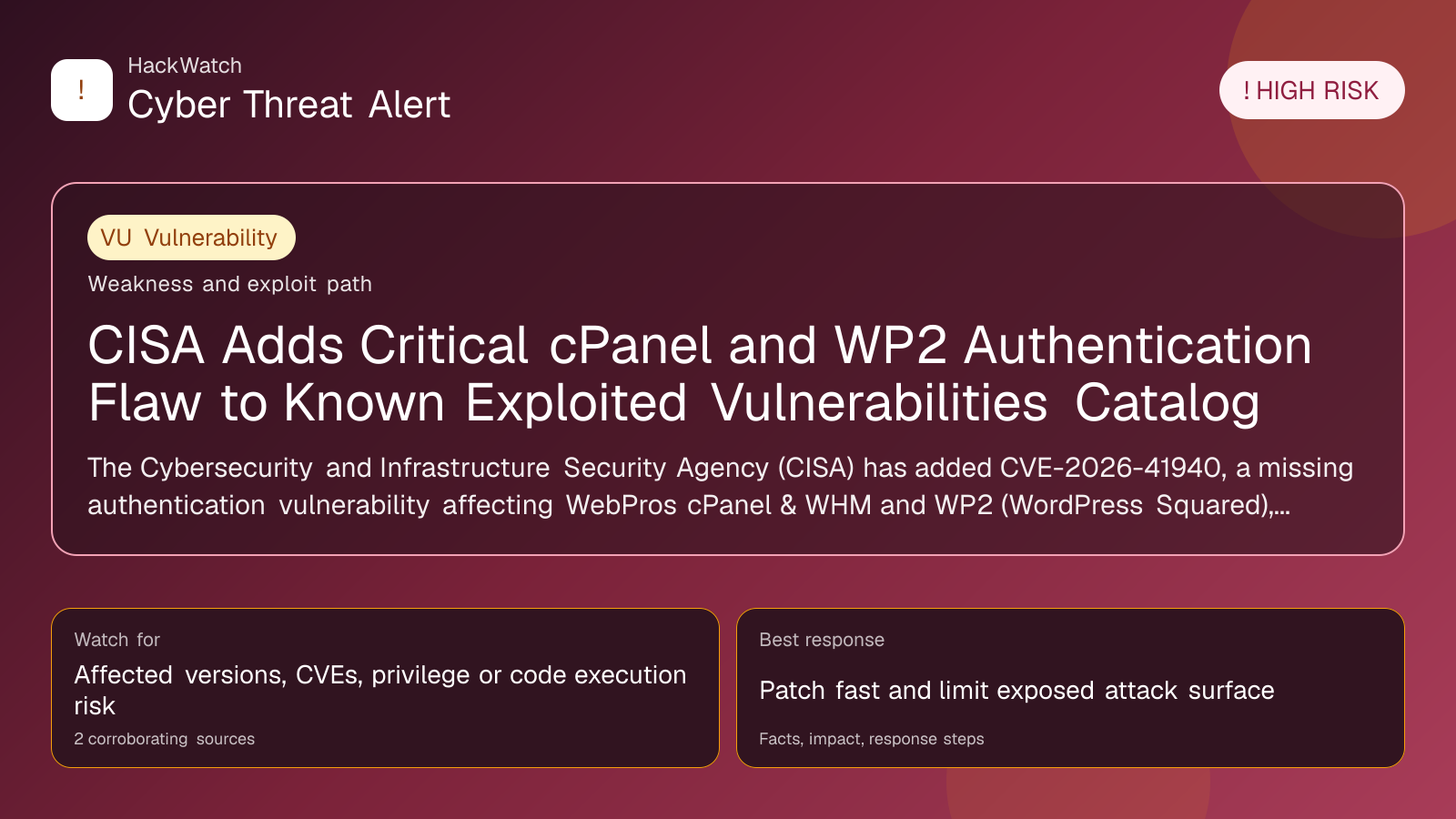
CISA Adds Critical cPanel and WP2 Authentication Flaw to Known Exploited Vulnerabilities Catalog
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 from an administrator's point of view, checking CVE-2026-41940 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 2 corroborating sources supports that scope.
Review our editorial policy or send corrections to [email protected].
Mitigation available. Mitigation guidance or a workaround is available, but defenders should still verify rollout status and exposure.
The Cybersecurity and Infrastructure Security Agency (CISA) has added CVE-2026-41940, a missing authentication vulnerability affecting WebPros cPanel & WHM and WP2 (WordPress Squared), to its Known Exploited Vulnerabilities Catalog following evidence of active exploitation. Federal agencies must address this flaw under Binding Operational Directive 22-01, while all organizations are urged to prioritize remediation to mitigate significant cyber risks.
WASHINGTON, April 30, 2026, 13:58 UTC
The Cybersecurity and Infrastructure Security Agency (CISA) has added a critical vulnerability, CVE-2026-41940, to its Known Exploited Vulnerabilities (KEV) Catalog. This flaw affects WebPros cPanel & WHM and WP2 (WordPress Squared) platforms and involves missing authentication for a critical function, enabling attackers to bypass security controls.
CISA's decision follows confirmed reports of active exploitation targeting this vulnerability. The agency emphasized the heightened risk this poses to federal networks and the broader digital ecosystem.
The inclusion of CVE-2026-41940 in the KEV Catalog triggers mandatory remediation requirements for Federal Civilian Executive Branch (FCEB) agencies under Binding Operational Directive (BOD) 22-01. This directive compels agencies to patch or mitigate listed vulnerabilities by specified deadlines to reduce exposure to active cyber threats.
While BOD 22-01 applies only to federal agencies, CISA strongly recommends that all organizations using affected platforms prioritize patching this vulnerability. Attackers frequently exploit missing authentication flaws to gain unauthorized access, potentially leading to data breaches, service disruptions, or further system compromise.
WebPros cPanel & WHM is widely used for web hosting management, while WP2 is a WordPress derivative popular for content management. The vulnerability allows threat actors to execute critical functions without proper authentication, amplifying the risk of unauthorized administrative actions.
CISA continues to update the KEV Catalog as new evidence emerges, underscoring the dynamic nature of cyber threats. Organizations are urged to integrate KEV Catalog monitoring into their vulnerability management programs to stay ahead of active exploits.
Failure to remediate such vulnerabilities promptly can result in significant operational and reputational damage. Past incidents involving similar authentication bypass flaws have led to ransomware attacks and data theft.
Security teams should verify their use of affected software versions and apply vendor patches immediately. Where patches are unavailable, implementing compensating controls such as network segmentation and enhanced monitoring can reduce risk.
The KEV Catalog serves as a critical tool for prioritizing cybersecurity efforts. Its living list reflects vulnerabilities with confirmed exploitation, helping organizations allocate resources efficiently.
Given the widespread deployment of cPanel and WordPress platforms, this vulnerability's exploitation could have far-reaching impacts beyond federal networks.
CISA's alert and the KEV Catalog update are accessible on the agency's website, providing detailed guidance on mitigation steps.
Organizations should also review their incident response plans to prepare for potential exploitation attempts targeting this vulnerability.
The evolving threat landscape demands continuous vigilance. Incorporating KEV Catalog advisories into routine security assessments is essential for proactive defense.
In summary, CVE-2026-41940 represents a high-risk vulnerability requiring immediate attention from federal agencies and private sector users alike.
Failure to act swiftly could expose critical infrastructure and sensitive data to malicious actors exploiting authentication weaknesses.
Source: https://www.cisa.gov/news-events/alerts/2026/04/30/cisa-adds-one-known-exploited-vulnerability-catalog
Sources used for this article
securityweek.com, cisa.gov
