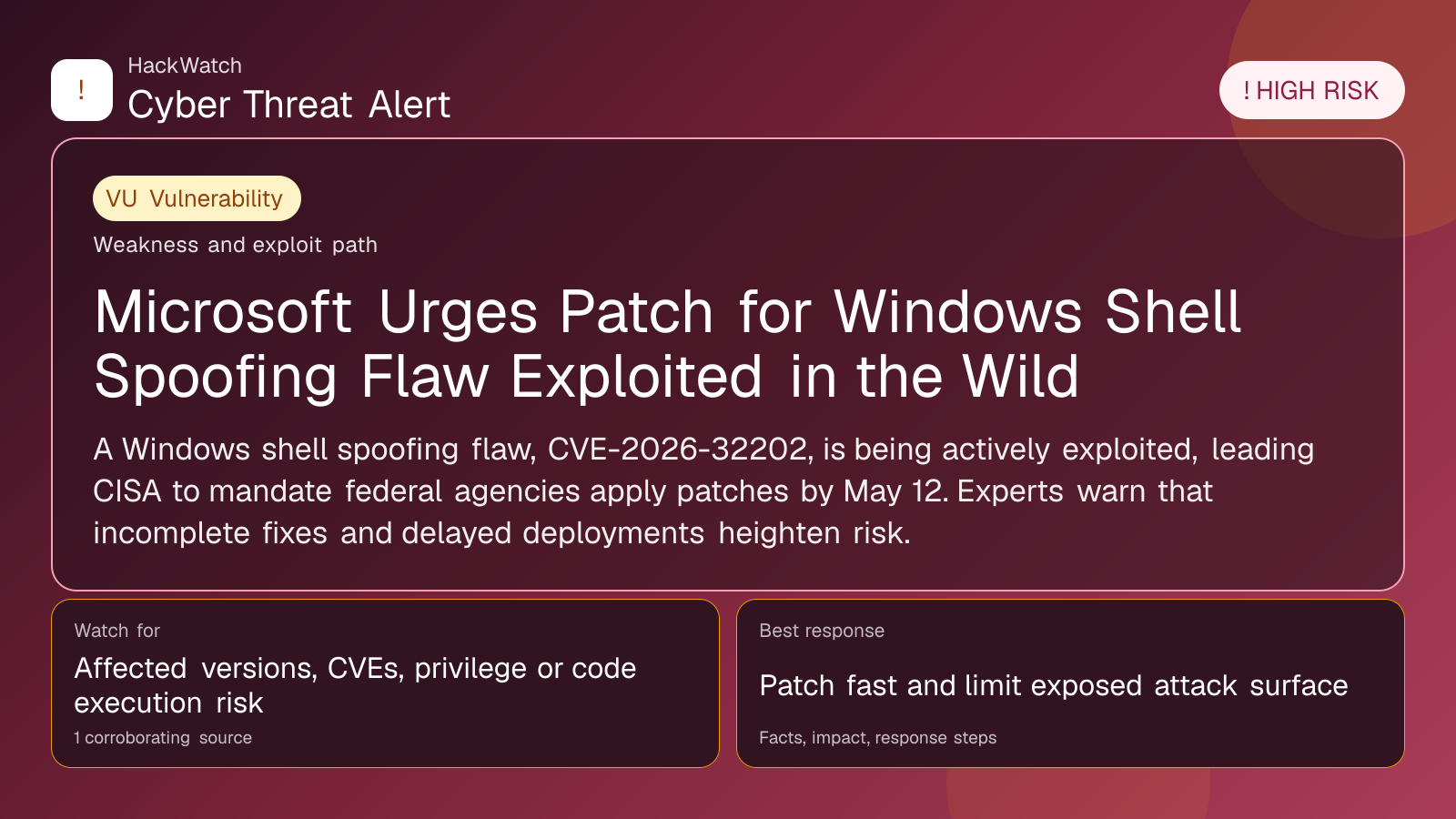
Microsoft Urges Patch for Windows Shell Spoofing Flaw Exploited in the Wild
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 from an administrator's point of view, checking CVE-2026-32202, CVE-2026-21510 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 1 corroborating source supports that scope.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A Windows shell spoofing flaw, CVE-2026-32202, is being actively exploited, leading CISA to mandate federal agencies apply patches by May 12. Experts warn that incomplete fixes and delayed deployments heighten risk.
WASHINGTON, June 1, 2026, 14:24 UTC
Microsoft and the U.S. Cybersecurity and Infrastructure Security Agency (CISA) have flagged an actively exploited Windows shell spoofing vulnerability, tracked as CVE-2026-32202. Although the responsible threat actors remain unconfirmed, suspicion centers on Russian state-linked groups.
CISA has ordered all federal agencies to install the patch by May 12 to prevent potential data exposure. Microsoft’s advisory states the flaw allows attackers to access sensitive information but does not enable full control over affected systems.
This vulnerability originates from an incomplete remediation of an earlier flaw, CVE-2026-21510, leaving residual side effects unaddressed. Lionel Litty, chief information security officer at Menlo Security, noted that vendors often patch the primary issue but overlook related variants, extending the window of vulnerability.
Litty also highlighted the persistent "patch gap"—the lag between patch release and actual deployment. Many organizations delay updates for weeks or months, often fearing operational disruptions.
Erik Avakian, technical counselor at Info-Tech Research Group, explained CISA’s 14-day patch deadline stems from the vulnerability’s moderate CVSS score of 4.3, which falls below thresholds for emergency patching despite active exploitation.
Avakian suggested that temporarily blocking specific network ports at firewalls can reduce exposure. This provides IT teams time to conduct thorough testing before rolling out patches in production environments, minimizing risks of system instability.
Security leaders face a challenge balancing urgent patch application with the risk of unintended consequences from hurried updates. Both Litty and Avakian emphasized the importance of measured, well-planned responses.
Microsoft has not released details on the extent of exploitation or the attackers involved. However, the advisory alongside CISA’s directive signals the threat’s seriousness.
Administrators are urged to prioritize patch deployment and consider additional network controls to limit attack surfaces. Delays in patching increase the likelihood of data breaches and further exploitation.
This case underscores ongoing issues in vulnerability management, where incomplete patches and slow rollout processes leave persistent security gaps.
Organizations should revisit update policies and educate users on the critical need for timely patching to mitigate risks from active exploits like CVE-2026-32202.
While the flaw does not currently permit full system compromise, failure to patch could expose sensitive data to unauthorized access.
CISA’s enforcement of the May 12 deadline for federal agencies reflects the urgency of addressing this vulnerability.
The situation remains dynamic. Security teams should monitor forthcoming advisories from Microsoft and CISA for updates.
https://www.csoonline.com/article/4166080/windows-shell-spoofing-vulnerability-puts-sensitive-data-at-risk.html
Sources used for this article
csoonline.com
