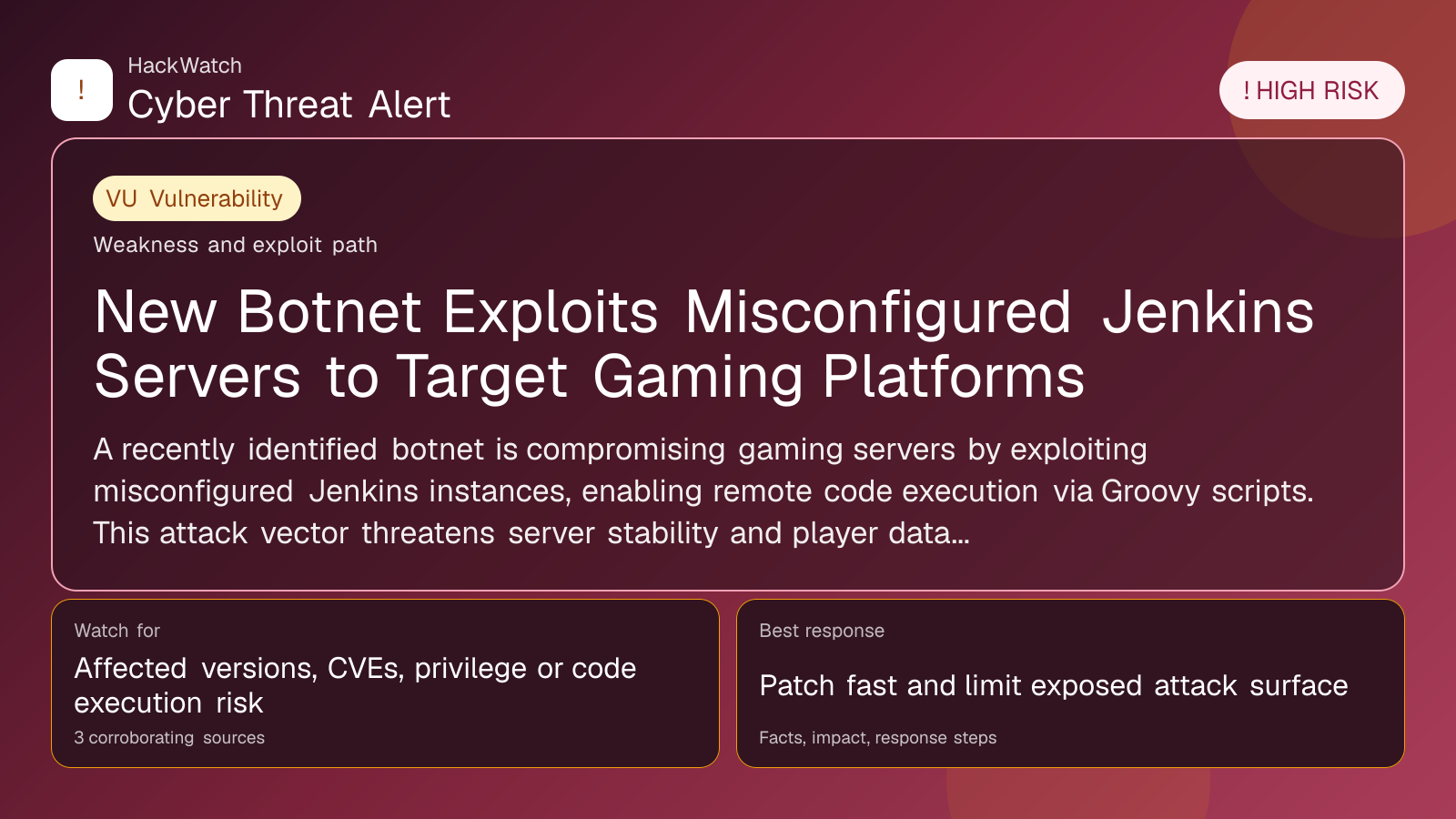
New Botnet Exploits Misconfigured Jenkins Servers to Target Gaming Platforms
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 3 corroborating sources.
Review our editorial policy or send corrections to [email protected].
Mitigation available. Mitigation guidance or a workaround is available, but defenders should still verify rollout status and exposure.
A recently identified botnet is compromising gaming servers by exploiting misconfigured Jenkins instances, enabling remote code execution via Groovy scripts. This attack vector threatens server stability and player data integrity, urging immediate configuration reviews and patching among gaming operators.
GLOBAL, May 4, 2026, 16:22 UTC
A new botnet has emerged, targeting gaming servers by exploiting misconfigured Jenkins automation servers. Attackers gain initial access through the Jenkins scriptText endpoint, executing malicious Groovy scripts to achieve remote code execution (RCE).
Jenkins, a popular open-source automation server, is widely used for continuous integration and deployment. Misconfigurations, particularly those exposing the scriptText endpoint without proper authentication, allow attackers to run arbitrary code remotely.
This vector is especially concerning for gaming platforms that rely on Jenkins for development and deployment pipelines. Compromised servers risk unauthorized access, data theft, and disruption of gaming services, which can impact millions of users.
Security researchers first identified the botnet exploiting this vulnerability on gaming infrastructure, highlighting the attackers’ focus on high-value targets with potentially lax Jenkins configurations.
The botnet’s use of Groovy scripts enables flexible and stealthy payload delivery, complicating detection and mitigation efforts. Once inside, attackers can deploy additional malware, mine cryptocurrency, or enlist servers into broader botnet operations.
Operators of gaming servers are urged to audit Jenkins configurations immediately, ensuring that scriptText endpoints are secured behind strong authentication or disabled if unnecessary. Applying the latest Jenkins security patches is critical to closing this attack vector.
The incident underscores the broader risk posed by exposed automation tools in critical infrastructure, where misconfigurations can serve as entry points for sophisticated cyber threats.
While no widespread breaches have been publicly reported yet, the high-risk nature of this botnet demands urgent attention from gaming companies and DevOps teams alike.
Experts recommend monitoring network traffic for unusual Jenkins activity and implementing strict access controls. Regular security assessments of CI/CD pipelines can help detect and prevent similar intrusions.
The gaming industry, often targeted for its valuable user data and real-time revenue streams, remains a lucrative target for cybercriminals leveraging automation server vulnerabilities.
This development follows a pattern of attackers exploiting overlooked or misconfigured developer tools, emphasizing the need for comprehensive security hygiene beyond traditional perimeter defenses.
Gaming operators should also review backup and incident response plans to minimize disruption in case of compromise.
The evolving threat landscape requires continuous vigilance as attackers adapt to new opportunities presented by modern development environments.
Source: https://www.scworld.com/brief/new-botnet-targets-gaming-servers-via-misconfigured-jenkins
Sources used for this article
gbhackers.com, cybersecuritynews.com, scmagazine.com
