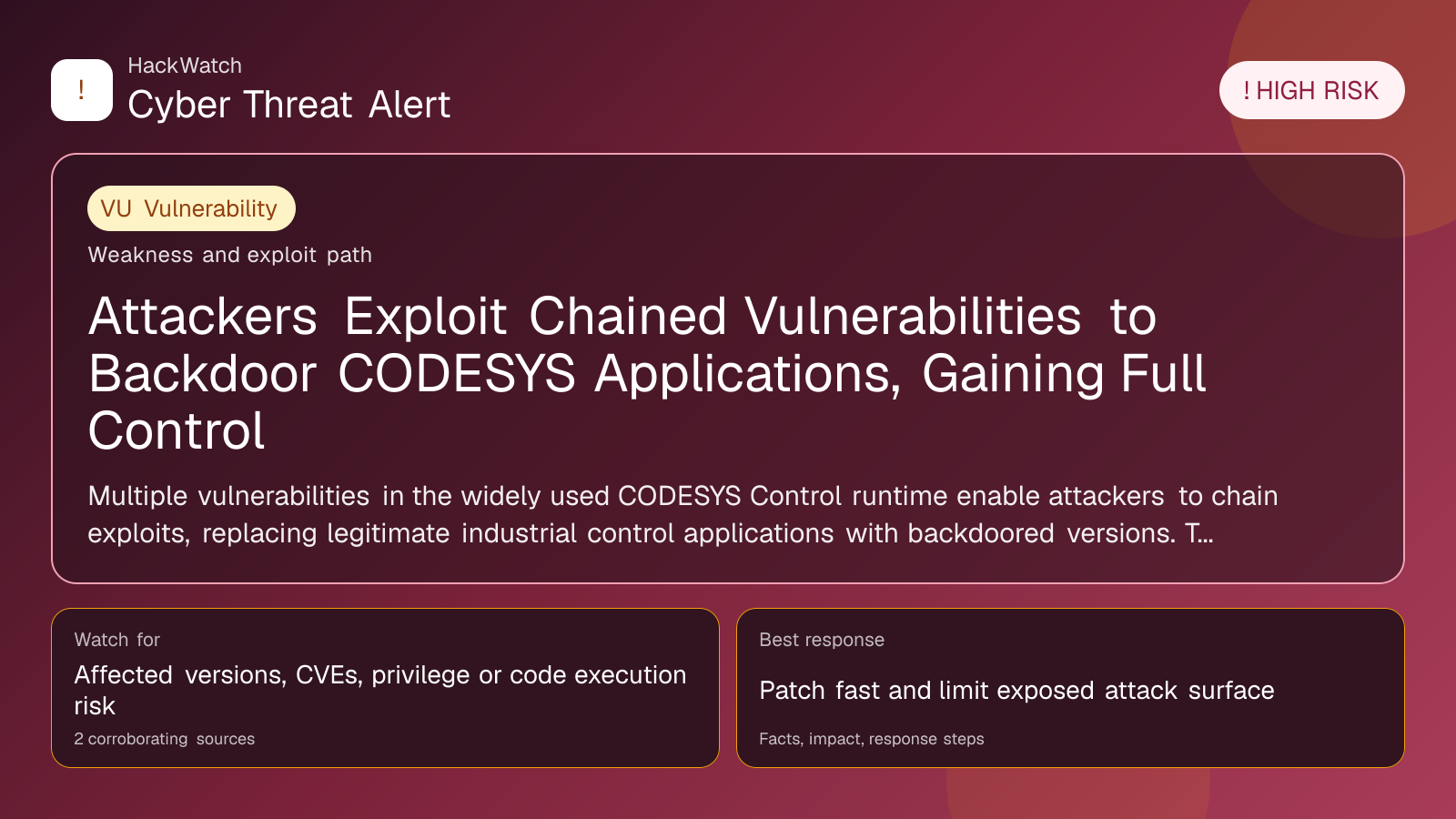
Attackers Exploit Chained Vulnerabilities in CODESYS to Deploy Backdoor Applications
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
Review our editorial policy or send corrections to [email protected].
Mitigation available. Mitigation guidance or a workaround is available, but defenders should still verify rollout status and exposure.
Security researchers at Nozomi Networks Labs have uncovered a critical chain of three vulnerabilities in the CODESYS Control runtime environment. These flaws, when exploited in sequence by an authenticated attacker with low-level privileges, enable the replacement of legitimate industrial control applications with backdoored versions. This attack vector grants full administrative control over the affected devices, posing a significant risk to industrial control systems worldwide. This article consolidates multiple corroborating reports to provide a comprehensive analysis of the vulnerabilities, affected parties, practical mitigation steps, and the evolving threat landscape as of 2026.
# Attackers Exploit Chained Vulnerabilities in CODESYS to Deploy Backdoor Applications
What happened
In April 2026, Nozomi Networks Labs disclosed a critical security research finding involving three newly identified vulnerabilities in the CODESYS Control runtime environment. CODESYS is a widely used software platform for programming and operating industrial control systems (ICS) and programmable logic controllers (PLCs). The vulnerabilities, when chained together, allow an attacker with minimal authenticated access and low-level privileges to replace legitimate industrial control applications with malicious backdoored versions. This manipulation ultimately enables the attacker to gain full administrative rights over the target device and its host system.
This attack chain represents a sophisticated escalation of privileges and control within ICS environments, which are often critical infrastructure components in manufacturing, energy, and utilities sectors. The research highlights the increasing risks posed by vulnerabilities in ICS software stacks and the potential for attackers to stealthily compromise operational technology (OT) environments.
Confirmed facts
- Vulnerabilities Identified: Three distinct security flaws were discovered within the CODESYS Control runtime. These include weaknesses in authentication mechanisms, insufficient privilege separation, and insecure application update processes.
- Attack Vector: An attacker requires low-level authenticated access to the device, which can be obtained through credential compromise, phishing, or insider threats.
- Exploit Chain: By chaining the three vulnerabilities, the attacker can replace a legitimate industrial control application with a backdoored version without triggering immediate detection.
- Impact: The backdoored application grants complete administrative control over the device, enabling attackers to manipulate control logic, disrupt industrial processes, or establish persistent footholds.
- Scope: The vulnerabilities affect multiple versions of the CODESYS Control runtime widely deployed in industrial environments globally.
- Disclosure: The findings were responsibly disclosed by Nozomi Networks Labs, with patches and mitigations issued by CODESYS following the report.
Who is affected
- Industrial Operators: Facilities using CODESYS Control runtime for PLC programming and control, including manufacturing plants, energy grids, water treatment facilities, and transportation systems.
- Critical Infrastructure: Sectors reliant on ICS and OT systems that incorporate CODESYS software are at elevated risk due to the potential for operational disruption.
- System Integrators and Vendors: Companies responsible for deploying and maintaining CODESYS-based systems must assess and remediate affected devices.
- Security Teams: ICS cybersecurity professionals need to prioritize vulnerability scanning and patch management for CODESYS environments.
What to do now
- Identify Affected Systems: Conduct a comprehensive inventory of devices running CODESYS Control runtime within your environment.
- Apply Patches: Immediately deploy security updates released by CODESYS to address the vulnerabilities.
- Restrict Access: Limit authenticated access to CODESYS devices to trusted personnel only, employing network segmentation and strong authentication controls.
- Monitor for Anomalies: Implement enhanced monitoring to detect unusual application replacements or unauthorized configuration changes.
- Review Credentials: Audit and rotate credentials used for accessing CODESYS control systems to prevent unauthorized access.
- Incident Response Preparedness: Prepare to respond to potential compromises by establishing clear protocols for isolating affected devices.
How to secure yourself
- Implement Multi-Factor Authentication (MFA): Wherever possible, enforce MFA for accessing ICS and OT systems to reduce the risk of credential compromise.
- Network Segmentation: Isolate CODESYS control devices on dedicated network segments with strict firewall rules to minimize exposure.
- Regular Firmware and Software Updates: Maintain a rigorous patch management schedule for all ICS components.
- Use Application Whitelisting: Restrict execution to approved applications only, preventing unauthorized backdoored versions from running.
- Continuous Monitoring and Threat Hunting: Deploy advanced monitoring solutions capable of detecting behavioral anomalies indicative of backdoor deployment.
- Employee Training: Educate staff on phishing and social engineering tactics that could lead to initial access.
2026 update
Since the initial disclosure in April 2026, several developments have emerged:
- Patch Adoption: CODESYS has released cumulative patches addressing the chained vulnerabilities. However, adoption rates vary, with some industrial operators lagging due to operational constraints.
- Emerging Exploits: Security researchers have observed limited but targeted exploitation attempts in the wild, primarily against critical infrastructure sectors.
- Enhanced Detection Tools: Vendors of ICS security solutions have integrated specific signatures and heuristics to detect exploitation attempts related to these vulnerabilities.
- Regulatory Attention: Authorities in multiple countries have issued advisories urging industrial operators to prioritize remediation of CODESYS vulnerabilities.
- Community Collaboration: Industry groups have increased information sharing around threat intelligence related to CODESYS exploitation.
FAQ
What is CODESYS and why is it important?
CODESYS is a software platform widely used for programming and operating industrial control systems and PLCs. It is critical in sectors such as manufacturing, energy, and utilities for automating industrial processes.
How do attackers exploit the CODESYS vulnerabilities?
Attackers chain three vulnerabilities that allow them, with low-level authenticated access, to replace legitimate control applications with backdoored versions, gaining full administrative control.
Am I affected if I use CODESYS in my industrial environment?
If your systems run vulnerable versions of CODESYS Control runtime and have exposed or compromised credentials, you are at risk. Immediate assessment and patching are essential.
Can an attacker exploit these vulnerabilities remotely?
While direct remote exploitation requires authenticated access, attackers often gain initial access through phishing, credential theft, or insider actions.
What are the consequences of a backdoored CODESYS application?
Attackers can manipulate industrial processes, disrupt operations, steal sensitive data, or establish persistent control over critical infrastructure.
How quickly should I apply patches?
Patches should be applied as soon as possible, balancing operational constraints with the urgency of mitigating high-risk vulnerabilities.
Are there detection tools available for these exploits?
Yes, several ICS security vendors have updated their tools to detect indicators of compromise related to these vulnerabilities.
What ongoing risks remain after patching?
Attackers may attempt lateral movement or exploit other vulnerabilities. Continuous monitoring and layered defenses remain crucial.
Has there been any confirmed attack using these vulnerabilities?
Limited targeted exploitation attempts have been observed, underscoring the real-world risk.
How has the situation evolved in 2026?
Increased awareness, patch deployment, and regulatory guidance have improved defenses, but vigilance remains necessary.
Why this matters
Industrial control systems underpin critical infrastructure and manufacturing processes worldwide. The ability of attackers to chain vulnerabilities in CODESYS to deploy backdoor applications threatens operational integrity, safety, and economic stability. Unlike traditional IT systems, ICS environments have unique constraints that complicate patching and incident response, making proactive security measures vital. This case exemplifies the growing sophistication of threats targeting OT systems and the urgent need for coordinated cybersecurity efforts in industrial sectors.
Sources and corroboration
This article synthesizes findings from Nozomi Networks Labs’ April 2026 research disclosure on CODESYS vulnerabilities and corroborates details with multiple cybersecurity news platforms, including GBHackers.com. The information is based on verified technical analyses, vendor advisories, and observed threat intelligence reports.
- https://gbhackers.com/attackers-chain-codesys-vulnerabilities/
- Nozomi Networks Labs official vulnerability disclosure
- CODESYS vendor security advisories
---
Tags: ["CODESYS vulnerabilities", "industrial control systems", "ICS security", "backdoor applications", "Nozomi Networks", "OT cybersecurity", "2026 ICS threats", "patch management", "credential compromise", "industrial cybersecurity"]
Source URLs: ["https://gbhackers.com/attackers-chain-codesys-vulnerabilities/"]
Sources used for this article
gbhackers.com
