Identity Remains Prime Target as Endpoint and Cloud Threats Expand
Verification-lure coverage focused on fake messages, cloned pages and account defense steps.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
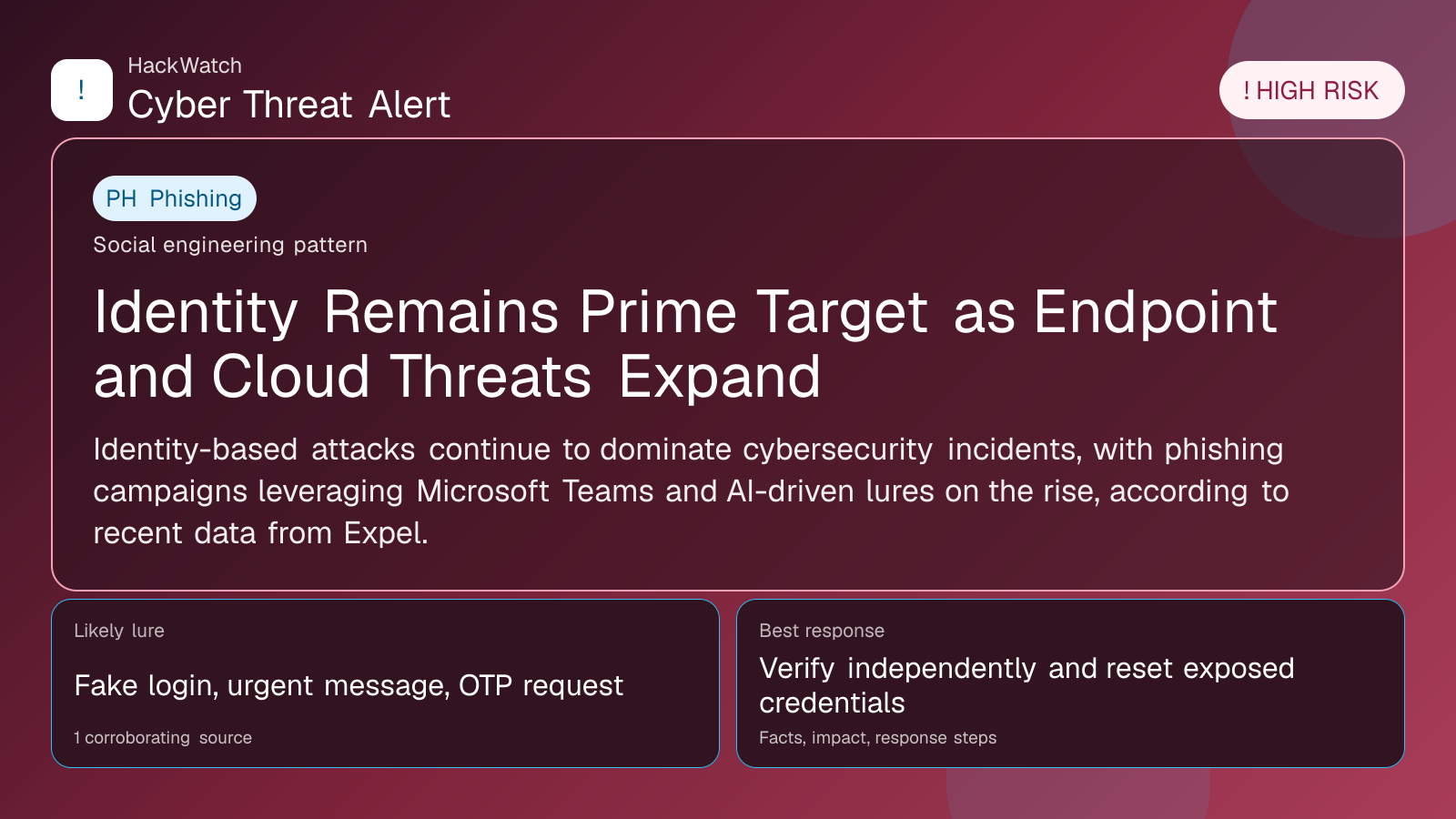
Identity-based attacks continue to dominate cybersecurity incidents, with phishing campaigns leveraging Microsoft Teams and AI-driven lures on the rise, according to recent data from Expel.
LONDON, May 4, 2026, 15:41 UTC
Identity remains the most targeted attack surface amid a surge in endpoint and cloud security incidents, cybersecurity firm Expel reported on Monday. The firm highlighted a growing trend of phishing attacks exploiting Microsoft Teams and artificial intelligence (AI) based lures.
Expel's latest data shows that threat actors increasingly focus on compromising user identities to gain access to corporate networks. This shift coincides with the widespread adoption of cloud services and remote collaboration tools, which have broadened the attack landscape.
The rise in Microsoft Teams phishing is particularly notable. Attackers craft convincing messages within the platform to trick users into revealing credentials or clicking malicious links. This method leverages the trust users place in internal communication channels, making detection harder for traditional security controls.
AI-powered lures represent another emerging vector. Cybercriminals use AI to generate tailored phishing content that mimics legitimate communications, increasing the likelihood of successful breaches. These sophisticated tactics complicate defenses that rely on pattern recognition and generic filters.
The expansion of endpoint incidents further underscores the challenges in securing identity. Devices connecting to corporate environments often serve as entry points for attackers once credentials are compromised. Endpoint security solutions must adapt to detect subtle signs of identity misuse alongside malware or ransomware.
Cloud environments also remain vulnerable as attackers exploit misconfigurations and weak identity controls. The integration of identity and access management (IAM) tools is critical to limiting exposure and enforcing least-privilege access policies.
Organizations are urged to strengthen multi-factor authentication (MFA) across all access points, including collaboration platforms like Teams. Regular user training on recognizing phishing attempts, especially those leveraging AI-generated content, is essential to reduce risk.
Expel's findings align with broader industry observations that identity theft and account compromise continue to drive security incidents. As attackers diversify their methods, defenders must prioritize identity protection as a foundational element of cybersecurity strategies.
The evolving threat landscape highlights the need for continuous monitoring and rapid response capabilities. Security teams should integrate behavioral analytics and anomaly detection to identify unusual access patterns indicative of identity compromise.
Failure to address these identity-centric threats could lead to significant data breaches, operational disruptions, and financial losses. The complexity of attacks demands a layered defense approach combining technology, process, and user awareness.
For users, vigilance remains key. Verifying unexpected requests within collaboration tools and reporting suspicious activity promptly can help mitigate the impact of phishing campaigns.
Expel's report serves as a timely reminder that as digital workspaces evolve, so do the tactics of cyber adversaries. Identity security must remain at the forefront of organizational defenses to counteract the expanding threat surface.
https://securitybrief.co.uk/story/identity-stays-top-attack-surface-as-threats-broaden
Sources used for this article
securitybrief.co.uk
