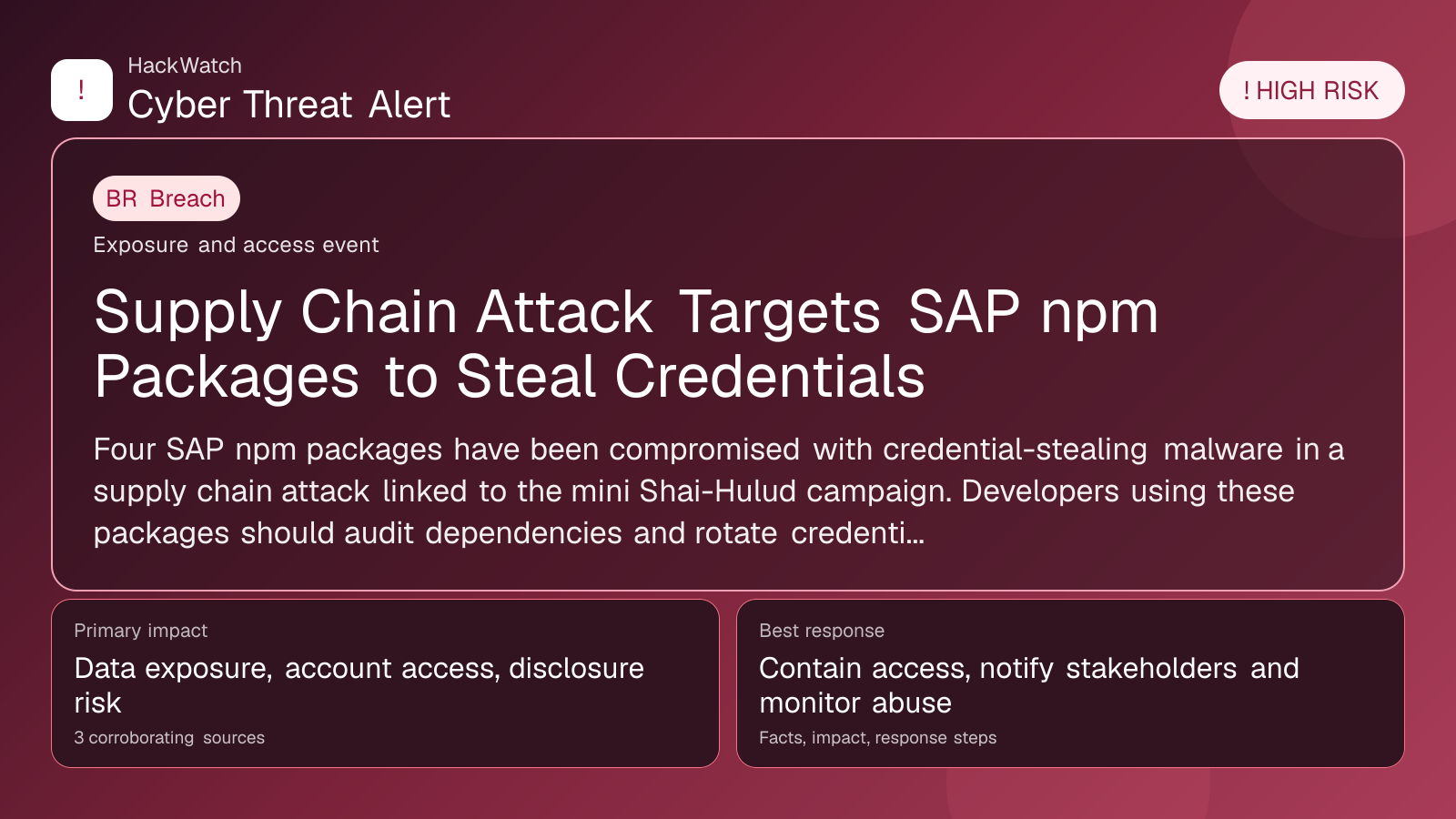
Supply Chain Attack Targets SAP npm Packages to Steal Credentials
Breach coverage centered on exposed data, scope clarification and immediate containment priorities.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 3 corroborating sources.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
Four SAP npm packages have been compromised with credential-stealing malware in a supply chain attack linked to the mini Shai-Hulud campaign. Developers using these packages should audit dependencies and rotate credentials immediately.
GLOBAL, May 1, 2026, 17:45 UTC
Threat actors have injected credential-stealing malware into four SAP npm packages, marking a new wave of supply chain attacks under the mini Shai-Hulud campaign, according to The Hacker News.
This intrusion is significant because npm packages are widely used in software development, and SAP’s ecosystem powers critical enterprise applications. Compromising these packages allows attackers to harvest credentials from developers and potentially pivot to broader corporate networks.
The malicious code embedded in these packages is designed to capture sensitive information such as usernames and passwords when the packages are installed or executed. This type of supply chain compromise exploits trust in legitimate software components, making detection challenging.
SAP has not yet issued a public statement, but security researchers urge immediate review and removal of the affected packages from development environments. Organizations relying on SAP npm packages should conduct thorough audits of their dependencies to identify any suspicious activity.
Credential theft at this scale can lead to unauthorized access, data breaches, and further infiltration into corporate systems. Attackers often use stolen credentials to move laterally or deploy ransomware, amplifying the risk.
Developers and IT teams are advised to rotate any credentials that may have been exposed and implement multi-factor authentication to reduce account takeover risks. Monitoring for unusual login patterns can also help detect compromised accounts early.
This incident follows a growing trend of supply chain attacks targeting open-source components, which have become a favored vector due to their widespread use and implicit trust.
The mini Shai-Hulud campaign has previously targeted other software ecosystems, but this is the first known compromise involving SAP npm packages, highlighting the attackers’ expanding scope.
Security experts recommend leveraging tools that automatically scan for malicious code in dependencies and maintaining strict version control to prevent unauthorized changes.
While the full extent of the attack remains under investigation, the potential impact on enterprise security is considerable given SAP’s prominence in business-critical infrastructure.
Users should stay alert for updates from SAP and npm registries regarding patches or package removals. Immediate action can mitigate the risk of credential theft and subsequent exploitation.
The incident underscores the urgent need for enhanced supply chain security practices, including vetting third-party components and adopting zero-trust principles in software development.
https://www.scworld.com/brief/supply-chain-attack-against-sap-npm-packages-facilitates-credential-theft
Sources used for this article
scmagazine.com, sentinelone.com
- https://www.scworld.com/brief/austrian-and-albanian-authorities-dismantle-e50-million-cryptocurrency-fraud-ring
- https://www.sentinelone.com/blog/the-good-the-bad-and-the-ugly-in-cybersecurity-week-18-7/
- https://www.scworld.com/brief/supply-chain-attack-against-sap-npm-packages-facilitates-credential-theft
