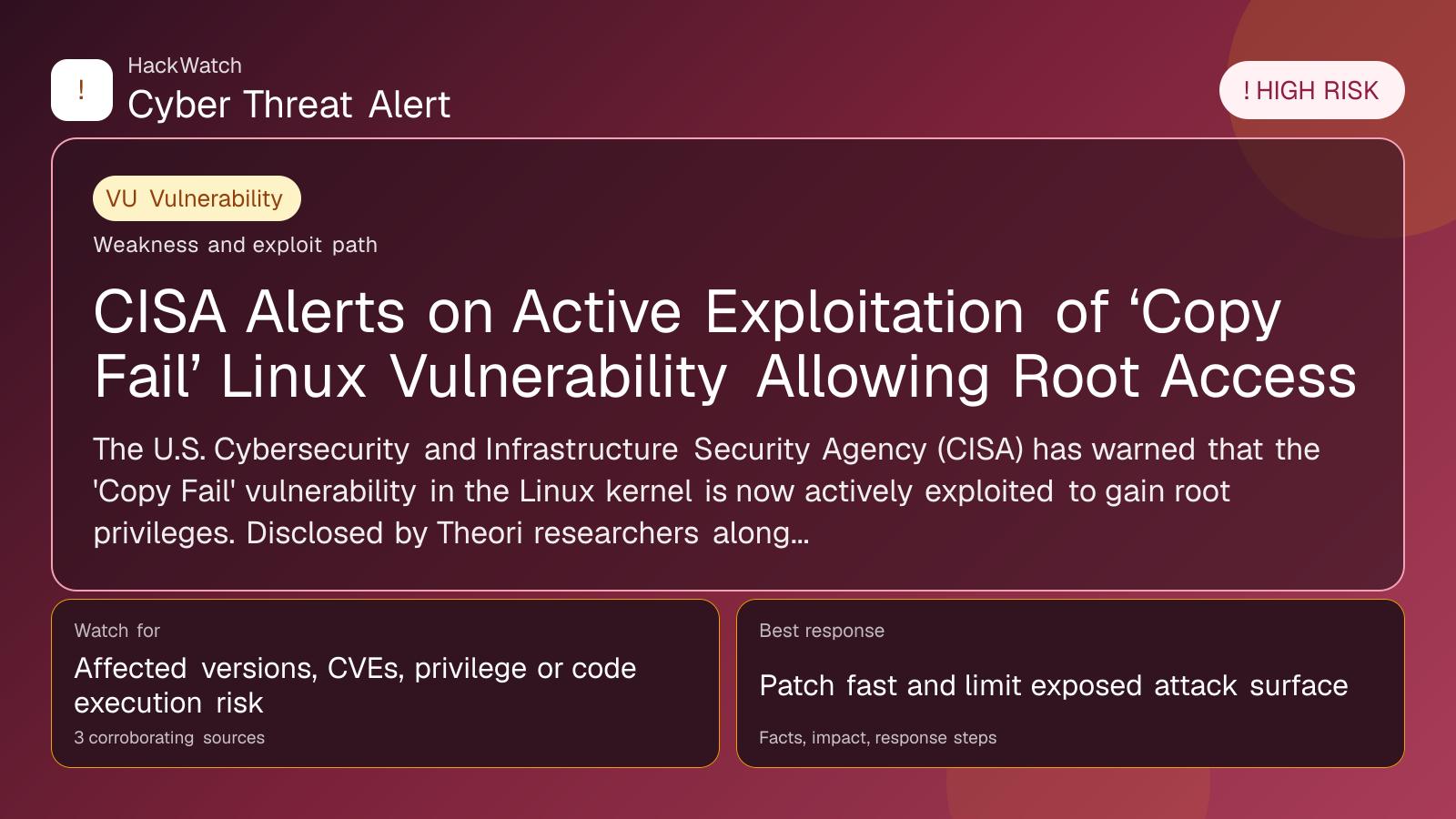
CISA Alerts on Active Exploitation of ‘Copy Fail’ Linux Vulnerability Allowing Root Access
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 3 corroborating sources.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has warned that the 'Copy Fail' vulnerability in the Linux kernel is now actively exploited to gain root privileges. Disclosed by Theori researchers alongside a proof-of-concept exploit, the flaw demands immediate patching to prevent system compromise.
WASHINGTON, May 4, 2026, 11:31 UTC
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has confirmed active exploitation of a critical Linux kernel vulnerability known as "Copy Fail." Threat actors are using this flaw to escalate privileges and gain root access on vulnerable systems.
The vulnerability was publicly disclosed by Theori researchers just one day earlier, accompanied by a proof-of-concept exploit that demonstrates how attackers can bypass security controls. The speed at which the exploit has been weaponized underscores the urgent need for system administrators to apply patches without delay.
"Copy Fail" affects the Linux kernel's handling of certain copy operations, allowing attackers to execute arbitrary code with root privileges. This grants full control over compromised machines, posing significant risks to servers and cloud infrastructure.
CISA's advisory emphasizes that exploitation is no longer theoretical. Systems running vulnerable Linux kernels, especially those exposed to internet-facing services, face immediate threats.
Following the disclosure, Linux distributions have started releasing patches to address the issue. CISA recommends prioritizing updates on critical systems that handle sensitive data or provide essential services.
Unpatched systems are at risk of unauthorized data access, system manipulation, and the installation of persistent malware. Attackers could also use the vulnerability as a foothold for wider network intrusions.
Security teams are advised to monitor logs for signs of exploitation attempts and to deploy intrusion detection systems where possible. Restricting unnecessary kernel module loading can further reduce exposure.
The rapid exploitation of "Copy Fail" reflects a broader trend of vulnerabilities being weaponized within hours of public disclosure, shrinking the window for effective defense.
While Linux remains a widely trusted platform, this incident highlights persistent challenges in securing open-source components critical to global IT infrastructure.
Organizations relying on Linux should review patch management practices and consider additional protections, such as mandatory access controls and kernel hardening measures.
CISA’s alert underscores that even mature operating systems can contain critical vulnerabilities with immediate real-world impact.
Theori researchers continue collaborating with Linux maintainers to develop comprehensive fixes and urge the community to maintain vigilance.
For now, prompt patching and vigilant monitoring remain the most effective defenses against "Copy Fail" exploitation and potential system compromise.
Sources used for this article
gbhackers.com, securityweek.com, BleepingComputer
