CISA Adds Critical Linux Kernel Vulnerability to Known Exploited Catalog
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 from an administrator's point of view, checking CVE-2026-31431 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 1 corroborating source supports that scope.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
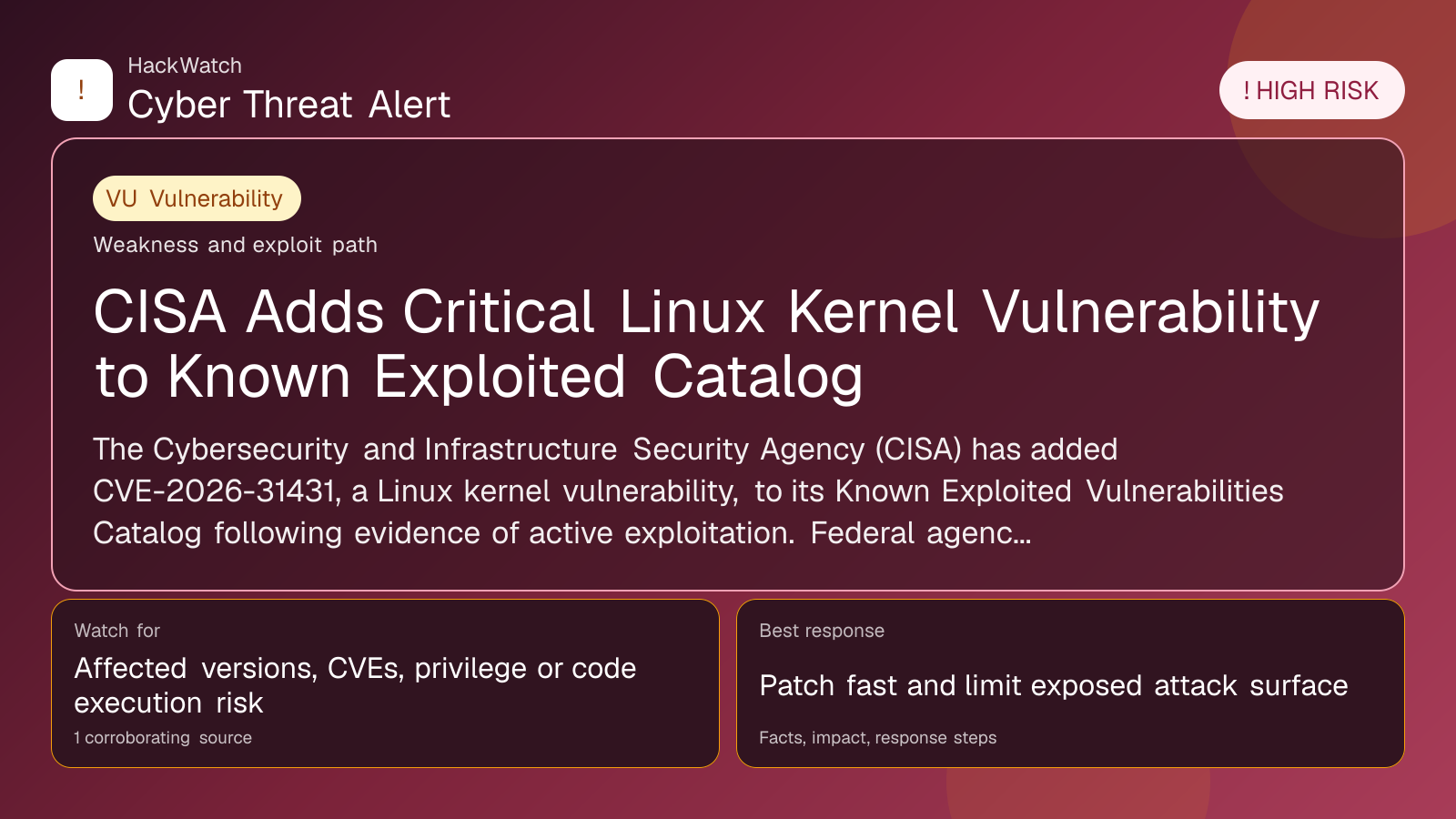
The Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2026-31431, a Linux kernel vulnerability, to its Known Exploited Vulnerabilities Catalog following evidence of active exploitation. Federal agencies must remediate the flaw under Binding Operational Directive 22-01, while private organizations are urged to prioritize patching to mitigate attack risks.
WASHINGTON, June 1, 2026, 15:58 UTC
The Cybersecurity and Infrastructure Security Agency (CISA) has added a new high-risk vulnerability, CVE-2026-31431, affecting the Linux kernel to its Known Exploited Vulnerabilities (KEV) Catalog. The move follows confirmed reports of active exploitation targeting this flaw.
CVE-2026-31431 involves an incorrect resource transfer between security spheres within the Linux kernel. Such vulnerabilities are commonly exploited by threat actors to escalate privileges or execute unauthorized code, posing a significant threat to federal networks and other critical infrastructure.
Under Binding Operational Directive 22-01, federal civilian agencies are mandated to remediate vulnerabilities listed in the KEV Catalog by specified deadlines to safeguard government systems. While this directive applies to federal entities, CISA strongly recommends all organizations, including private sector and critical infrastructure operators, to address the vulnerability promptly.
The KEV Catalog serves as a dynamic list of vulnerabilities with verified active exploitation, guiding agencies and organizations on urgent remediation priorities. CVE-2026-31431’s addition reflects the ongoing risk posed by Linux kernel flaws, which underpin many enterprise and cloud environments.
Security teams should prioritize patching affected Linux kernel versions as soon as updates become available. Delays in remediation increase exposure to attacks that can lead to data breaches, system compromise, or disruption.
CISA’s advisory does not specify affected Linux distributions but urges administrators to consult vendor bulletins for patches. Given the widespread use of Linux in government and industry, the vulnerability’s impact could be extensive.
The agency continues to monitor exploitation trends and will update the KEV Catalog as new information emerges. Organizations are encouraged to integrate KEV Catalog monitoring into their vulnerability management programs.
This update underscores the persistent threat posed by kernel-level vulnerabilities and the need for vigilant patch management. Cyber defenders should also review system logs and network activity for signs of exploitation attempts related to this vulnerability.
While the KEV Catalog focuses on vulnerabilities with known active exploits, organizations should maintain comprehensive security hygiene, including multi-factor authentication and network segmentation, to reduce overall risk.
CISA’s action highlights the importance of rapid response to emerging threats amid an evolving cyber landscape. The agency’s ongoing efforts aim to reduce the window of opportunity for attackers leveraging known weaknesses.
For further details, organizations can access CISA’s advisory and the KEV Catalog on the agency’s website.
https://www.cisa.gov/news-events/alerts/2026/05/01/cisa-adds-one-known-exploited-vulnerability-catalog
Sources used for this article
cisa.gov
