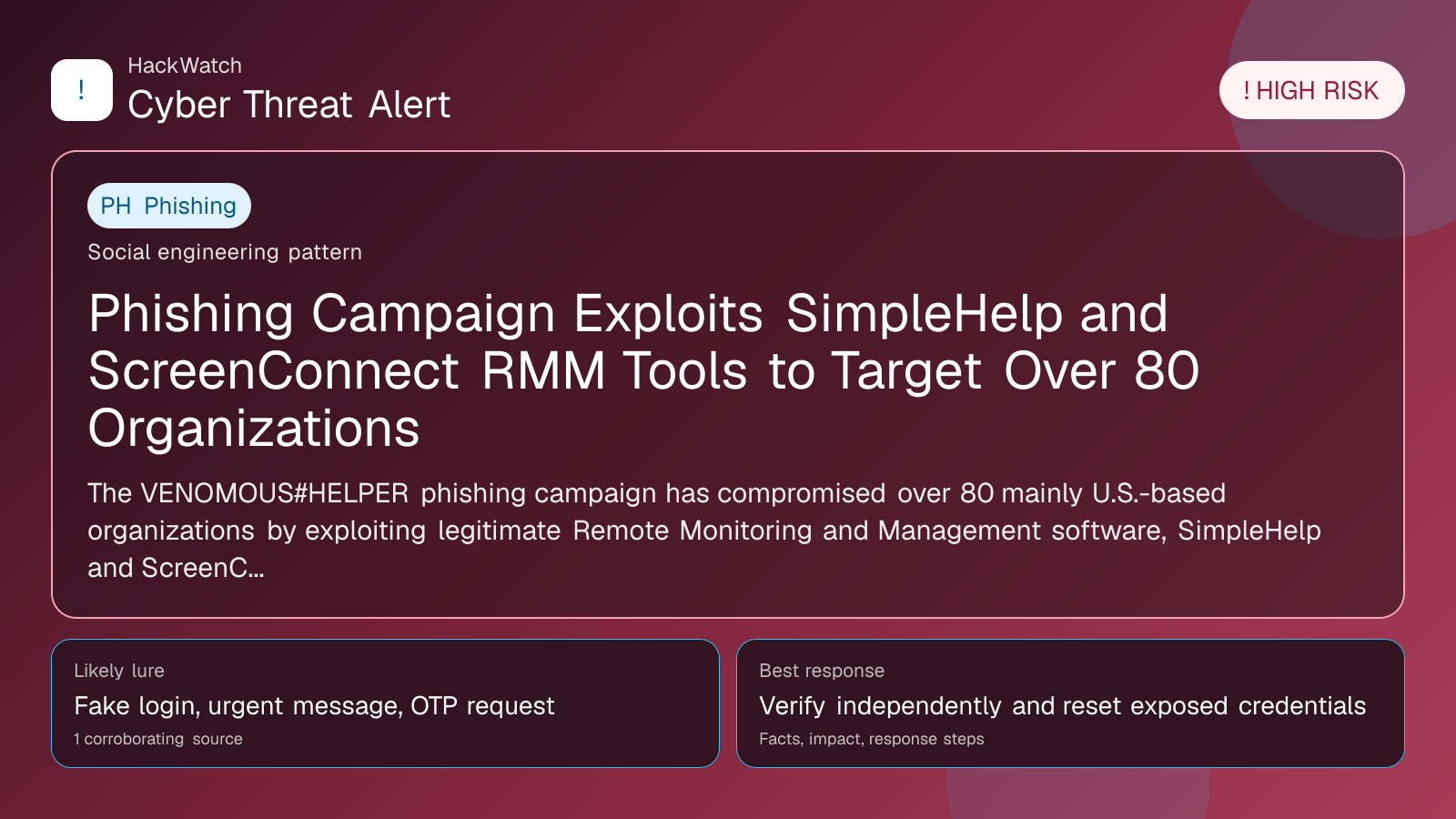
Phishing Campaign Exploits SimpleHelp and ScreenConnect RMM Tools to Target Over 80 Organizations
Verification-lure coverage focused on fake messages, cloned pages and account defense steps.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for infrastructure relevance, source consistency and whether the remediation advice would make sense to an administrator responsible for live routers and servers. His note keeps the action list grounded: validate scope, reduce exposed management paths, keep evidence intact and avoid claims that go beyond the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
The VENOMOUS#HELPER phishing campaign has compromised over 80 mainly U.S.-based organizations by exploiting legitimate Remote Monitoring and Management software, SimpleHelp and ScreenConnect, to gain persistent system access. Active since April 2025, the attackers use phishing to deploy these trusted tools and evade detection.
WASHINGTON, May 4, 2026, 18:15 UTC – More than 80 organizations, mostly in the United States, have been breached by a phishing campaign that abuses legitimate Remote Monitoring and Management (RMM) platforms to maintain persistent access, security researchers reported.
The campaign, identified as VENOMOUS#HELPER, has been active since at least April 2025. It targets a range of sectors by leveraging SimpleHelp and ScreenConnect software, tools normally used by IT departments to remotely manage devices.
Attackers send phishing emails that prompt users to install or activate these RMM applications. Once operational, the software provides continuous remote control over infected systems, allowing threat actors to evade traditional security measures.
This tactic is effective because it exploits trusted software, reducing the chance of detection by endpoint protection and network monitoring tools.
Researchers at Securonix noted overlaps between VENOMOUS#HELPER and other related attack groups, indicating a potentially coordinated campaign against enterprise environments.
Organizations employing SimpleHelp or ScreenConnect are advised to audit their RMM deployments immediately. Reviewing access logs and disabling unauthorized or unused instances can help restrict attacker persistence.
The campaign highlights the growing risk of legitimate IT management tools being weaponized. Security teams should enforce strict access controls, enable multi-factor authentication, and monitor RMM activity continuously.
While the extent of data theft or damage linked to VENOMOUS#HELPER remains uncertain, the use of persistent remote access tools raises concerns about subsequent ransomware attacks or intellectual property breaches.
Companies should also train staff to recognize phishing attempts and verify any unusual requests to install or activate remote management software.
The campaign’s duration—exceeding a year—demonstrates how threats blending into normal IT operations can evade detection for extended periods.
Security vendors and incident responders are encouraged to develop detection methods focused on identifying abnormal RMM usage patterns that may signal compromise.
As VENOMOUS#HELPER evolves, organizations must keep RMM software up to date with patches to close vulnerabilities.
This incident underscores the need for cybersecurity defenses to extend beyond malware detection and include scrutiny of legitimate applications that attackers can exploit.
Further details and indicators of compromise are provided in the Securonix advisory to assist organizations in enhancing their threat detection and response strategies.
https://thehackernews.com/2026/05/phishing-campaign-hits-80-orgs-using.html
Sources used for this article
The Hacker News
