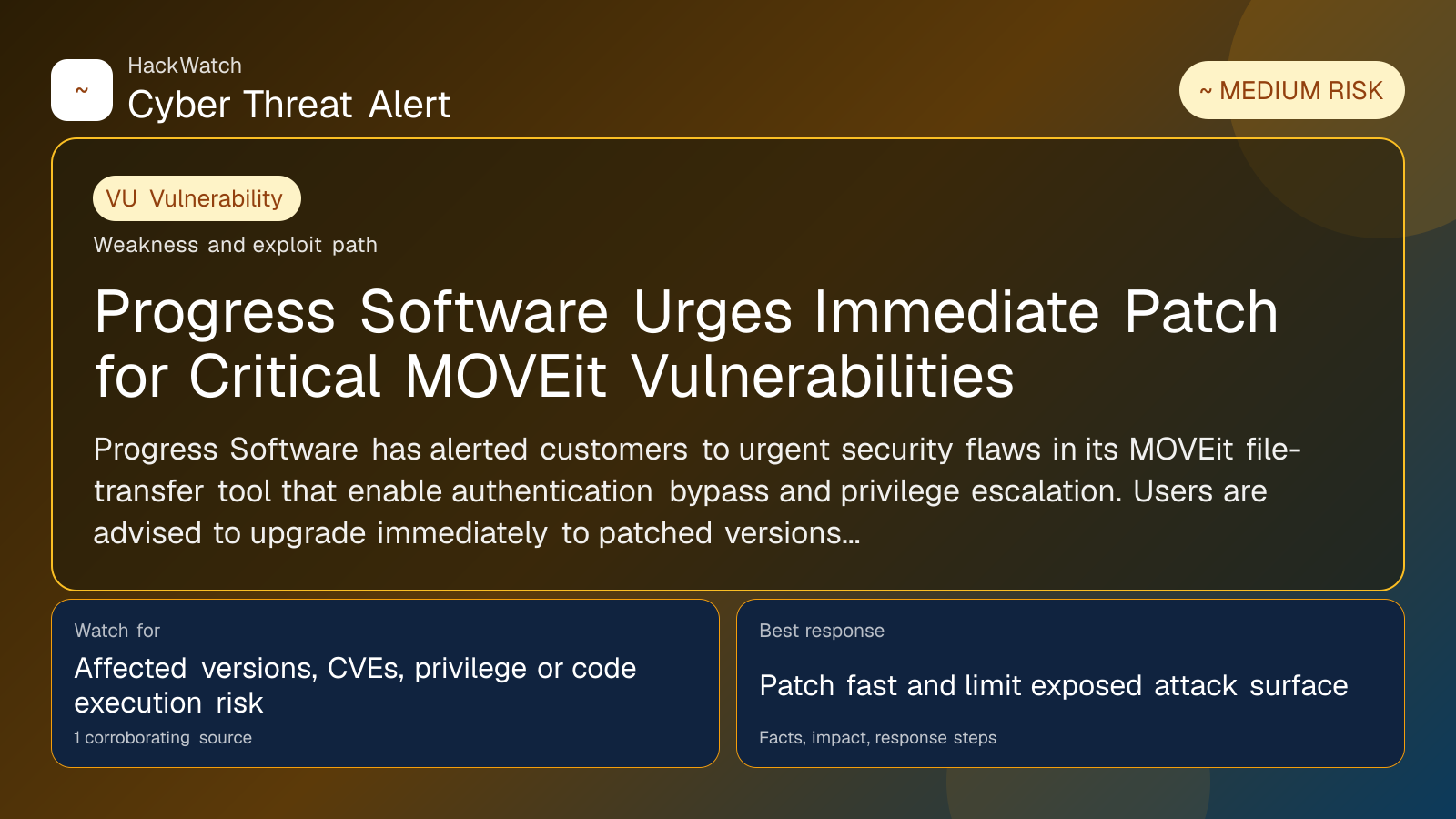
Progress Software Urges Immediate Patch for Critical MOVEit Vulnerabilities
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
Progress Software has alerted customers to urgent security flaws in its MOVEit file-transfer tool that enable authentication bypass and privilege escalation. Users are advised to upgrade immediately to patched versions to mitigate risk.
GLOBAL, May 4, 2026, 15:15 UTC
Progress Software has issued a critical warning to users of its MOVEit file-transfer solution following the discovery of serious security vulnerabilities. The company urged customers to upgrade to the latest versions without delay to address these flaws.
The newly identified vulnerabilities allow attackers to bypass authentication controls and escalate privileges within MOVEit environments. This could enable unauthorized access to sensitive data or administrative functions, raising the risk of data breaches or further compromise.
MOVEit is widely used by enterprises for secure file transfers, making these vulnerabilities particularly concerning. Exploitation could disrupt operations or expose confidential information, underscoring the urgency of applying patches.
Progress Software did not disclose technical details about the flaws, citing security considerations. However, the company confirmed that fixed versions are now available and strongly recommended immediate deployment.
The timing of the alert comes amid increased scrutiny of file-transfer platforms, which have been targeted in recent cyberattacks due to their role in moving critical data.
Security researchers emphasize that organizations running MOVEit should prioritize patching to reduce exposure. Delays could leave systems vulnerable to attackers exploiting the authentication bypass and privilege escalation bugs.
While no widespread exploitation has been reported so far, the medium risk level assigned to these vulnerabilities reflects the potential impact if left unaddressed.
Progress Software's advisory includes guidance on verifying patch installation and monitoring for suspicious activity. Customers are advised to review access logs and tighten account controls as precautionary measures.
The company joins other vendors who have recently accelerated vulnerability disclosures and patch rollouts in response to evolving threat landscapes targeting enterprise software.
For now, the best defense remains swift patch management and vigilant monitoring to detect any anomalous behavior linked to MOVEit deployments.
Users can find the updated MOVEit versions and detailed remediation instructions on Progress Software’s official website.
This incident highlights the ongoing challenges organizations face in securing file-transfer tools, which remain attractive targets for attackers seeking to infiltrate networks or exfiltrate data.
Enterprises should also consider multi-factor authentication and network segmentation to further limit the impact of any potential compromise.
The MOVEit vulnerabilities serve as a reminder that even trusted infrastructure components require continuous security oversight to prevent exploitation.
Source: https://www.cybersecuritydive.com/news/moveit-vulnerabilities-authentication-bypass-privilege-escalation/819187/
Sources used for this article
cybersecuritydive.com
