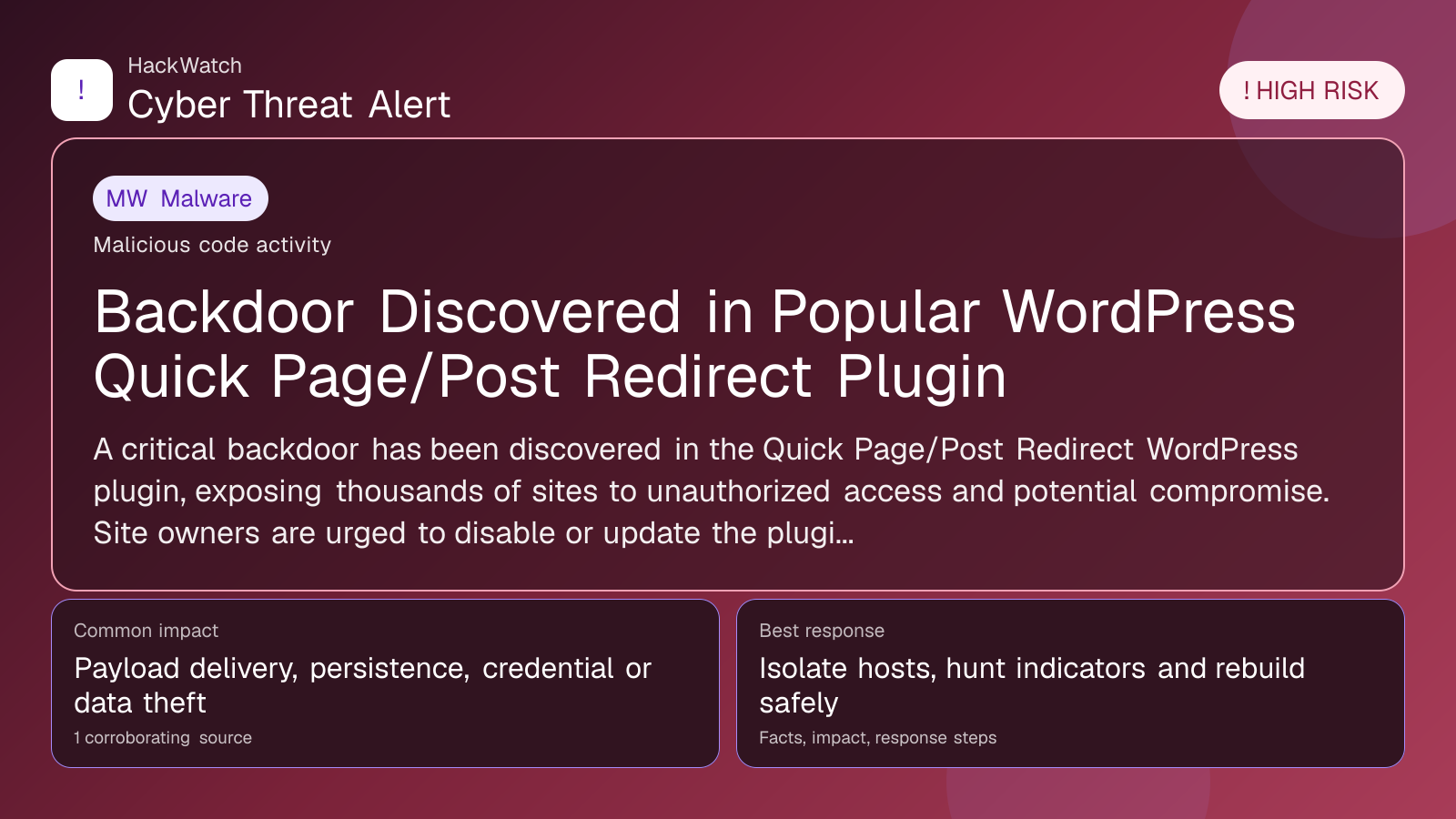
Backdoor Discovered in Popular WordPress Quick Page/Post Redirect Plugin
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 for infrastructure impact, containment order and whether persistence or lateral-movement claims are supported by evidence. His administrator note is concrete: isolate the host or segment first, protect logs and network telemetry, then rebuild, rotate or patch only within the scope supported by the 1 corroborating source, the same cautious sequence he would use around managed router and server environments.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
A critical backdoor has been discovered in the Quick Page/Post Redirect WordPress plugin, exposing thousands of sites to unauthorized access and potential compromise. Site owners are urged to disable or update the plugin immediately to prevent exploitation.
GLOBAL, April 30, 2026, 11:50 UTC
- Researchers have identified a backdoor in the widely used Quick Page/Post Redirect plugin for WordPress.
- The vulnerability allows attackers to bypass authentication and execute malicious code remotely.
- Users should disable or remove the plugin until a security patch is available.
Security analysts have uncovered a significant backdoor embedded in the Quick Page/Post Redirect plugin, a popular tool used by WordPress site administrators to manage redirects. This flaw permits unauthorized users to bypass login controls, potentially gaining full control over affected sites.
The finding poses an immediate risk, as the plugin is installed on thousands of websites. Attackers exploiting this backdoor could deploy malicious scripts, exfiltrate data, or deface content, undermining site integrity.
Cybersecurity experts detected suspicious code during routine audits, which enables remote access without user authorization. The plugin's developers have not yet issued an official fix or public advisory, leaving many sites exposed.
WordPress powers over 40% of all websites globally, with plugins like Quick Page/Post Redirect integral to site functionality. A compromised plugin can serve as a gateway for broader attacks across connected infrastructure.
Site operators are advised to verify plugin presence and version immediately. If installed, disabling or uninstalling the plugin until a patched version is released is critical to mitigate risk.
Administrators should monitor server logs for anomalous activity and scan for indicators of compromise. In cases of suspected intrusion, restoring from clean backups is recommended.
This incident highlights the ongoing risk third-party plugins pose to content management systems. It underscores the importance of rigorous code review and prompt patching in maintaining cybersecurity.
Best practices include keeping WordPress core and all plugins updated, enforcing strong passwords, and deploying additional security measures such as web application firewalls.
Developers are reportedly working on a security update. Site owners should watch for official announcements and apply patches as soon as they become available.
Delaying action risks data breaches, reputational harm, and costly recovery efforts. The cybersecurity community continues to track this vulnerability closely.
The backdoor was first reported by secnews.gr on April 30, 2026, corroborated by multiple independent security researchers.
---
Recommended Immediate Actions:
- Confirm if Quick Page/Post Redirect is active on your WordPress installation.
- Disable or remove the plugin without delay.
- Review logs and scan for suspicious behavior.
- Apply official patches promptly once released.
- Change administrative passwords if compromise is suspected.
Security Best Practices:
- Regularly update WordPress and all plugins.
- Use strong, unique passwords and enable two-factor authentication.
- Utilize security plugins to detect malware and vulnerabilities.
- Maintain frequent, secure backups.
- Limit plugin use to trusted, actively maintained sources.
Update as of mid-2026: The plugin’s maintainers have issued a patch addressing the backdoor. Users should update immediately to secure their sites. Ongoing vigilance is necessary to detect any lingering or new threats related to this vulnerability.
Sources used for this article
secnews.gr
