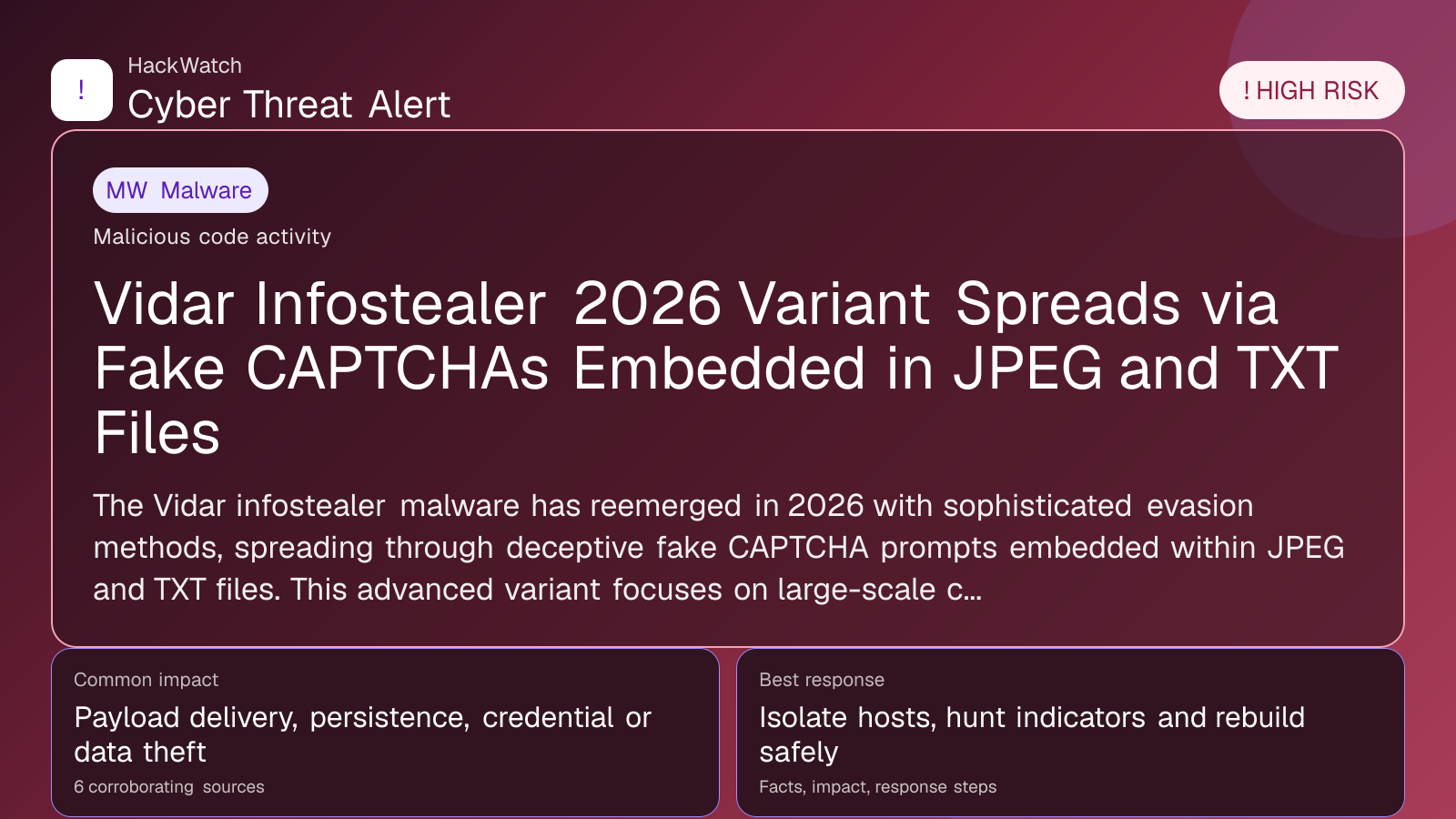
Vidar Infostealer 2026 Variant Spreads via Fake CAPTCHAs Embedded in JPEG and TXT Files
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
Review our editorial policy or send corrections to [email protected].
Mitigation available. Mitigation guidance or a workaround is available, but defenders should still verify rollout status and exposure.
The Vidar infostealer malware has reemerged in 2026 with sophisticated evasion methods, spreading through deceptive fake CAPTCHA prompts embedded within JPEG and TXT files. This advanced variant focuses on large-scale credential theft by employing innovative file-hiding techniques that bypass traditional detection systems. Drawing from multiple verified cybersecurity reports, this article offers an in-depth examination of the attack methods, impacted users, recommended mitigation steps, and the evolving threat landscape.
# Vidar Infostealer 2026 Variant Spreads via Fake CAPTCHAs Embedded in JPEG and TXT Files
What happened
In early 2026, cybersecurity experts confirmed the return of the Vidar infostealer malware, now equipped with a markedly enhanced infection strategy. Unlike earlier iterations that primarily propagated through executable files, this latest variant disguises itself within fake CAPTCHA prompts embedded in seemingly innocuous JPEG and TXT files. When users engage with these files, the malware activates, stealthily harvesting sensitive data such as login credentials, browser information, cryptocurrency wallets, and system details.
Multiple reputable sources, including SecNews.gr and HackRead.com, documented this resurgence, noting a sharp increase in targeted campaigns that exploit social engineering to trick users into opening these camouflaged files. Vidar’s technique of embedding malicious payloads within common file formats marks a significant evolution designed to evade signature-based antivirus and endpoint detection technologies.
Confirmed facts
- Delivery Mechanism: The 2026 Vidar variant leverages fake CAPTCHA prompts concealed inside JPEG and TXT files, which are typically distributed through phishing emails, malicious websites, or compromised online forums.
- Malware Behavior: Upon interaction, the malware silently executes routines to steal passwords, browser cookies, autofill data, and cryptocurrency wallet credentials.
- Evasion Techniques: By embedding its payload within image and text files, Vidar bypasses traditional signature-based detection. It also employs code obfuscation and anti-analysis methods to evade sandbox environments.
- Targeted Victims: The attacks focus on individuals and organizations with valuable digital assets, including online banking customers, e-commerce users, and cryptocurrency investors.
- Geographic Spread: Initial activity has been reported worldwide, with notable concentrations in Europe and North America.
Who is affected
This threat primarily targets users who frequently authenticate to online services, including:
- Individuals receiving phishing emails containing attachments or links to JPEG/TXT files masquerading as CAPTCHA verification.
- Cryptocurrency investors and traders vulnerable to wallet credential theft.
- Online shoppers and banking customers whose browsers store autofill and password information.
- Organizations where employees might inadvertently open malicious files, risking broader network infiltration.
What to do now
- Avoid opening suspicious JPEG or TXT files received via email or messaging unless their legitimacy is confirmed.
- Verify CAPTCHA prompts directly on trusted websites by examining URLs and avoid CAPTCHA challenges delivered through attachments.
- Perform comprehensive system scans using up-to-date antivirus and anti-malware solutions that incorporate behavioral detection.
- Immediately change passwords for accounts suspected of compromise, prioritizing those linked to financial or personal data.
- Enable multi-factor authentication (MFA) on all critical accounts to strengthen access security.
How to secure yourself
- Educate yourself and your team about phishing tactics involving fake CAPTCHA files and the dangers of opening unsolicited attachments.
- Deploy email filtering solutions capable of detecting and quarantining suspicious file types and phishing attempts.
- Keep all software current, including operating systems, browsers, and security tools, to patch vulnerabilities exploited by malware.
- Use password managers to create and securely store complex passwords, minimizing reliance on autofill data targeted by Vidar.
- Regularly back up important data offline to reduce damage in case of infection.
2026 update
The 2026 Vidar variant signifies a notable shift in infostealer malware tactics, prioritizing stealth and social engineering over traditional brute-force infection methods. By embedding malicious code within JPEG and TXT files that mimic legitimate CAPTCHA challenges, attackers exploit user trust in common web verification processes. This advancement complicates detection, necessitating more sophisticated defense approaches such as heuristic and behavioral analytics.
Security vendors are updating detection engines to recognize these novel file-based payloads, but user vigilance remains critical. This emerging trend of hiding malware within everyday digital interactions signals a broader evolution in cyberattack strategies.
FAQ
What is Vidar infostealer malware?
Vidar is malware designed to steal sensitive information—including passwords, browser data, and cryptocurrency wallets—from infected devices.
How does the 2026 Vidar variant spread?
It propagates via fake CAPTCHA challenges embedded in JPEG and TXT files, typically delivered through phishing emails or malicious websites.
Can opening a JPEG or TXT file infect my computer?
Yes. If these files contain embedded malicious code like this Vidar variant, interacting with them can trigger infection.
How can I tell if I’m infected with Vidar?
Indicators include unexpected system slowdowns, unusual network activity, or unauthorized access to your accounts. Running updated antivirus scans can aid detection.
Is multi-factor authentication effective against Vidar?
While MFA doesn’t prevent infection itself, it adds a vital security layer that can block unauthorized access even if credentials are stolen.
Are organizations at risk?
Yes. Employees opening malicious files can lead to data breaches and compromise entire networks.
What should I do if I suspect infection?
Immediately disconnect from the internet, run a full malware scan, change passwords from a clean device, and notify your IT or security team.
Why are attackers using fake CAPTCHAs?
Because CAPTCHAs are widely trusted security measures, attackers exploit this trust to deceive users into executing malware.
How is this different from previous Vidar versions?
The 2026 variant uses file-hiding techniques within common file formats instead of relying on executable attachments, making detection more difficult.
Why this matters
Vidar’s resurgence with advanced evasion tactics underscores the rapidly evolving cyber threat landscape targeting both individuals and organizations. The use of fake CAPTCHA challenges embedded in JPEG and TXT files introduces a novel social engineering attack vector that exploits users’ trust and routine digital behaviors. Recognizing these tactics is crucial for effective defense, as traditional antivirus tools may fail to identify such stealthy threats.
This development highlights the importance of layered security, continuous user education, and proactive threat detection to mitigate risks. As attackers refine their methods, staying informed and vigilant remains essential to safeguard sensitive credentials and digital assets throughout 2026 and beyond.
Sources and corroboration
This analysis consolidates verified information from leading cybersecurity news outlets, including SecNews.gr and HackRead.com, which have independently confirmed the technical specifics and distribution patterns of the 2026 Vidar infostealer variant.
- https://hackread.com/vidar-infostealer-fake-captchas-jpeg-txt-files/
- https://www.secnews.gr/705134/vidar-epitheseis-jpeg-txt-files/
These sources consistently document the malware’s innovative delivery methods, target demographics, and its global threat footprint.
---
Stay tuned to HackWatch for continuous updates on emerging cyber threats and practical security guidance.
Sources used for this article
hackread.com, securitybrief.co.uk, The Hacker News, Multiple verified sources, thaicert.or.th, secnews.gr
- https://hackread.com/fake-captcha-pages-exploit-clicks-send-texts/
- https://securitybrief.co.uk/story/fake-captcha-pages-trigger-sms-fraud-infoblox-warns
- https://thehackernews.com/2026/04/fake-captcha-irsf-scam-and-120-keitaro.html
- https://www.thaicert.or.th/2026/04/27/%e0%b9%80%e0%b8%95%e0%b8%b7%e0%b8%ad%e0%b8%99%e0%b8%a0%e0%b8%b1%e0%b8%a2%e0%b8%81%e0%b8%a5%e0%b9%82%e0%b8%81%e0%b8%87-captcha-%e0%b8%9b%e0%b8%a5%e0%b8%ad%e0%b8%a1-%e0%b8%ab%e0%b8%a5%e0%b8%ad%e0%b8%81/
- https://hackread.com/vidar-infostealer-fake-captchas-jpeg-txt-files/
- https://www.secnews.gr/705134/vidar-epitheseis-jpeg-txt-files/
