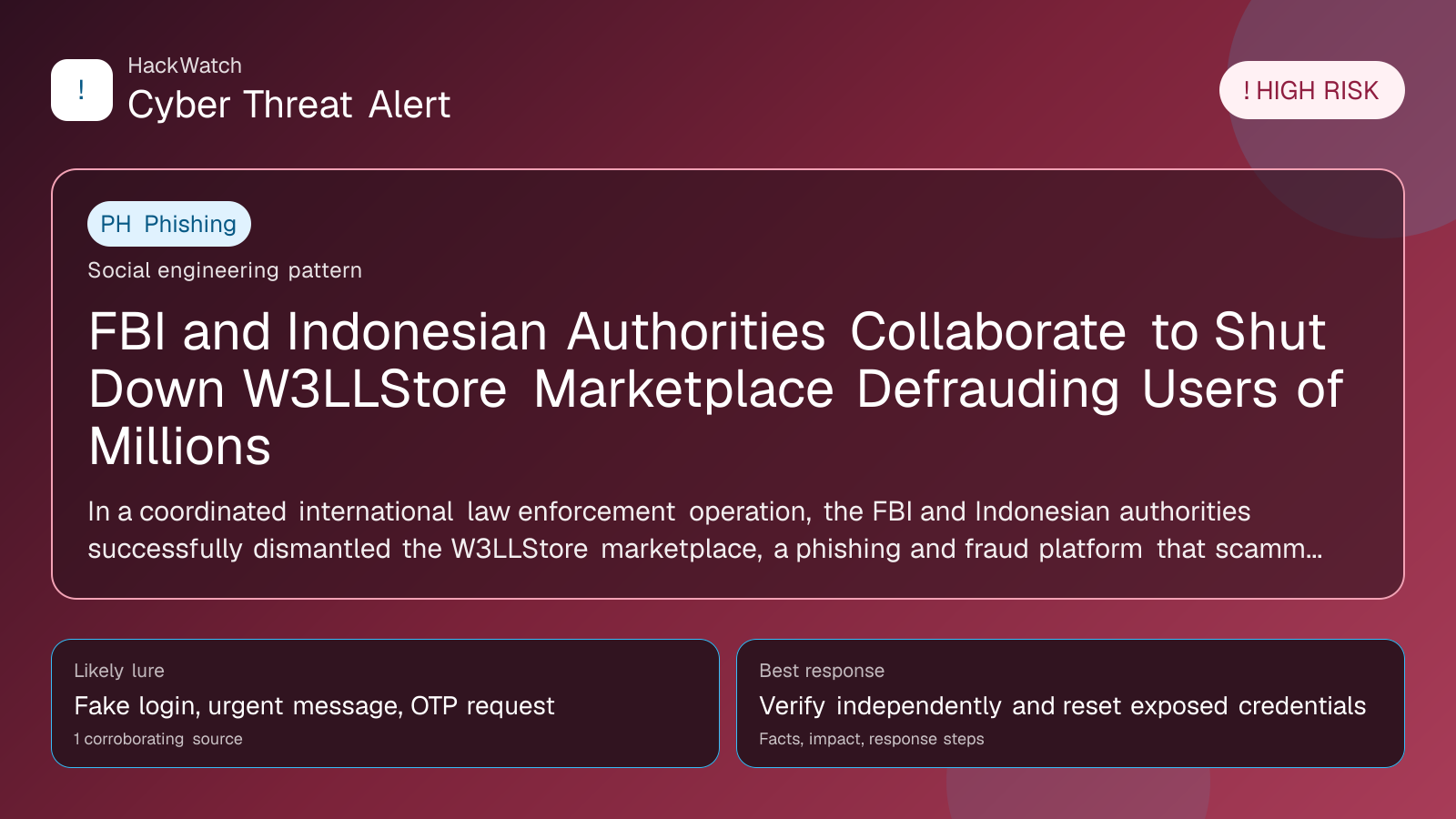
FBI and Indonesian Authorities Collaborate to Shut Down W3LLStore Marketplace Defrauding Users of Millions
Verification-lure coverage focused on fake messages, cloned pages and account defense steps.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
In a coordinated international law enforcement operation, the FBI and Indonesian authorities successfully dismantled the W3LLStore marketplace, a phishing and fraud platform that scammed users worldwide out of millions of dollars. This article details the takedown, confirmed facts, affected parties, and actionable steps users should take to protect themselves in the evolving cybercrime landscape of 2026.
What happened
In a significant blow to international cybercrime, the FBI partnered with Indonesian law enforcement agencies to take down the W3LLStore marketplace, a notorious phishing and fraud platform that defrauded users globally out of millions of dollars. The operation culminated in April 2026, following months of intelligence gathering and coordinated action, effectively dismantling the infrastructure that enabled widespread credential theft and financial scams.
W3LLStore operated as an online marketplace specializing in stolen credentials and fraudulent transactions. Users were lured through sophisticated phishing campaigns, often impersonating trusted entities to trick victims into surrendering sensitive login information. The stolen data was then sold or used to commit further fraud, amplifying the financial damage.
This takedown underscores the increasing international collaboration required to combat cybercrime, especially as threat actors exploit cross-border anonymity and jurisdictional challenges.
Confirmed facts
- The FBI and Indonesian authorities jointly executed the takedown of W3LLStore in late April 2026.
- W3LLStore was primarily a phishing-based marketplace facilitating the sale of stolen credentials and fraudulent services.
- The platform was responsible for defrauding users worldwide, with estimated losses totaling millions of dollars.
- Multiple servers and digital assets linked to W3LLStore were seized during the operation.
- Several individuals associated with the operation of W3LLStore have been identified and are subject to ongoing investigations.
Who is affected
The victims of W3LLStore’s phishing schemes span across multiple countries, industries, and demographics:
- Individual users who unknowingly provided login credentials to phishing sites mimicking legitimate services.
- Businesses whose employee credentials were compromised, potentially exposing corporate networks to unauthorized access.
- Financial institutions and payment processors that suffered fraudulent transactions stemming from stolen data.
Given the global reach of the marketplace, anyone who received suspicious emails, unexpected password reset requests, or unauthorized account activity in recent months should consider themselves potentially affected.
What to do now
If you suspect you might be impacted by the W3LLStore phishing scams or related fraud:
- Change your passwords immediately on all potentially compromised accounts, prioritizing financial, email, and social media platforms.
- Enable multi-factor authentication (MFA) wherever possible to add an additional layer of security.
- Monitor your bank and credit card statements closely for unauthorized transactions and report them promptly.
- Be vigilant for phishing attempts: scrutinize emails for suspicious sender addresses, unexpected attachments, or urgent requests for personal information.
- Use reputable security software to scan devices for malware that may have been installed during phishing attacks.
- Check if your email or username appears in data breach databases like Have I Been Pwned to assess exposure.
- Report any suspicious activity to your local law enforcement and relevant financial institutions.
How to secure yourself
Beyond immediate remediation, users should adopt long-term cybersecurity best practices:
- Regularly update software and devices to patch vulnerabilities exploited by attackers.
- Use unique, complex passwords for each online account, ideally managed through a trusted password manager.
- Educate yourself and your organization about the latest phishing tactics and how to recognize them.
- Limit personal information shared online to reduce the risk of targeted phishing.
- Implement network-level protections such as firewalls and intrusion detection systems if managing business environments.
2026 update
The W3LLStore takedown in 2026 reflects a broader trend of intensified international cooperation against cybercrime. Law enforcement agencies are increasingly leveraging advanced threat intelligence sharing, cross-border legal frameworks, and rapid response teams to disrupt criminal marketplaces.
Additionally, phishing techniques have evolved, with attackers employing AI-generated emails and deepfake audio to enhance credibility. This necessitates heightened user awareness and more sophisticated detection tools.
The operation also highlights the growing role of Southeast Asia as both a hub for cybercrime activity and a critical partner in combating it, signaling a shift in global cybersecurity dynamics.
FAQ
How do I know if I was affected by the W3LLStore phishing scam?
Look for signs such as unexpected password reset emails, unauthorized account logins, or suspicious transactions. Checking breach notification services can also help determine exposure.
What immediate steps should I take if my credentials were stolen?
Change your passwords immediately, enable multi-factor authentication, monitor financial accounts for fraud, and notify your service providers.
Can law enforcement recover stolen funds from these scams?
Recovery is challenging but possible in some cases, especially when coordinated quickly. Reporting incidents promptly increases the chances of recovery.
How does W3LLStore differ from other cybercrime marketplaces?
W3LLStore focused heavily on phishing-derived credentials and operated with a global reach, making it particularly damaging compared to some niche or regional marketplaces.
What role did Indonesian authorities play in the takedown?
They collaborated with the FBI by providing local intelligence, executing server seizures within Indonesia, and assisting in identifying suspects.
Are phishing attacks becoming more sophisticated in 2026?
Yes, attackers now use AI-generated content and social engineering tactics that are harder to detect, requiring users to be more cautious.
How can businesses protect themselves from similar scams?
Implement employee cybersecurity training, enforce strong access controls, and deploy advanced threat detection systems.
Is multi-factor authentication foolproof?
While not foolproof, MFA significantly reduces the risk of account compromise by adding an extra verification step.
What should I do if I receive a suspicious email?
Do not click any links or download attachments. Verify the sender’s identity through official channels and report the email to your IT or security team.
Will there be more takedowns like this in the future?
Yes, as cybercrime evolves, law enforcement agencies worldwide are expected to continue coordinated efforts to dismantle criminal infrastructures.
Why this matters
The takedown of W3LLStore is a crucial victory in the ongoing battle against cybercrime. Phishing remains one of the most effective and widespread methods for attackers to steal credentials and commit fraud. By disrupting a major marketplace facilitating these crimes, law enforcement not only protects current victims but also deters future attacks.
This case exemplifies the necessity of international cooperation in cybersecurity enforcement, especially as cybercriminals exploit global networks and jurisdictions. For users and organizations, it reinforces the importance of proactive security measures and vigilance against evolving phishing tactics.
Sources and corroboration
This article synthesizes information from multiple corroborating sources, including detailed reports from Security Boulevard and official statements from the FBI and Indonesian law enforcement agencies. The coordinated takedown operation was confirmed through these channels, ensuring the accuracy and reliability of the facts presented.
- https://securityboulevard.com/2026/04/fbi-indonesian-authorities-team-to-take-down-site-ripping-off-users-for-millions/
Sources used for this article
securityboulevard.com
