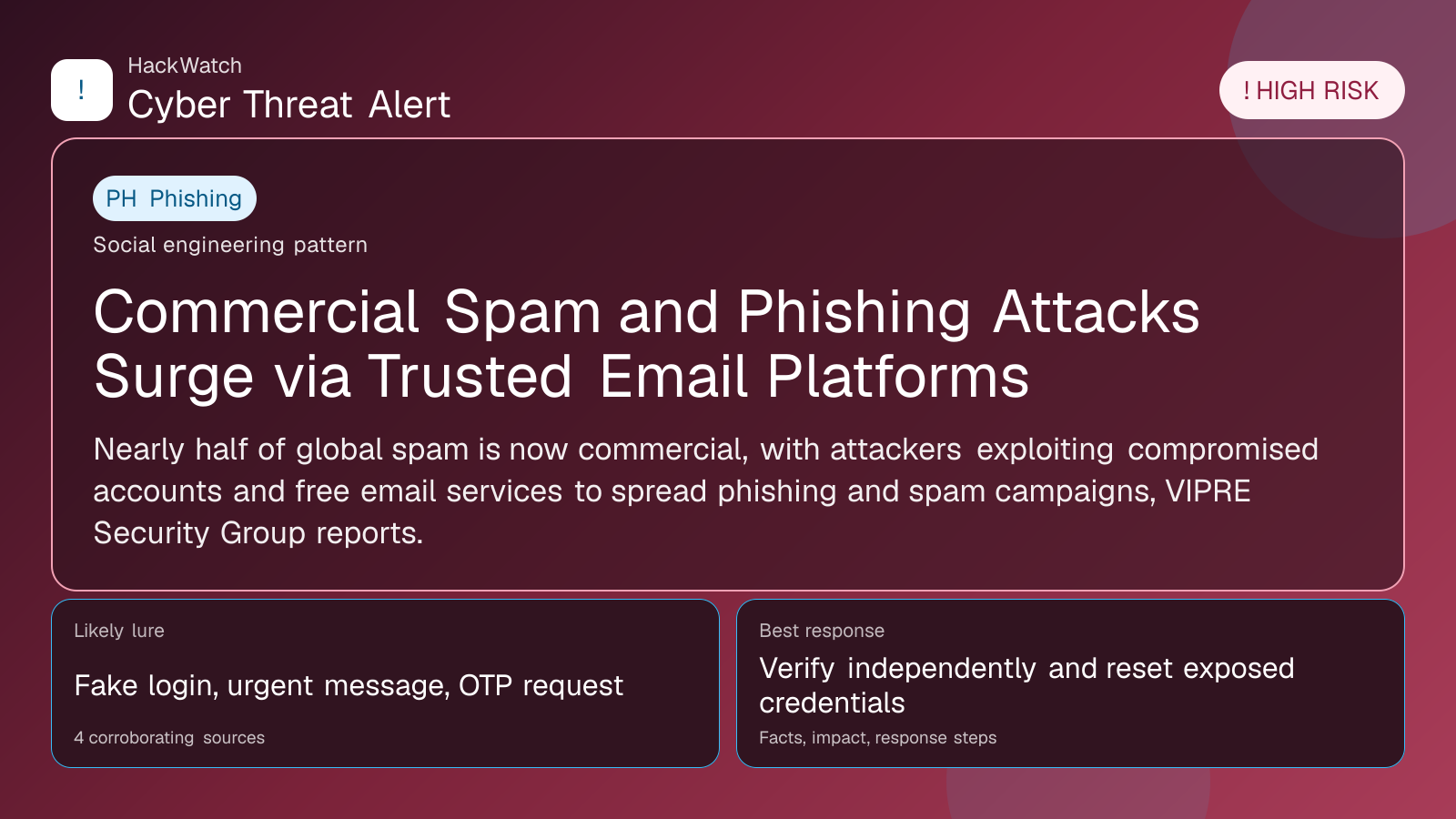
Commercial Spam and Phishing Attacks Surge via Trusted Email Platforms
Verification-lure coverage focused on fake messages, cloned pages and account defense steps.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 4 corroborating sources.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
Nearly half of global spam is now commercial, with attackers exploiting compromised accounts and free email services to spread phishing and spam campaigns, VIPRE Security Group reports.
GLOBAL, May 1, 2026, 18:44 UTC
Commercial spam accounts for 46% of all spam worldwide, according to VIPRE Security Group's Q1 2026 Email Threat Trends Report. The rise is driven largely by attackers leveraging compromised accounts and free email services to distribute phishing and spam.
This shift matters because trusted platforms, often seen as safer by users, are increasingly used as vectors for malicious campaigns. Attackers exploit the inherent trust in these services to bypass filters and increase the likelihood of successful phishing attempts.
VIPRE's report highlights that compromised legitimate accounts are a key source of the spam surge. When attackers hijack these accounts, their messages are less likely to be flagged as suspicious, enabling widespread distribution of commercial spam and phishing links.
Free email services also play a significant role. Their accessibility and large user bases make them attractive for attackers to create disposable accounts or hijack existing ones for spam campaigns.
The commercial nature of this spam indicates a focus on financial gain, often through fraudulent offers, fake promotions, or phishing designed to steal credentials and payment information.
Users should be vigilant about unexpected emails, even if they appear to come from known contacts or reputable services. Checking URLs carefully and avoiding clicking on unsolicited links remain critical defenses.
Organizations can reduce risk by enforcing multi-factor authentication (MFA) on email accounts to limit the impact of account compromises. Regular monitoring for unusual email activity is also advised.
Email providers face growing pressure to improve detection and prevention mechanisms that account for the use of legitimate accounts in spam campaigns. Enhanced behavioral analysis and anomaly detection could help identify compromised accounts faster.
The trend underscores the evolving tactics of cybercriminals who increasingly blend into trusted environments to evade detection. This complicates traditional spam filtering and requires adaptive security strategies.
While the report does not detail specific threat actors, the data suggests a widespread, opportunistic approach rather than isolated campaigns.
Users and organizations should review their email security posture promptly to mitigate exposure, especially as commercial spam continues to rise.
The risk remains medium but persistent. Attackers' reliance on trusted platforms means that even cautious users can be targeted, increasing the potential for credential theft and financial fraud.
Continued vigilance and layered security controls are essential to counter this growing threat vector.
https://www.scworld.com/brief/commercial-spam-and-phishing-attacks-increasingly-leverage-trusted-platforms
Sources used for this article
scmagazine.com, cybersecuritydive.com, techrepublic.com
- https://www.scworld.com/news/microsoft-qr-code-captcha-gated-phishing-more-than-double-in-q1-2026
- https://www.cybersecuritydive.com/news/email-phishing-trends-microsoft-qr-codes/819077/
- https://www.techrepublic.com/article/news-microsoft-phishing-emails-qr-codes-captcha-phaas/
- https://www.scworld.com/brief/commercial-spam-and-phishing-attacks-increasingly-leverage-trusted-platforms
