What is CVE-2026-31431?
A local privilege escalation vulnerability in the Linux kernel's cryptographic subsystem affecting kernels 4.14 and later.
Who is at risk?
Systems with multiple users or workloads sharing a Linux kernel, especially cloud, container, and multi-tenant environments.
Is there a patch?
Yes, patches are available and being deployed by major distributions, though some remain vulnerable.
How does the exploit work?
By modifying the kernel's page cache in memory, attackers can alter privileged binaries without changing files on disk.
How does Copy Fail compare to Dirty Cow and Dirty Pipe?
Copy Fail is more reliable, does not rely on race conditions, and has fewer constraints on write positions.
Can a reboot fix the issue?
Rebooting clears the altered page cache but does not patch the vulnerability.
Is there a public exploit?
Yes, a proof-of-concept is publicly available on GitHub.
Which distributions are vulnerable?
Virtually all with kernels 4.14+, including Debian and Amazon Linux (currently unpatched).
What should users do now?
Apply vendor patches immediately and restrict local access where possible.
How can users secure themselves?
Monitor for unusual privilege escalations, limit untrusted code execution, and keep systems updated.
---
What To Do Now
- Identify Linux kernel version: `uname -r`.
- Check vendor advisories for patch availability.
- Apply kernel updates without delay.
- Limit local user access on shared systems.
- Monitor system logs for suspicious activity.
- Reboot systems after patching to clear cached exploits.
---
How To Secure Yourself
- Restrict local user permissions and access.
- Avoid running untrusted code on shared kernels.
- Use container isolation best practices.
- Employ intrusion detection systems to spot privilege escalations.
- Regularly audit kernel and system updates.
---
2026 Update
As of mid-2026, patch adoption has improved but some distributions lag behind. Researchers continue to monitor for exploit variants. The Linux community is increasing focus on logical bug detection using AI-assisted tools. Users are advised to maintain vigilance and keep systems current to mitigate evolving risks.
Sources used for this article
securityweek.com, securityboulevard.com
- https://www.securityweek.com/copy-fail-logic-flaw-in-linux-kernel-enables-system-takeover/
- https://securityboulevard.com/2026/04/linux-kernel-flaw-copy-fail-exposes-widespread-privilege-escalation-risk/
- https://securityboulevard.com/2026/04/copy-fail-cve-2026-31431-frequently-asked-questions-about-linux-kernel-privilege-escalation-vulnerability/
