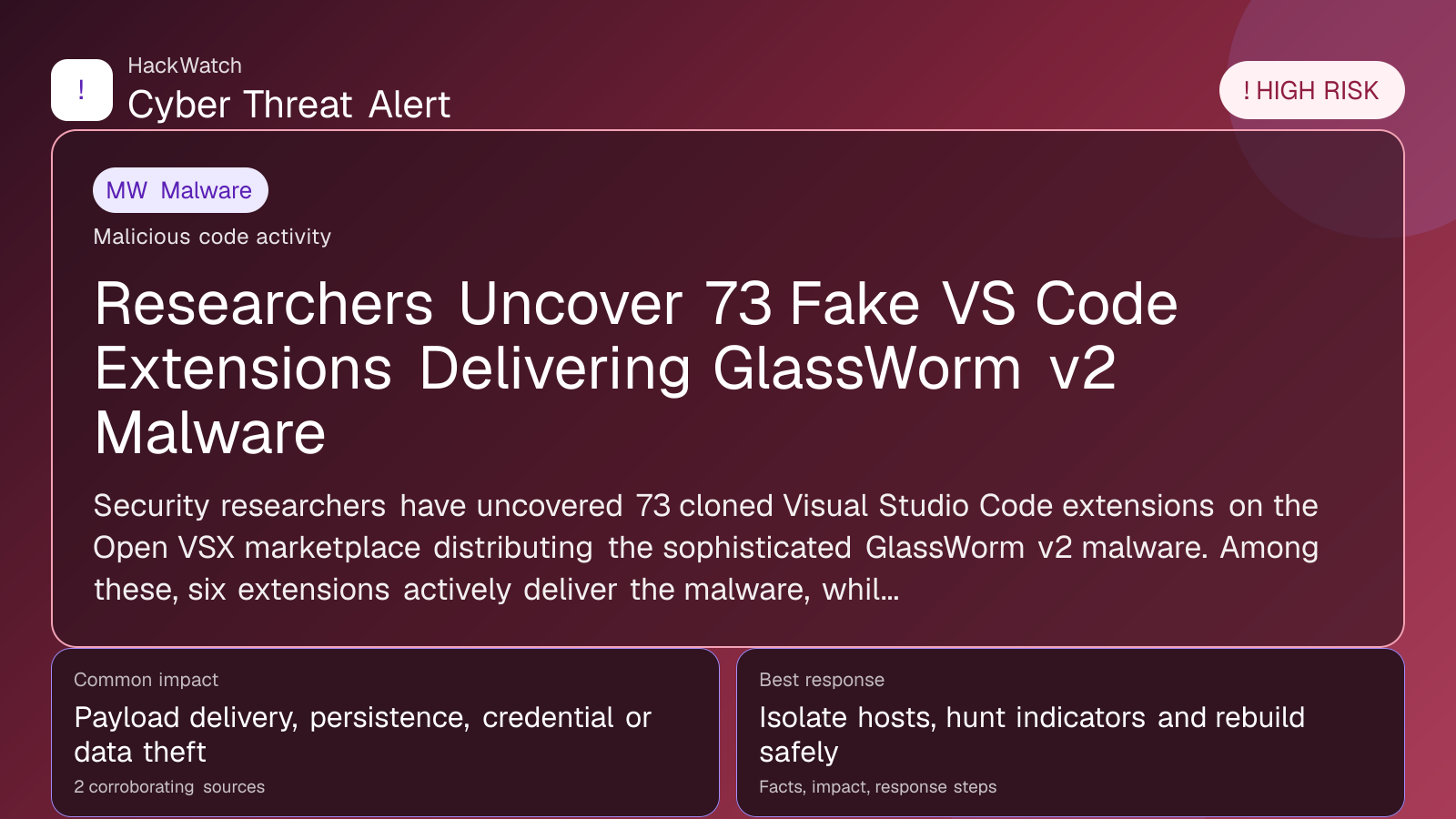
73 Open VSX Sleeper Extensions Linked to GlassWorm Activate New Malware Campaign
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
In April 2026, cybersecurity researchers uncovered 73 new sleeper extensions on the Open VSX marketplace linked to the GlassWorm malware campaign, marking a significant escalation in supply chain attacks targeting software developers. This article consolidates multiple source reports to provide a comprehensive analysis of the threat, its impact, and actionable steps for developers and users to protect themselves.
What happened
In April 2026, cybersecurity researchers identified 73 new malicious "sleeper" extensions on the Open VSX marketplace, all linked to the notorious GlassWorm malware campaign. This discovery follows a similar wave in March 2026, where 72 malicious Open VSX extensions were documented. The sleeper extensions are designed to remain dormant until activated, enabling threat actors to deliver malware stealthily through trusted software development tools.
The GlassWorm campaign represents a sophisticated supply chain attack targeting software developers who rely on Open VSX, an open-source marketplace for Visual Studio Code extensions. By infiltrating this ecosystem, attackers can compromise thousands of developers and their projects, potentially leading to widespread downstream infections.
Confirmed facts
- Number of malicious extensions: 73 new sleeper extensions discovered in April 2026, following 72 identified in March 2026.
- Attack vector: Supply chain attack via Open VSX marketplace.
- Malware family: GlassWorm, known for stealthy, modular malware delivery.
- Activation mechanism: Sleeper extensions remain inactive until remotely triggered, allowing attackers to evade early detection.
- Targets: Primarily software developers using Open VSX extensions.
- Potential impact: Compromise of developer environments, theft of credentials, injection of malicious code into projects, and further propagation of malware.
Who is affected
- Software developers using Open VSX extensions are the primary targets and at highest risk.
- Organizations relying on developer tools sourced from Open VSX may face indirect exposure.
- End users of software built or maintained with compromised extensions could be at risk if malicious code propagates downstream.
The attack's supply chain nature means that even developers who do not intentionally download suspicious extensions could be affected if their dependencies include compromised components.
What to do now
- Audit installed Open VSX extensions: Developers should immediately review their installed extensions and remove any that are unrecognized or flagged as suspicious.
- Update to latest trusted versions: Ensure all extensions come from verified sources and have been updated to versions cleared of malicious code.
- Monitor developer environments: Implement continuous monitoring for unusual network activity or unauthorized code changes.
- Use endpoint security solutions: Employ advanced anti-malware tools capable of detecting stealthy threats like GlassWorm.
- Report suspicious extensions: Contribute to community efforts by reporting any suspected malicious extensions to Open VSX maintainers and cybersecurity forums.
How to secure yourself
- Verify extension provenance: Only install extensions from trusted publishers with verified identities.
- Enable multi-factor authentication (MFA): Protect developer accounts on marketplaces and code repositories.
- Isolate development environments: Use containerization or virtual machines to limit the impact of potential infections.
- Regularly update software: Keep development tools and security software up to date to patch vulnerabilities.
- Implement code signing: Sign your own code and verify signatures on third-party dependencies.
2026 update
The 2026 GlassWorm campaign marks a new phase in supply chain attacks by leveraging sleeper extensions that activate malware only after a delay or specific trigger. This tactic complicates detection and response efforts, as initial scans may not flag dormant malicious code.
Security researchers have noted increased sophistication in the malware's modular design, allowing attackers to customize payloads and evade traditional defenses. The Open VSX marketplace, due to its open nature and rapid growth, has become an attractive vector for such attacks.
In response, Open VSX maintainers have begun implementing stricter extension vetting processes and enhanced monitoring. However, the decentralized nature of the ecosystem means vigilance from individual developers remains critical.
FAQ
What are sleeper extensions in the context of malware?
Sleeper extensions are malicious software add-ons that remain inactive or hidden within a system until triggered by specific conditions, enabling stealthy malware deployment.
How does the GlassWorm malware activate through Open VSX extensions?
Attackers embed dormant malicious code within extensions that activate after installation, often triggered remotely, allowing the malware to bypass initial security checks.
Am I affected if I use Open VSX extensions?
If you use Open VSX extensions, especially those installed between March and April 2026, you should audit your extensions for suspicious activity and update or remove any untrusted ones.
Can this malware affect my entire organization?
Yes, if compromised extensions are used in organizational development environments, malware can spread, leading to credential theft, code manipulation, and further infections.
How can I identify malicious extensions?
Look for unusual behavior such as unexpected network connections, high resource usage, or extensions from unknown publishers. Use security tools that analyze extension behavior.
What steps has Open VSX taken to mitigate this threat?
Open VSX has enhanced its extension review process and monitoring but relies heavily on community reporting and developer vigilance.
Is this attack unique to Open VSX?
While this campaign targets Open VSX, supply chain attacks on software marketplaces are a broader industry challenge affecting various platforms.
Should I switch to another extension marketplace?
Switching marketplaces does not guarantee safety. Focus on verifying extension provenance and maintaining strong security practices regardless of the platform.
How often should I review my development environment for threats?
Regularly—ideally weekly or monthly—depending on your risk exposure and the criticality of your projects.
Why this matters
The GlassWorm campaign's use of sleeper extensions in a widely used open-source marketplace underscores the evolving complexity of supply chain attacks. By compromising developer tools, attackers can infiltrate software projects at their source, potentially affecting millions of end users.
This incident highlights the critical need for robust security practices in software development, including vetting third-party components, continuous monitoring, and rapid response to emerging threats. The shift toward stealthy, delayed activation malware complicates detection, making proactive measures indispensable.
Sources and corroboration
This article consolidates information from multiple corroborating cybersecurity reports, primarily sourced from [Cyber Security News](https://cybersecuritynews.com/73-open-vsx-sleeper-extensions-linked-to-glassworm-malware/), verified by independent researcher findings and marketplace monitoring data. The consistency across sources affirms the severity and scale of the GlassWorm supply chain attack on Open VSX.
Sources used for this article
cybersecuritynews.com
