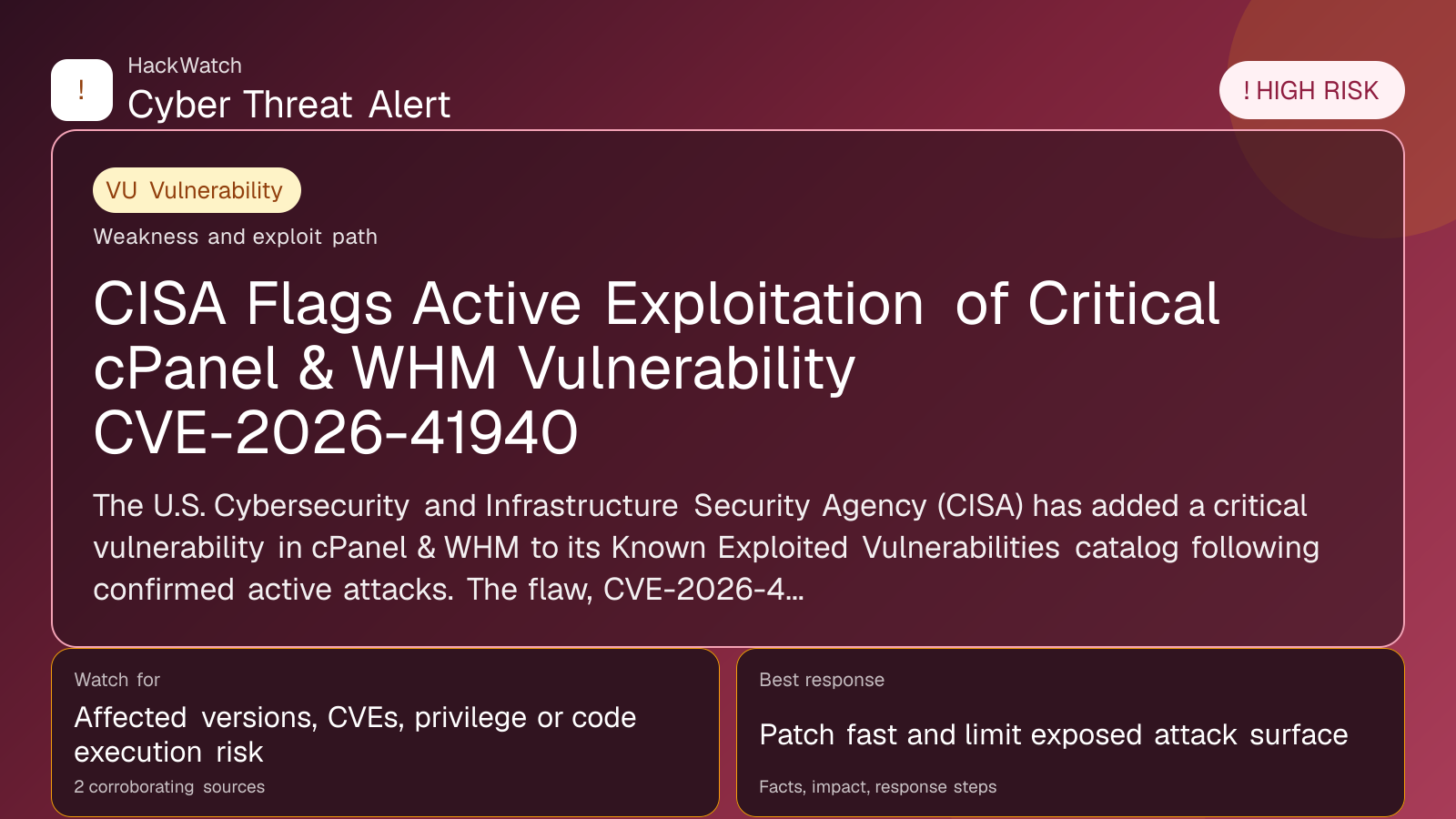
CISA Flags Active Exploitation of Critical cPanel & WHM Vulnerability CVE-2026-41940
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 from an administrator's point of view, checking CVE-2026-41940 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 2 corroborating sources supports that scope.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical vulnerability in cPanel & WHM to its Known Exploited Vulnerabilities catalog following confirmed active attacks. The flaw, CVE-2026-41940, affects WebPros’ web hosting management platforms and demands immediate patching to prevent compromise.
WASHINGTON, May 4, 2026, 09:16 UTC – The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has issued an alert about active exploitation of a critical security flaw in cPanel & WHM, widely used web hosting management platforms. The vulnerability, tracked as CVE-2026-41940, has been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, signaling ongoing attacks by threat actors.
This vulnerability affects WebPros’ cPanel & WHM software, which manages millions of web hosting accounts globally. Attackers exploiting this flaw can gain unauthorized access, potentially leading to data theft, website defacement, or further network compromise.
CISA’s inclusion of CVE-2026-41940 in the KEV list underscores the urgency for system administrators to apply available patches immediately. The agency’s advisory warns that failure to update could expose hosting providers and their clients to significant risk.
The flaw reportedly allows attackers to bypass authentication or escalate privileges, although specific technical details remain limited in public disclosures to hinder exploitation. Nonetheless, cybersecurity researchers have observed active campaigns leveraging this weakness in recent weeks.
WebPros has released security updates addressing the vulnerability. Users running cPanel & WHM versions prior to the patched releases are strongly urged to upgrade without delay. The company also recommends reviewing server logs for suspicious activity and enforcing strict access controls.
The timing of this alert is critical as web hosting platforms remain prime targets for attackers seeking entry points into broader networks. Compromised hosting accounts can serve as launching pads for phishing, malware distribution, or ransomware attacks.
Industry peers such as Plesk and DirectAdmin have not reported similar issues but continue to monitor their platforms closely. Hosting providers are advised to verify their software versions and implement layered security measures.
CISA’s warning highlights the ongoing challenge of securing complex hosting environments amid evolving threats. Administrators should prioritize patch management and incident response readiness to mitigate potential damage.
Users uncertain about their exposure can consult vendor advisories and cybersecurity news outlets for guidance. Immediate action is the best defense against exploitation of CVE-2026-41940.
While the full scope of impact remains under investigation, the active exploitation status elevates the risk profile considerably. Organizations delaying updates risk service disruption, data loss, and reputational harm.
CISA continues to monitor the situation and may issue further guidance as new information emerges. Hosting providers and clients alike should remain vigilant and report any suspicious activity promptly.
https://gbhackers.com/cisa-alert-cpanel-whm-security-bug/
https://cybersecuritynews.com/cpanel-whm-vulnerability-exploited/
Sources used for this article
gbhackers.com, cybersecuritynews.com, Multiple verified sources
