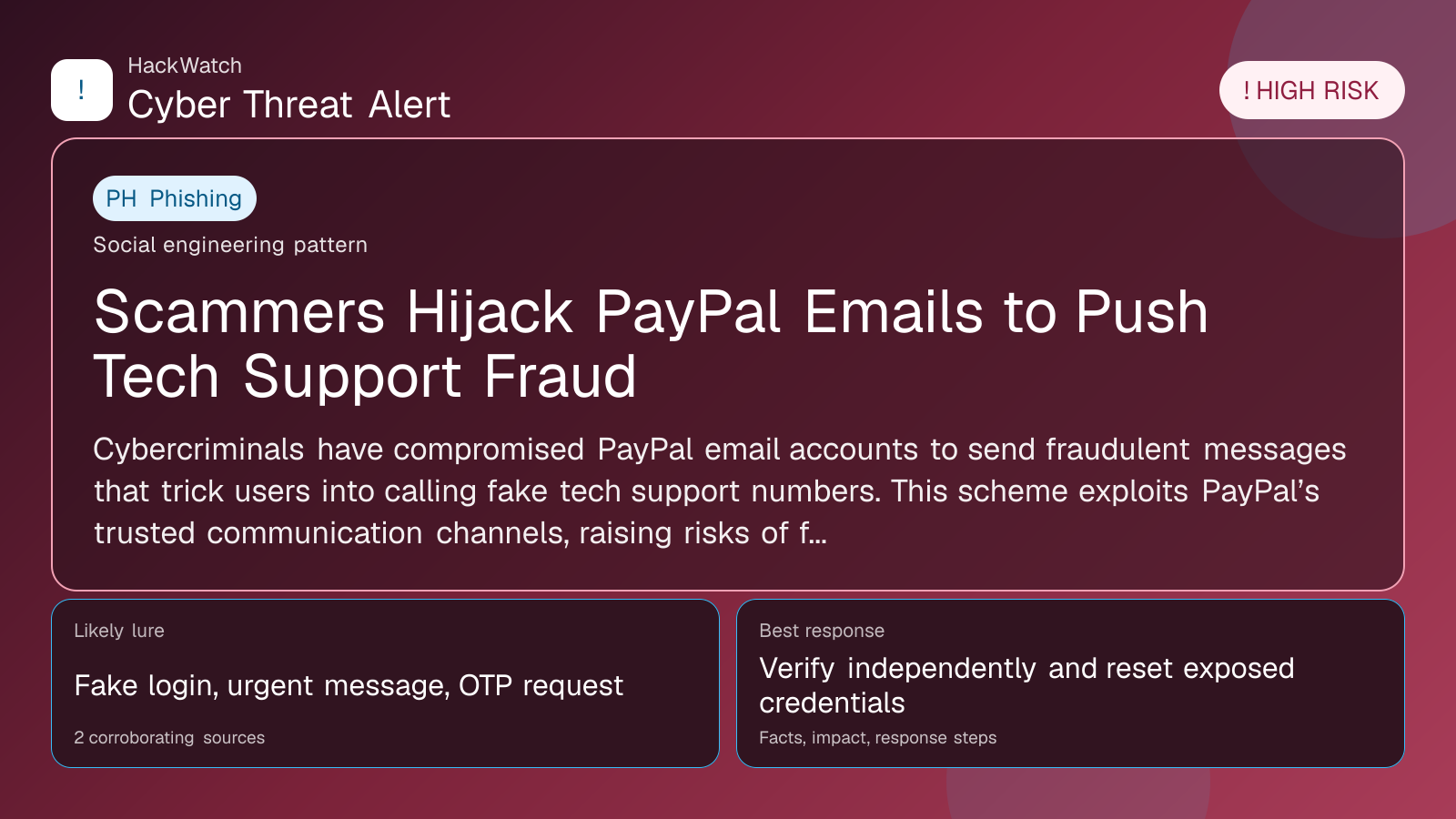
Scammers Hijack PayPal Emails to Push Tech Support Fraud
Verification-lure coverage focused on fake messages, cloned pages and account defense steps.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 2 corroborating sources.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
Cybercriminals have compromised PayPal email accounts to send fraudulent messages that trick users into calling fake tech support numbers. This scheme exploits PayPal’s trusted communication channels, raising risks of financial theft and identity fraud.
GLOBAL, April 30, 2026, 21:42 UTC
Cybersecurity researchers have uncovered a surge in scams using hijacked PayPal email accounts to distribute fake tech support messages. These emails prompt recipients to call fraudulent support lines, where attackers attempt to steal sensitive data or money.
PayPal’s role as a widely trusted online payment service makes this tactic particularly effective. By hijacking legitimate PayPal email addresses, scammers bypass spam filters and increase the chance users will engage with the messages.
The scam emails typically warn of account problems or security alerts and instruct recipients to call specific phone numbers. Once contacted, fraudsters impersonate PayPal agents to extract passwords, payment information, or persuade victims to install remote access tools.
Analysis from Malwarebytes and Security Boulevard highlights multiple incidents linked to breaches in PayPal’s email systems or vulnerabilities in third-party services handling PayPal communications.
Victims face risks including unauthorized account access, financial loss, and exposure of personal details. The attackers often pressure targets into quick compliance, exploiting trust in PayPal’s brand.
PayPal has not disclosed the full extent of the breach but urges users to verify communications through official channels only. Security experts advise ignoring unsolicited emails demanding urgent action or phone contact.
To protect themselves, users should enable two-factor authentication, update passwords regularly, and monitor account activity closely. Businesses using PayPal should review email security protocols and consider enhanced authentication.
This incident underscores the difficulty of securing email systems tied to major platforms, with attackers adapting to trusted brands to evade detection.
Users should be wary of unexpected PayPal emails, especially those urging immediate phone calls. Confirming messages via PayPal’s official website or app remains the safest approach.
Similar scams have targeted other major providers like Microsoft and Apple, reflecting a broader trend of tech support fraud exploiting brand impersonation.
There is a risk attackers may escalate these campaigns or integrate malware delivery, increasing potential damage. Prompt vigilance and adherence to security best practices are crucial.
Users suspecting exposure should check recent account activity, change passwords, and report suspicious emails to PayPal’s fraud team.
In brief, the compromise of PayPal email accounts to spread tech support scams poses a significant threat to users’ financial and personal security. Vigilance and proactive security measures are vital to limit harm.
For more information, see reports by Malwarebytes and Security Boulevard:
- https://www.malwarebytes.com/blog/news/2026/04/more-paypal-emails-hijacked-to-deliver-tech-support-scams
- https://securityboulevard.com/2026/04/more-paypal-emails-hijacked-to-deliver-tech-support-scams/
Sources used for this article
blog.malwarebytes.com, securityboulevard.com, Multiple verified sources
