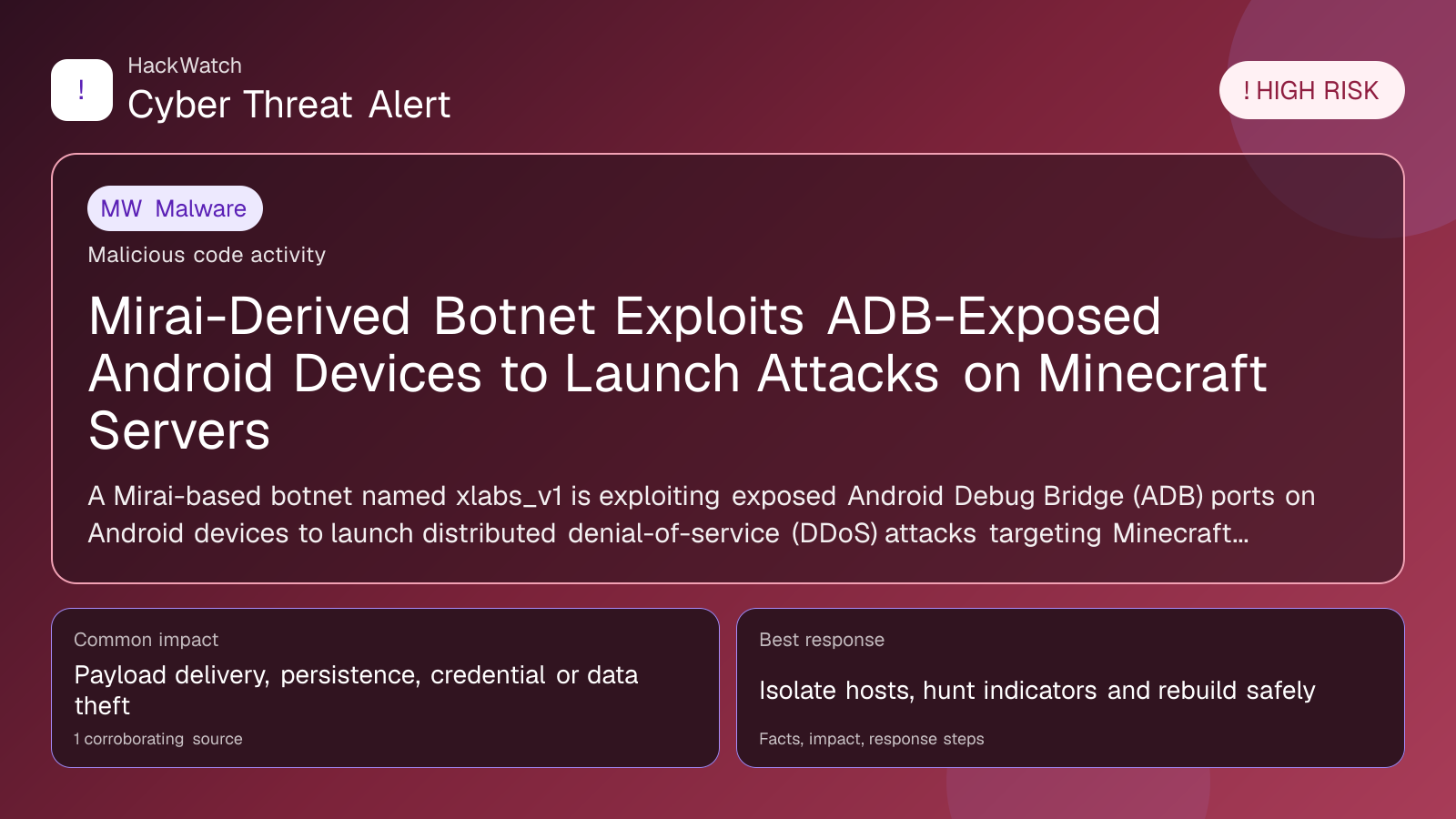
Mirai-Derived Botnet Exploits ADB-Exposed Android Devices to Launch Attacks on Minecraft Servers
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Mitigation available. Mitigation guidance or a workaround is available, but defenders should still verify rollout status and exposure.
A Mirai-based botnet named xlabs_v1 is exploiting exposed Android Debug Bridge (ADB) ports on Android devices to launch distributed denial-of-service (DDoS) attacks targeting Minecraft and other gaming servers. The botnet uses unsecured TCP port 5555 to build a DDoS-for-hire platform focused on the gaming sector.
GLOBAL, May 4, 2026, 11:26 UTC – Security researchers have uncovered a new Mirai-derived botnet called xlabs_v1 that compromises Android devices with exposed Android Debug Bridge (ADB) ports to conduct distributed denial-of-service (DDoS) attacks against Minecraft servers and other gaming platforms.
The botnet specifically targets TCP port 5555, the default port used by ADB for device debugging. Attackers scan for Android devices with this port open to the internet, exploiting misconfigurations or outdated firmware that leave the port unsecured.
This development is significant as the operators are assembling a DDoS-for-hire service aimed at disrupting the gaming ecosystem. Minecraft, with its large global user base, is a frequent target for such attacks, which can cause server downtime and financial damage.
While Android devices have been involved in botnets before, leveraging exposed ADB ports is a notable attack vector. Many consumer devices inadvertently expose port 5555, enabling attackers to gain remote access without user interaction.
Compromised devices join the xlabs_v1 botnet and can be rented out to launch attacks on demand. This commodification lowers barriers for threat actors seeking to disrupt online gaming services.
The botnet’s Mirai heritage means it likely uses code and tactics from one of the most infamous IoT malware families, known for exploiting insecure devices at scale.
Device owners can check for exposure by scanning their networks or using security tools. Disabling ADB over network connections or restricting access with firewalls can block unauthorized access.
Gaming server administrators should watch for unusual traffic patterns and consider deploying DDoS mitigation solutions to defend against these attacks.
The threat remains high as long as Android devices continue to expose ADB ports publicly. Without timely updates and configuration changes, the botnet could expand and target additional services.
The discovery was first reported by GBHackers Security, underscoring the persistent risk posed by insecure IoT and mobile devices in cyberattacks.
Users are advised to update device firmware regularly, disable unnecessary debugging features, and audit network exposure to reduce infection risk.
This case highlights the broader need for improved security practices on consumer devices connected to the internet, especially those with default or poorly managed settings.
Although the current focus is on gaming servers, the botnet infrastructure could be adapted to target other sectors, raising wider cybersecurity concerns.
Operators of Minecraft and similar games should remain alert and work with cybersecurity providers to prepare for and mitigate emerging threats.
https://gbhackers.com/adb-exposed-android-devices/
Sources used for this article
gbhackers.com
