Misconfigured Hacker Server Exposes 345,000 Stolen Credit Cards
Breach coverage centered on exposed data, scope clarification and immediate containment priorities.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
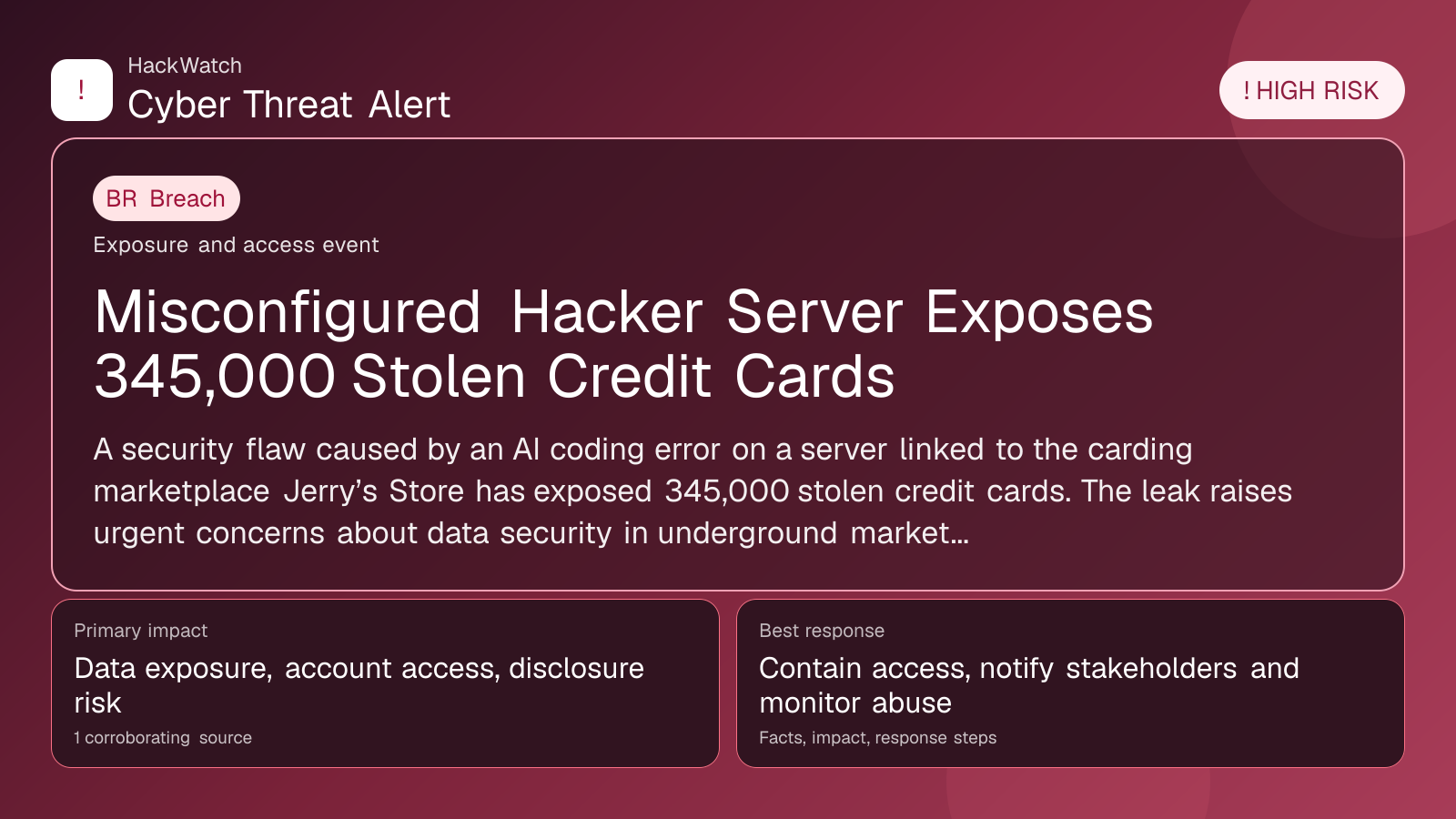
A security flaw caused by an AI coding error on a server linked to the carding marketplace Jerry’s Store has exposed 345,000 stolen credit cards. The leak raises urgent concerns about data security in underground marketplaces and the risks posed to consumers.
GLOBAL, April 30, 2026, 19:23 UTC
- Misconfigured server tied to Jerry’s Store leaks 345,000 stolen credit cards
- AI coding error identified as root cause of security flaw
- Data exposure highlights ongoing risks from underground carding marketplaces
A misconfigured server operated by hackers connected to the carding marketplace Jerry’s Store has exposed 345,000 stolen credit card records, researchers said. The leak resulted from an AI coding error that introduced a critical security flaw, leaving sensitive payment data accessible online.
The exposure is significant given the scale of stolen financial information involved. Carding marketplaces like Jerry’s Store facilitate the sale and trade of compromised payment credentials, fueling fraud and identity theft worldwide. This latest leak underscores how operational mistakes can amplify risks even within illicit networks.
The server’s misconfiguration meant that the data was not properly secured or encrypted, allowing anyone with the server address to access the full cache of stolen cards. Security analysts noted that the AI code responsible for managing the server’s access controls failed to implement basic safeguards.
While the exact timeline of the leak remains unclear, the vulnerability was discovered and reported by independent cybersecurity researchers who monitor underground marketplaces. The flaw was promptly closed after disclosure, but the stolen data had already been exposed for an unknown period.
Consumers whose credit card information was compromised face heightened risks of fraudulent charges and identity theft. Banks and payment processors may need to issue new cards and monitor accounts closely to mitigate damage. Experts advise cardholders to review statements and report suspicious activity immediately.
This incident also highlights the persistent challenge law enforcement faces in disrupting illicit carding operations. Even when marketplaces are taken down, residual infrastructure such as misconfigured servers can continue to leak sensitive data.
The use of AI in managing underground hacking infrastructure introduces new vulnerabilities. In this case, the AI coding error directly contributed to the exposure, suggesting that automated systems require rigorous testing and oversight even in criminal contexts.
Security firms recommend that organizations and individuals remain vigilant about the potential fallout from such leaks. Monitoring dark web forums and marketplaces can provide early warnings about compromised data.
In response to this event, payment networks may accelerate adoption of advanced fraud detection and tokenization technologies to reduce reliance on static card data.
Given the scale of the breach, affected users should consider enrolling in credit monitoring services and freezing their credit reports to prevent unauthorized account openings.
While the server has been secured, the incident serves as a stark reminder that stolen data can proliferate widely once exposed, complicating efforts to contain fraud.
The leak was first reported by HackRead.com, which provided detailed analysis of the server misconfiguration and its implications (https://hackread.com/misconfigured-server-hackers-leak-stolen-credit-cards/).
Future investigations may reveal additional compromised data or related infrastructure vulnerabilities tied to Jerry’s Store or similar marketplaces.
The ongoing evolution of cybercrime infrastructure, including the use of AI, demands continuous adaptation by cybersecurity professionals and law enforcement agencies.
Users concerned about exposure should contact their banks immediately and remain alert for phishing attempts exploiting the breach.
Sources used for this article
hackread.com
