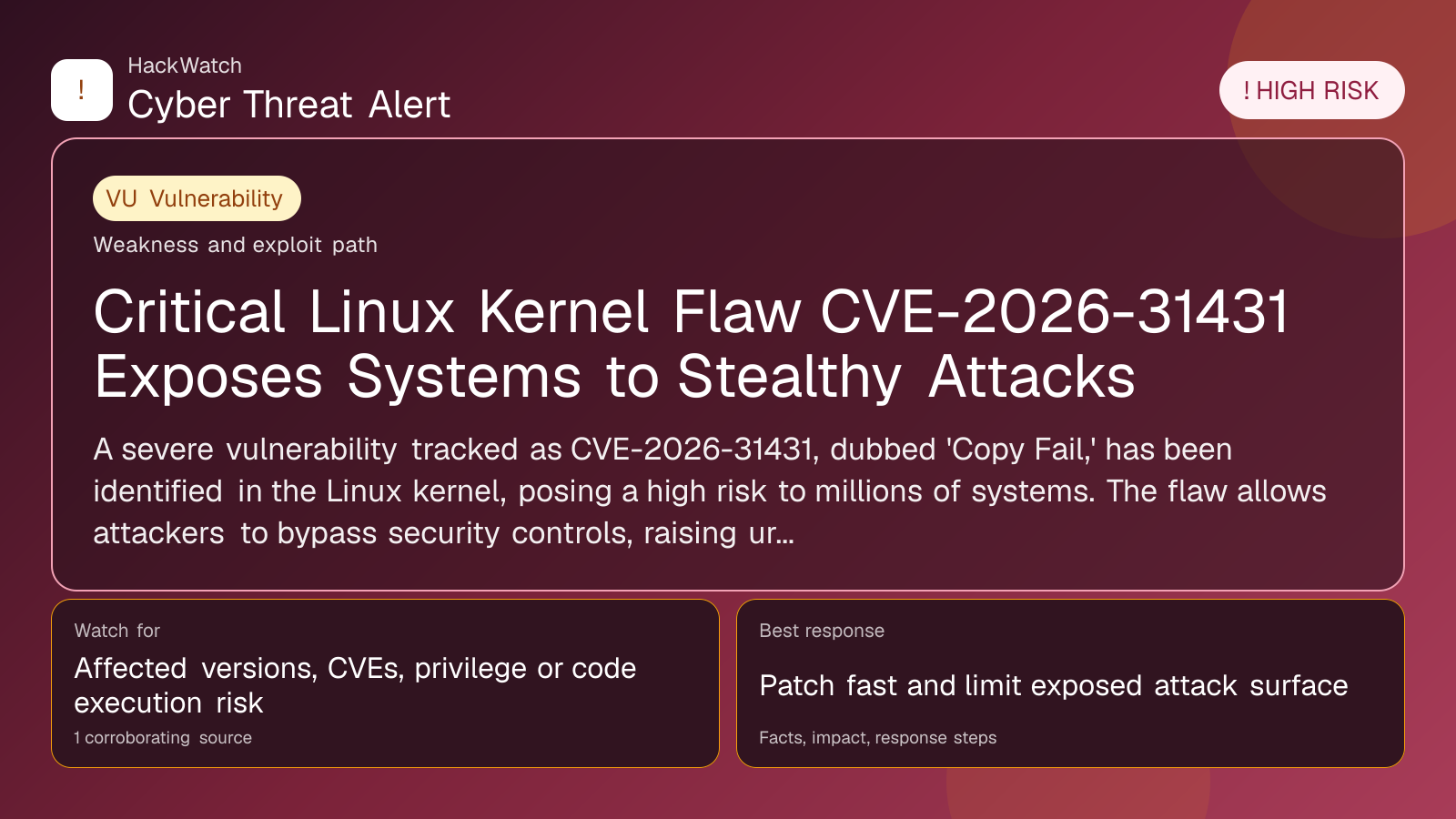
Critical Linux Kernel Flaw CVE-2026-31431 Exposes Systems to Stealthy Attacks
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 from an administrator's point of view, checking CVE-2026-31431 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 1 corroborating source supports that scope.
Review our editorial policy or send corrections to [email protected].
Mitigation available. Mitigation guidance or a workaround is available, but defenders should still verify rollout status and exposure.
A severe vulnerability tracked as CVE-2026-31431, dubbed 'Copy Fail,' has been identified in the Linux kernel, posing a high risk to millions of systems. The flaw allows attackers to bypass security controls, raising urgent concerns for enterprises and individual users alike.
GLOBAL, April 30, 2026, 15:02 UTC
- CVE-2026-31431 is a high-severity bug in the Linux kernel impacting core system security.
- The vulnerability enables attackers to bypass standard safeguards, potentially leading to data breaches or system compromise.
- Immediate patching and mitigation steps are recommended to reduce exposure.
A critical security vulnerability, CVE-2026-31431, known as "Copy Fail," has been uncovered in the Linux kernel, one of the foundational components of countless computing environments. Researchers describe it as one of the most insidious bugs discovered in recent years, due to its stealthy nature and potential impact.
Linux powers everything from cloud infrastructure and enterprise servers to personal devices, making this flaw particularly consequential. The bug allows threat actors to circumvent kernel-level protections, which could facilitate unauthorized access or privilege escalation.
The vulnerability stems from a flaw in how the kernel handles certain memory copy operations, which attackers can exploit to bypass security checks. This undermines the integrity of the operating system’s core defenses, increasing the risk of data theft, ransomware deployment, or system takeover.
Security teams and system administrators are urged to prioritize patching. While official updates are being rolled out, some environments may face delays due to complex dependencies or legacy hardware constraints.
The timing is critical as threat actors are known to exploit such vulnerabilities rapidly after disclosure. Given the widespread use of Linux in critical infrastructure and cloud services, the risk of large-scale attacks remains high.
This flaw arrives amid a broader surge in cybercrime activities, including phishing campaigns, underground marketplaces selling stolen credit card data, and sophisticated ransomware groups. The interconnected threats underscore the need for heightened vigilance and layered defenses.
Users should verify their Linux distributions’ security advisories and apply updates without delay. Organizations should also review their intrusion detection systems and monitor for unusual kernel-level activity that might indicate exploitation attempts.
Experts warn that failure to act swiftly could result in significant operational disruptions and data loss. The covert nature of the bug means attacks may go unnoticed for extended periods, compounding damage.
In parallel, artificial intelligence tools used for cybersecurity are evolving, but recent incidents reveal their limitations, emphasizing human oversight remains essential.
Looking ahead, the cybersecurity community anticipates further research into this vulnerability and related kernel issues, with ongoing efforts to harden Linux against emerging threats.
Users and administrators can reduce risk by implementing strict access controls, isolating critical workloads, and maintaining comprehensive backups.
The discovery of CVE-2026-31431 highlights the persistent challenges in securing open-source software that underpins modern computing. Vigilance and prompt response remain the best defenses.
For detailed mitigation guidance and patch links, consult your Linux vendor’s security pages or trusted cybersecurity sources.
---
Frequently Asked Questions
What is CVE-2026-31431?
It is a security flaw in the Linux kernel that allows attackers to bypass memory copy protections, potentially leading to unauthorized system access.
Who is affected?
Any system running vulnerable Linux kernel versions, including servers, desktops, and embedded devices.
How can I check if my system is vulnerable?
Review your Linux distribution’s security advisories and verify kernel version against published vulnerable ranges.
What should I do now?
Apply available patches immediately and monitor system logs for suspicious activity.
Can this vulnerability be exploited remotely?
While primarily local, exploitation could be combined with other vulnerabilities for remote attacks.
Are there any workarounds if patches cannot be applied immediately?
Limiting user privileges and disabling unnecessary services can reduce risk temporarily.
How does this relate to other recent cyber threats?
It adds to a growing list of vulnerabilities exploited by cybercriminals, increasing the overall threat landscape.
Will AI tools help detect exploitation?
AI can assist but is not foolproof; human analysis remains critical.
What is the long-term outlook?
Ongoing kernel hardening and community vigilance are expected to mitigate similar risks in the future.
---
What to Do Now
- Identify and inventory all Linux systems in your environment.
- Check for and apply official patches related to CVE-2026-31431.
- Increase monitoring for unusual kernel or memory-related activity.
- Restrict user permissions and network access where feasible.
- Backup critical data and verify recovery procedures.
How to Secure Yourself
- Keep your operating system and software up to date.
- Use strong authentication and limit administrative access.
- Employ intrusion detection and prevention tools.
- Educate users about phishing and social engineering risks.
- Regularly audit system logs and security configurations.
2026 Update
By late 2026, Linux kernel maintainers have released multiple patches addressing CVE-2026-31431 and related issues. Adoption rates vary, and some legacy systems remain exposed. Continuous vigilance and patch management remain essential to prevent exploitation.
---
Source: https://www.redhotcyber.com/
Sources used for this article
redhotcyber.com
