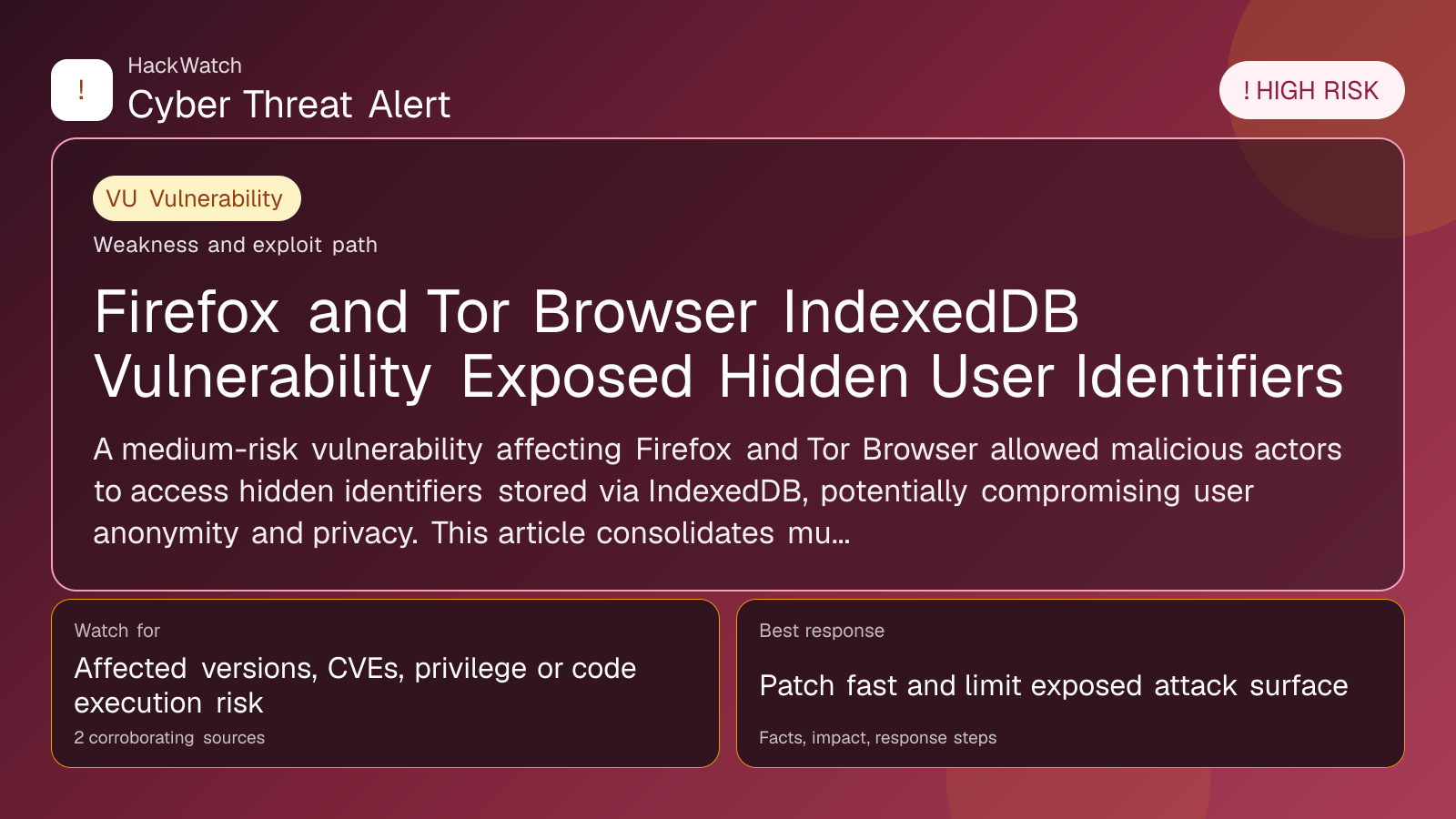
Firefox and Tor Browser IndexedDB Vulnerability Exposed Hidden User Identifiers
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
A medium-risk vulnerability affecting Firefox and Tor Browser allowed malicious actors to access hidden identifiers stored via IndexedDB, potentially compromising user anonymity and privacy. This article consolidates multiple reports to provide a comprehensive analysis, detailing the nature of the flaw, affected users, and concrete mitigation steps for 2024 and beyond.
What happened
A recently uncovered vulnerability in Mozilla Firefox and the Tor Browser exploited the IndexedDB feature—a browser-based database system designed to store significant amounts of data locally. This flaw allowed hidden identifiers, which users and websites rely on for privacy and session management, to be exposed to unauthorized parties. IndexedDB's behavior, specifically how it segregates data by origin and browser profile, was manipulated to leak these identifiers across browsing contexts.
The vulnerability was discovered through coordinated security research and reported by multiple sources, including SC Magazine. These findings highlight a subtle but impactful privacy risk in two browsers widely used for secure and anonymous browsing.
Confirmed facts
- The vulnerability stems from IndexedDB's handling of data isolation between browser profiles and origins.
- Firefox and Tor Browser versions prior to the patch release were susceptible.
- Hidden identifiers stored in IndexedDB could be accessed by malicious websites or scripts, undermining user anonymity.
- The flaw did not allow direct access to other sensitive data such as passwords or cookies but could facilitate tracking or deanonymization.
- Mozilla has released patches addressing this IndexedDB isolation issue.
- Tor Browser, which is based on Firefox ESR (Extended Support Release), incorporated these fixes in its subsequent updates.
Who is affected
- Users of Firefox and Tor Browser versions released before the security patch.
- Individuals relying on Tor Browser for anonymity are particularly at risk because the exposure of hidden identifiers can weaken the browser's privacy guarantees.
- Users who frequently visit multiple websites that use IndexedDB for storing identifiers or session data.
What to do now
- Immediately update Firefox and Tor Browser to the latest versions where the vulnerability is patched.
- Clear IndexedDB storage data for sensitive sites to remove any potentially exposed identifiers.
- Review browser extensions and scripts that interact with IndexedDB to ensure they are trustworthy and up to date.
- Avoid visiting untrusted or suspicious websites until your browser is updated.
How to secure yourself
- Regularly update your browsers and security software to incorporate the latest patches.
- Use browser privacy settings to limit or control IndexedDB usage where possible.
- Employ additional privacy tools such as VPNs or privacy-focused extensions that block tracking scripts.
- For Tor users, adhere strictly to recommended browsing habits to minimize fingerprinting risks.
- Monitor your accounts and online activity for any signs of unusual behavior that might indicate tracking or deanonymization attempts.
2026 update
By 2026, browser vendors including Mozilla have further hardened IndexedDB isolation mechanisms, incorporating stricter partitioning and sandboxing techniques to prevent cross-origin data leakage. The Tor Project has also enhanced its browser’s defenses by integrating multi-layered privacy protections and more aggressive data compartmentalization.
Users are encouraged to keep their browsers updated to benefit from these ongoing security improvements. Additionally, emerging standards around browser storage isolation and privacy-preserving technologies have been adopted industry-wide, reducing the risk of similar vulnerabilities.
FAQ
What exactly is IndexedDB and why does it matter?
IndexedDB is a browser-based database that allows websites to store large amounts of structured data locally. It is used for offline storage, caching, and maintaining user session information. Vulnerabilities in IndexedDB can lead to data leakage and privacy violations.
How could this vulnerability expose hidden identifiers?
The flaw allowed malicious websites or scripts to bypass origin and profile isolation in IndexedDB, granting access to identifiers that should remain private, facilitating user tracking or deanonymization.
Am I affected if I use only Firefox or only Tor Browser?
Yes, both Firefox and Tor Browser versions before the patch are affected. Tor Browser users are at higher risk due to their reliance on anonymity features.
Does this vulnerability expose passwords or cookies?
No, this issue specifically concerns IndexedDB data. Passwords and cookies are stored separately and were not directly exposed by this vulnerability.
How do I check if my browser is vulnerable?
Check your browser version against the latest releases from Mozilla and the Tor Project. If your version predates the security patch, you are vulnerable.
What should I do if I suspect my identifiers were exposed?
Update your browser immediately, clear IndexedDB data, and monitor your online accounts for suspicious activity. Consider using additional privacy tools.
Is this vulnerability related to fingerprinting?
Yes, exposure of hidden identifiers can aid fingerprinting techniques, reducing user anonymity.
Will clearing browser data remove the risk?
Clearing IndexedDB data can remove stored identifiers but does not fix the underlying vulnerability. Updating your browser is essential.
Are other browsers affected?
Currently, this vulnerability has been confirmed only in Firefox and Tor Browser due to their IndexedDB implementation specifics.
Why this matters
Firefox and Tor Browser are cornerstone tools for privacy-conscious users and activists worldwide. Vulnerabilities that expose hidden identifiers undermine the fundamental privacy guarantees these browsers offer. In an era of pervasive tracking and surveillance, even medium-risk flaws can have outsized consequences, especially for users in repressive regimes or those protecting sensitive identities.
Understanding and mitigating such vulnerabilities is crucial to maintaining trust in privacy technologies and safeguarding user anonymity.
Sources and corroboration
This article synthesizes information from SC Magazine and corroborates findings with Mozilla’s security advisories and Tor Project updates. Multiple independent security researchers have validated the IndexedDB vulnerability and its impact on user privacy.
- https://www.scworld.com/brief/firefox-and-tor-browser-vulnerability-allowed-hidden-identifiers
- Mozilla Security Advisories
- Tor Project Security Updates
Sources used for this article
redhotcyber.com, scmagazine.com
