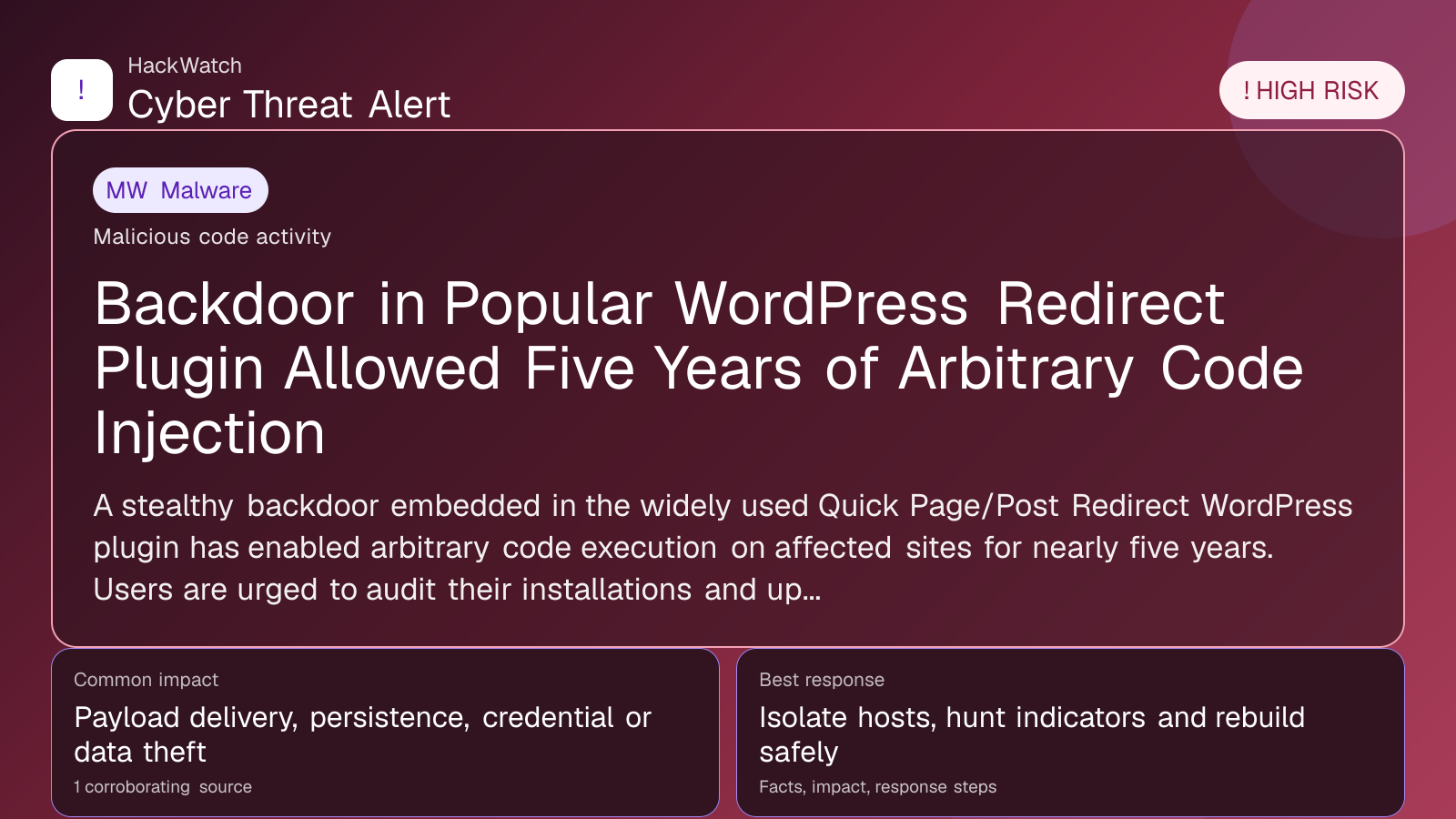
Backdoor in Popular WordPress Redirect Plugin Allowed Five Years of Arbitrary Code Injection
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 for infrastructure impact, containment order and whether persistence or lateral-movement claims are supported by evidence. His administrator note is concrete: isolate the host or segment first, protect logs and network telemetry, then rebuild, rotate or patch only within the scope supported by the 1 corroborating source, the same cautious sequence he would use around managed router and server environments.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A stealthy backdoor embedded in the widely used Quick Page/Post Redirect WordPress plugin has enabled arbitrary code execution on affected sites for nearly five years. Users are urged to audit their installations and update immediately.
GLOBAL, May 1, 2026, 17:39 UTC
A long-hidden backdoor in the Quick Page/Post Redirect WordPress plugin has allowed attackers to inject arbitrary code into websites for almost five years, security researchers reported.
The plugin, which facilitates URL redirects within posts, pages, and custom URLs, was compromised with a stealthy backdoor that went unnoticed since around 2021. This vulnerability effectively gave threat actors remote code execution capabilities on sites using the plugin.
Quick Page/Post Redirect is widely deployed across WordPress sites, making this a significant risk vector. The backdoor’s longevity means numerous websites may have been exposed to unauthorized access or manipulation over an extended period.
Security analysts from BleepingComputer first disclosed the issue after uncovering the malicious code embedded deep within the plugin’s files. The backdoor allowed attackers to push arbitrary PHP code, bypassing typical security controls.
This flaw underscores the risks of supply chain attacks in the WordPress ecosystem, where popular plugins can become attack vectors if vetting and monitoring are insufficient.
Site administrators are advised to immediately check their WordPress installations for the Quick Page/Post Redirect plugin and update to the latest clean version. Removing the compromised plugin and scanning for signs of intrusion is critical.
Failure to address this vulnerability could lead to data breaches, site defacements, or the deployment of further malware. Given the plugin’s role in managing redirects, attackers could also manipulate traffic to malicious sites.
WordPress users should also consider strengthening overall security hygiene, including enforcing strong credentials, limiting plugin use, and employing web application firewalls.
The incident highlights the importance of continuous monitoring and auditing of third-party components in web infrastructure. Even trusted plugins can harbor hidden threats that persist undetected for years.
No official statement from the plugin’s developers has been publicly released as of this writing. The WordPress security community continues to investigate the full scope of affected sites.
Site owners unsure about their exposure should consult cybersecurity professionals to conduct thorough forensic analysis and remediation.
This case adds to a growing list of supply chain compromises targeting content management systems, emphasizing the need for vigilance and rapid response to emerging threats.
https://www.scworld.com/brief/arbitrary-code-pushed-by-long-concealed-backdoor-in-widely-used-wordpress-redirect-add-on
Sources used for this article
scmagazine.com
