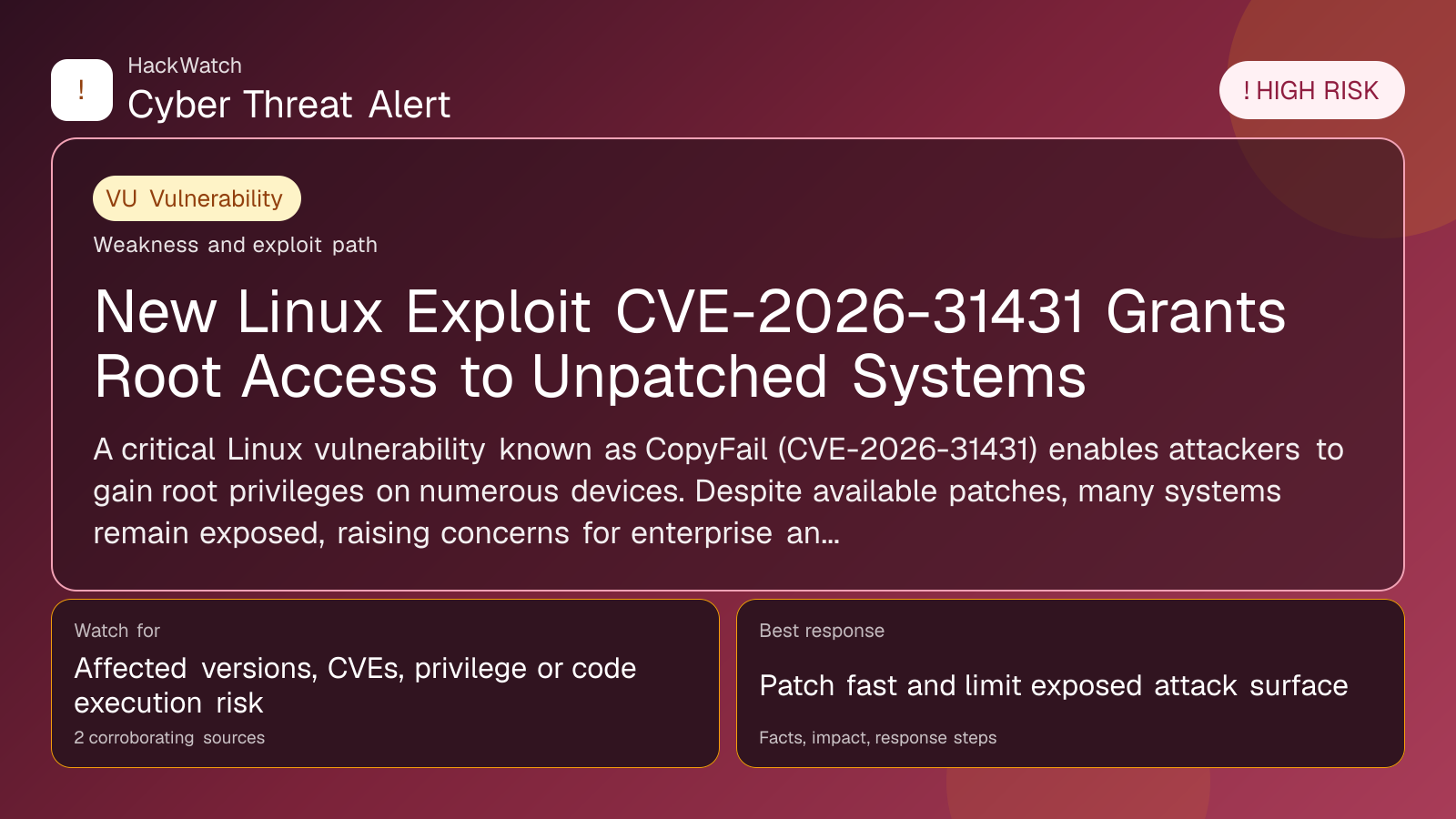
New Linux Exploit CVE-2026-31431 Grants Root Access to Unpatched Systems
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 from an administrator's point of view, checking CVE-2026-31431 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 2 corroborating sources supports that scope.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
A critical Linux vulnerability known as CopyFail (CVE-2026-31431) enables attackers to gain root privileges on numerous devices. Despite available patches, many systems remain exposed, raising concerns for enterprise and personal users alike.
GLOBAL, May 1, 2026, 20:52 UTC
A newly disclosed Linux vulnerability, tracked as CVE-2026-31431 and nicknamed CopyFail, allows attackers to escalate privileges and seize root access on affected machines. The flaw impacts a broad range of Linux distributions, putting both personal computers and data center servers at risk.
The exploit leverages a flaw in the kernel's memory handling during copy operations, enabling malicious actors to overwrite critical data structures. This effectively grants them full control over the compromised system.
Security researchers and vendors have issued patches addressing the vulnerability. However, a significant number of devices remain unpatched, leaving them vulnerable to exploitation. The widespread use of Linux in enterprise environments and cloud infrastructure amplifies the potential impact.
The timing of this disclosure is critical as threat actors may attempt to weaponize the exploit before organizations complete patch rollouts. Experts warn that automated scanning tools could identify vulnerable systems, increasing the risk of targeted attacks.
System administrators are urged to prioritize updating Linux kernels to the latest patched versions. Additionally, monitoring for unusual activity and restricting access to critical systems can help mitigate exploitation risks.
The vulnerability's root cause stems from a subtle bug in the kernel's copy-on-write mechanism, a core feature used to optimize memory usage. Attackers exploiting this can bypass standard security controls and gain unrestricted system privileges.
While Linux distributions have responded swiftly with fixes, the challenge lies in the patch deployment speed across diverse environments, especially in legacy or embedded systems.
Security firms recommend organizations conduct comprehensive audits to identify unpatched hosts and apply updates immediately. Delays could lead to data breaches, ransomware attacks, or infrastructure compromise.
The CopyFail exploit underscores the ongoing need for vigilance in open-source software security, where widespread adoption can amplify the fallout from single vulnerabilities.
Users running Linux on personal or enterprise devices should confirm their kernel versions and apply vendor updates without delay. Failure to do so could expose sensitive data and critical services to attackers.
The incident also highlights the importance of layered security measures, including network segmentation and least-privilege access, to contain potential breaches.
While no widespread attacks exploiting CVE-2026-31431 have been reported yet, the window between disclosure and exploitation remains narrow. Organizations must act swiftly to reduce exposure.
This vulnerability joins a growing list of high-severity Linux kernel flaws discovered in recent years, prompting calls for enhanced security auditing and faster patch distribution channels.
The risk landscape remains fluid, with the possibility of new variants or related exploits emerging as attackers analyze the patch details.
Source: https://www.wired.com/story/dangerous-new-linux-exploit-gives-attackers-root-access-to-countless-computers/
Sources used for this article
redhotcyber.com, wired.com
