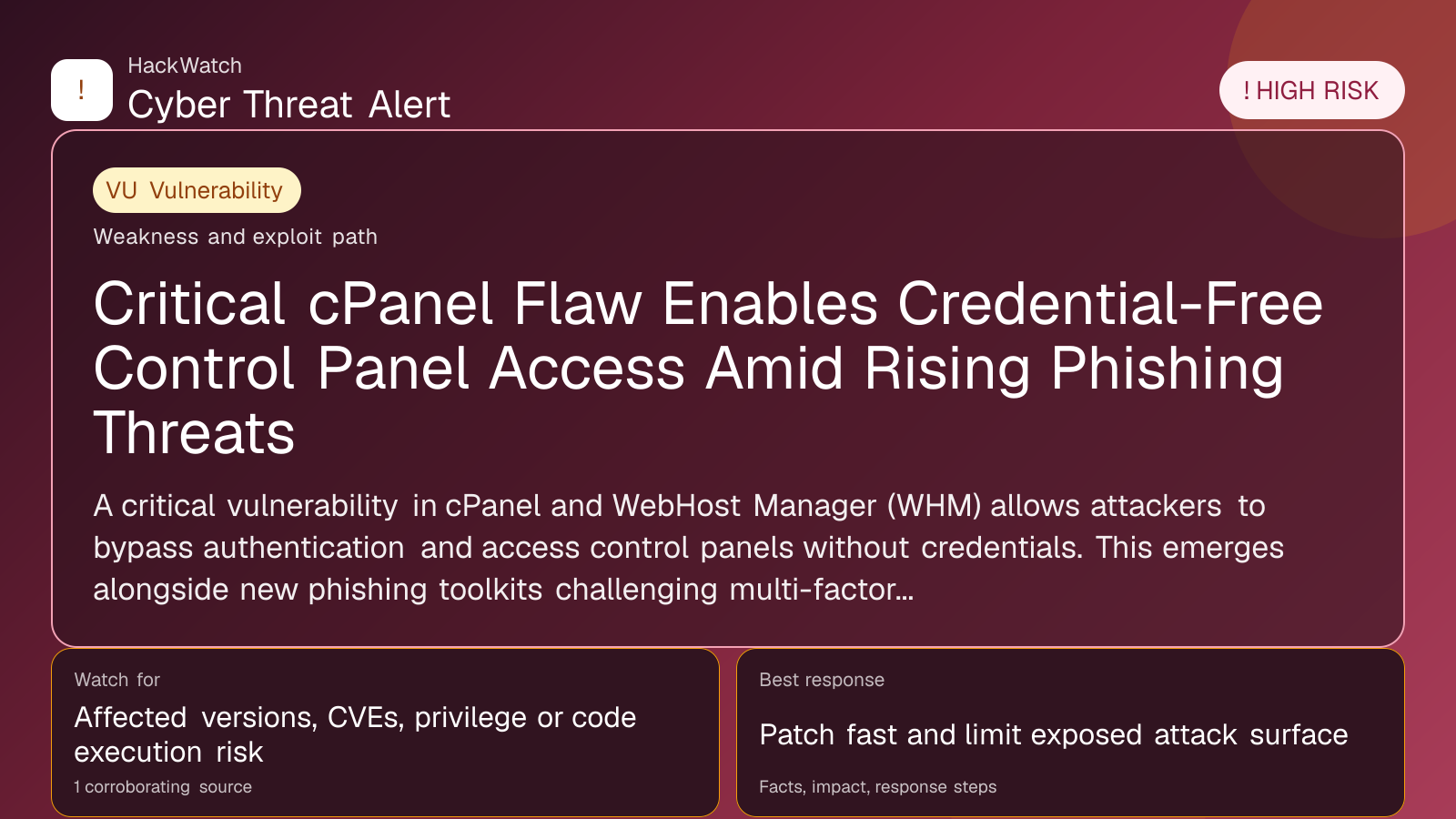
Critical cPanel Flaw Enables Credential-Free Control Panel Access Amid Rising Phishing Threats
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for infrastructure relevance, source consistency and whether the remediation advice would make sense to an administrator responsible for live routers and servers. His note keeps the action list grounded: validate scope, reduce exposed management paths, keep evidence intact and avoid claims that go beyond the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A critical vulnerability in cPanel and WebHost Manager (WHM) allows attackers to bypass authentication and access control panels without credentials. This emerges alongside new phishing toolkits challenging multi-factor authentication (MFA) effectiveness.
GLOBAL, May 4, 2026, 10:13 UTC
A critical security flaw in cPanel and WebHost Manager (WHM) has been discovered that permits attackers to bypass authentication and gain unauthorized access to web hosting control panels. The vulnerability affects nearly all versions in use, raising urgent concerns for millions of websites relying on these platforms.
The flaw enables attackers to circumvent login requirements entirely, potentially allowing full control over hosting environments. This could lead to website defacement, data theft, or deployment of malicious content without the need for valid credentials.
This development comes amid a surge in sophisticated phishing campaigns. A recently surfaced phishing-as-a-service toolkit named EvilTokens, active since February 2026, exploits social engineering to defeat multi-factor authentication (MFA), traditionally considered a strong security barrier.
Security researchers warn that the combination of this cPanel vulnerability and advanced phishing tools significantly raises the risk profile for website operators and their users. Attackers can leverage these weaknesses to infiltrate systems and maintain persistent access.
Meta’s recent infrastructure expansion, powered by Amazon’s AWS Graviton processors, underscores the growing reliance on cloud resources that must be secured against such threats. Meanwhile, the cybercrime underground continues to evolve rapidly, with new tactics emerging daily.
The timing is critical as the vulnerability was publicly noted shortly after a reported supply chain attack on SAP’s package management system, attributed to the TeamPCP group. These incidents highlight the expanding attack surface in software supply chains and hosting platforms.
Website administrators using cPanel or WHM are urged to apply patches immediately once available and review access logs for suspicious activity. Enhanced monitoring and incident response plans should be prioritized.
Given the demonstrated limits of MFA against phishing toolkits like EvilTokens, organizations should consider additional layers of defense such as hardware security keys, behavioral analytics, and user training to mitigate social engineering risks.
Legal and regulatory scrutiny may intensify as courts, like a recent Chinese labor tribunal ruling involving AI replacement disputes, increasingly address technology’s impact on security and employment.
The evolving threat landscape demands vigilance. Users should verify communications carefully and avoid clicking links or downloading attachments from unknown sources.
Red Hot Cyber, the source of these reports, continues to track underground cybercriminal activity and emerging vulnerabilities, providing timely alerts to the security community.
The precise scope and exploitation status of the cPanel flaw remain under investigation. Organizations should prepare for potential follow-on attacks exploiting this weakness.
As May Day marks labor rights and collective action, cybersecurity professionals face their own battle to safeguard digital workplaces against rapidly advancing threats.
Source: https://www.redhotcyber.com/
Sources used for this article
redhotcyber.com
