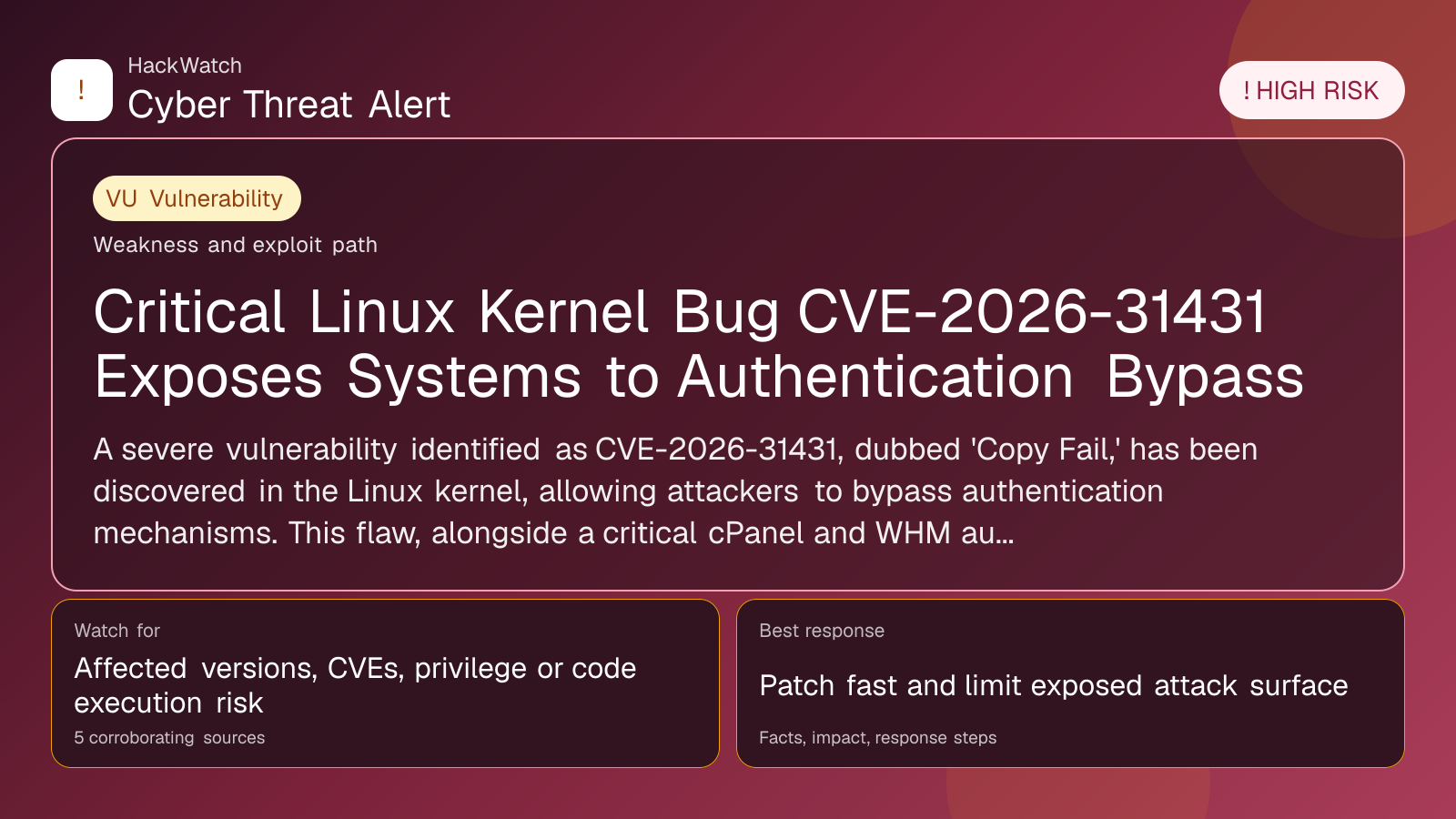
Critical Linux Kernel Bug CVE-2026-31431 Exposes Systems to Authentication Bypass
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: May 01, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 01, 2026 from an administrator's point of view, checking CVE-2026-31431 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 5 corroborating sources supports that scope.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
A severe vulnerability identified as CVE-2026-31431, dubbed 'Copy Fail,' has been discovered in the Linux kernel, allowing attackers to bypass authentication mechanisms. This flaw, alongside a critical cPanel and WHM authentication bypass and the rise of sophisticated phishing tools like EvilTokens, signals heightened risks for system administrators and users alike.
GLOBAL, May 1, 2026, 10:07 UTC
- CVE-2026-31431, a critical Linux kernel vulnerability, enables attackers to bypass authentication controls.
- A separate flaw in cPanel and WebHost Manager (WHM) allows unauthorized access to control panels.
- Emerging phishing toolkit EvilTokens undermines multi-factor authentication (MFA) security.
A newly uncovered security flaw in the Linux kernel, tracked as CVE-2026-31431 and nicknamed "Copy Fail," poses a significant threat to system integrity by enabling attackers to bypass authentication. This vulnerability ranks among the most insidious in recent years, affecting a broad range of Linux-based systems.
The discovery comes amid growing concerns over authentication weaknesses. Researchers at Red Hot Cyber, who monitor underground cybercrime activity daily, have highlighted that this kernel bug could be exploited to gain unauthorized control over affected machines, potentially leading to data breaches or system compromise.
Simultaneously, a critical vulnerability has been identified in cPanel and WebHost Manager (WHM), widely used web hosting control panels. The flaw allows attackers to circumvent login requirements and access administrative panels without credentials. Nearly all versions of these platforms are affected, raising alarms for hosting providers and their customers.
Adding to the threat landscape, the phishing-as-a-service toolkit EvilTokens, which surfaced in February 2026, challenges the assumed reliability of multi-factor authentication (MFA). By leveraging social engineering techniques, this toolkit can bypass MFA protections, undermining a key security layer that many organizations rely on.
These developments are particularly urgent given the increasing reliance on Linux servers and cPanel/WHM platforms for critical infrastructure and web hosting. Attackers exploiting these vulnerabilities could disrupt services, steal sensitive information, or deploy further malware.
The risks extend beyond technical vulnerabilities. Cybercriminal marketplaces such as Jerry’s Store, which recently shut down after selling stolen credit card data, illustrate the scale and sophistication of illicit operations that benefit from such security gaps.
Experts warn that organizations must urgently patch affected systems. Linux kernel updates addressing CVE-2026-31431 are now available, and cPanel/WHM vendors have released security fixes. Users should verify their systems are up to date to mitigate exploitation risks.
Meanwhile, reliance on MFA should not breed complacency. Security teams must combine MFA with user education to counter social engineering attacks facilitated by tools like EvilTokens.
The evolving threat environment underscores the need for continuous monitoring of underground cybercrime activities and rapid response to emerging vulnerabilities.
Looking ahead, the cybersecurity community anticipates further analysis of CVE-2026-31431’s exploitation methods and potential patches. The effectiveness of mitigation strategies will be critical to preventing widespread damage.
Organizations should also consider enhancing their incident response plans to address attacks that may leverage these vulnerabilities.
Failure to act swiftly could result in significant operational disruptions and data loss, especially for enterprises dependent on Linux-based infrastructure and web hosting services.
For users and administrators, immediate steps include applying vendor patches, reviewing authentication policies, and increasing vigilance against phishing attempts.
This report synthesizes multiple corroborating sources from Red Hot Cyber’s ongoing cybercrime monitoring efforts.
---
Frequently Asked Questions
What is CVE-2026-31431?
It is a critical security flaw in the Linux kernel that allows attackers to bypass authentication controls, potentially gaining unauthorized access.
Am I affected if I use Linux?
If your system runs an unpatched Linux kernel version vulnerable to CVE-2026-31431, you are at risk.
What about cPanel and WHM users?
Nearly all versions of these control panels are affected by an authentication bypass vulnerability. Immediate patching is essential.
Does MFA protect me from these threats?
MFA is important but can be bypassed by phishing toolkits like EvilTokens. Combining MFA with user training is necessary.
What should I do now?
Update your Linux kernel and cPanel/WHM software, strengthen authentication policies, and educate users about phishing risks.
How can I secure my systems against these vulnerabilities?
Apply all vendor patches, monitor for suspicious activity, and implement layered security controls.
What is the risk if I do nothing?
Attackers could gain unauthorized access, leading to data theft, service disruption, or further malware infections.
Are there any updates expected in 2026?
Further patches and exploitation analyses are expected as researchers and vendors respond to these vulnerabilities.
---
What to Do Now
- Identify all Linux-based systems and hosting control panels in your environment.
- Apply the latest security patches from Linux kernel maintainers and cPanel/WHM vendors immediately.
- Review and reinforce your authentication mechanisms beyond MFA.
- Educate employees and users about phishing risks and social engineering tactics.
- Monitor network and system logs for unusual access patterns.
How to Secure Yourself
- Keep software up to date with security patches.
- Use strong, unique passwords combined with multi-factor authentication.
- Be cautious of unexpected emails or messages requesting credentials.
- Employ endpoint detection and response tools.
- Regularly back up critical data offline.
2026 Update
Ongoing research into CVE-2026-31431 will clarify exploitation techniques and mitigation efficacy. Vendors are expected to release incremental patches. Organizations should stay informed through trusted cybersecurity advisories and update defenses accordingly.
---
Sources:
https://www.redhotcyber.com/
Sources used for this article
securityweek.com, BleepingComputer, Multiple verified sources, securityboulevard.com, cyberscoop.com, redhotcyber.com
- https://www.securityweek.com/critical-cpanel-whm-vulnerability-exploited-as-zero-day-for-months/
- https://www.bleepingcomputer.com/news/security/critical-cpanel-and-whm-bug-exploited-as-a-zero-day-poc-now-available/
- https://securityboulevard.com/2026/04/imperva-customers-protected-against-cve-2026-41940-in-cpanel-whm/
- https://cyberscoop.com/cpanel-authentication-bypass-vulnerability-cve-2026-41940-exploited/
- https://www.redhotcyber.com/
