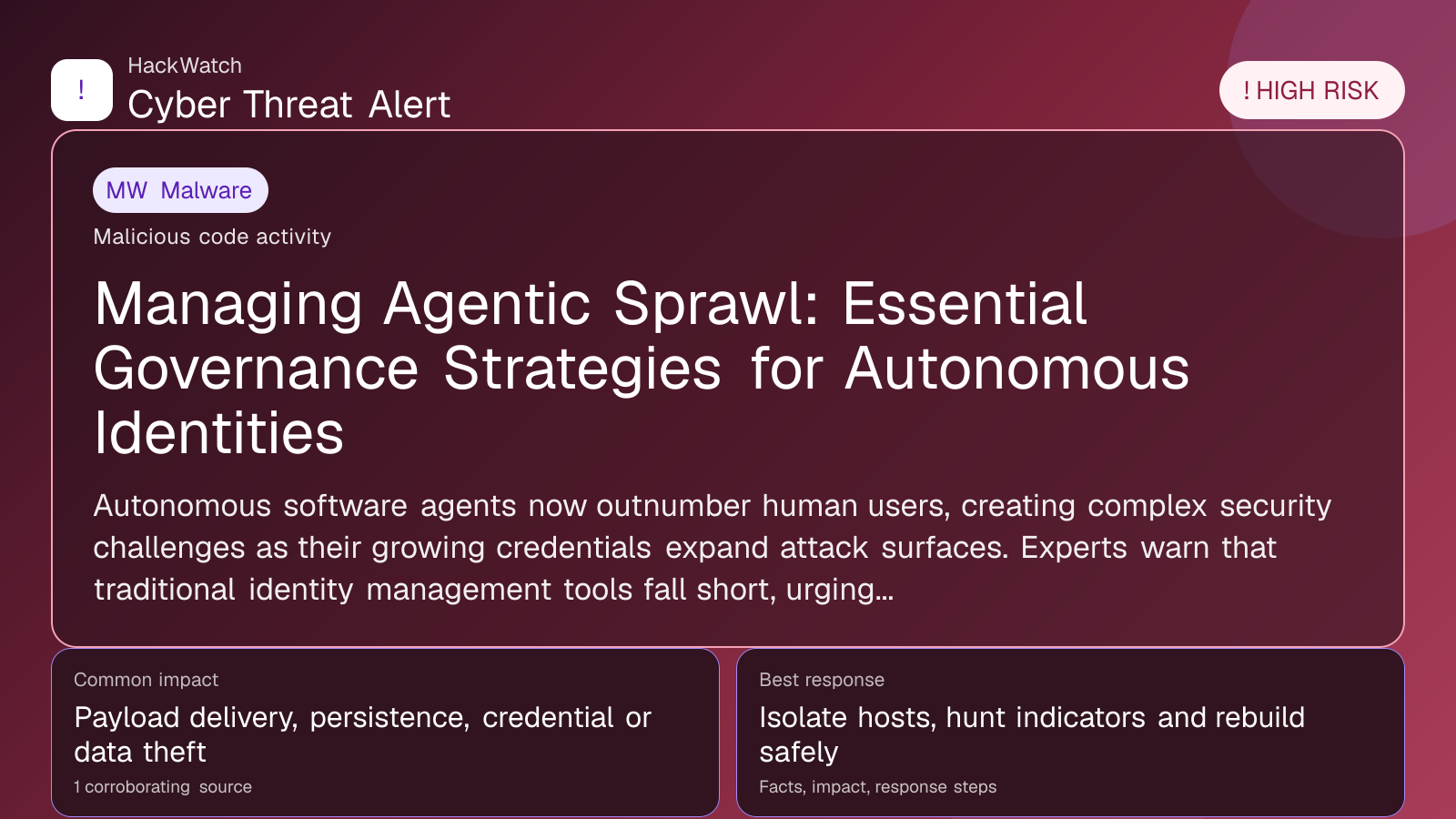
Managing Agentic Sprawl: Essential Governance Strategies for Autonomous Identities
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: May 01, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 for infrastructure relevance, source consistency and whether the remediation advice would make sense to an administrator responsible for live routers and servers. His note keeps the action list grounded: validate scope, reduce exposed management paths, keep evidence intact and avoid claims that go beyond the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
Autonomous software agents now outnumber human users, creating complex security challenges as their growing credentials expand attack surfaces. Experts warn that traditional identity management tools fall short, urging firms to adopt stricter governance and dynamic controls to prevent credential abuse and limit exposure.
GLOBAL, May 1, 2026, 14:45 UTC
- Autonomous agent identities have surpassed human identities, broadening potential attack vectors.
- Excessive OAuth permissions and long-lived tokens increase risks of credential compromise.
- Conventional identity and access management (IAM) systems struggle to manage the scale and complexity of agent proliferation.
Organizations face mounting security risks as autonomous agents—software programs acting independently—multiply within IT ecosystems. These agents now outnumber human identities, each adding new credentials and access points that enlarge the attack surface.
This rapid increase, known as agentic sprawl, worsens existing identity security issues such as over-permissioned OAuth scopes, token reuse, and service accounts with excessive privileges. Traditional IAM tools were not built to handle this scale or complexity.
The urgency to control agentic sprawl is rising as attackers increasingly exploit these dispersed credentials to breach systems, steal data, or disrupt services. Each autonomous agent represents a potential entry point if not tightly governed.
Security experts note that conventional IAM lacks the fine-grained automation required to monitor and restrict agent activities effectively. This leaves organizations vulnerable to credential misuse and privilege escalation.
To mitigate these risks, firms must enforce the principle of least privilege by restricting OAuth scopes strictly to necessary functions and frequently rotating tokens to reduce credential lifespan.
Avoiding reuse of service accounts across multiple agents and implementing continuous monitoring to detect unusual agent behavior are also critical steps. Automated tools capable of dynamically adjusting permissions based on real-time activity are becoming essential.
Maintaining an up-to-date inventory of autonomous agents and their credentials is vital. This visibility allows for prompt revocation of access when agents are retired or compromised.
Failure to govern agentic sprawl effectively could exponentially increase the attack surface and the chance of successful cyberattacks. As autonomous agents become integral to digital operations, unchecked growth threatens to weaken overall security.
Some organizations have begun adopting zero trust models to contain agentic sprawl, but broad implementation remains limited. The evolving threat environment demands accelerated deployment of adaptive IAM solutions that scale with expanding autonomous identities.
In short, agentic sprawl represents a critical frontier in identity security. Organizations must act swiftly to establish governance frameworks tailored to autonomous agents’ unique challenges.
For administrators and users, the key question is whether their programs have full visibility of all autonomous identities and enforce appropriate controls. Without this, risk exposure remains high.
Cybersecurity teams should prioritize integrating agent-focused policies into IAM strategies and invest in tooling that supports dynamic credential life cycle management.
Given the changing nature of agentic sprawl, continuous reassessment and adaptation of governance practices will be essential to keep pace with emerging threats.
Source: Security Boulevard, Strata.io, May 1, 2026 (https://securityboulevard.com/2026/05/a-guide-to-agentic-sprawl-how-to-govern-your-program/)
Sources used for this article
securityboulevard.com
