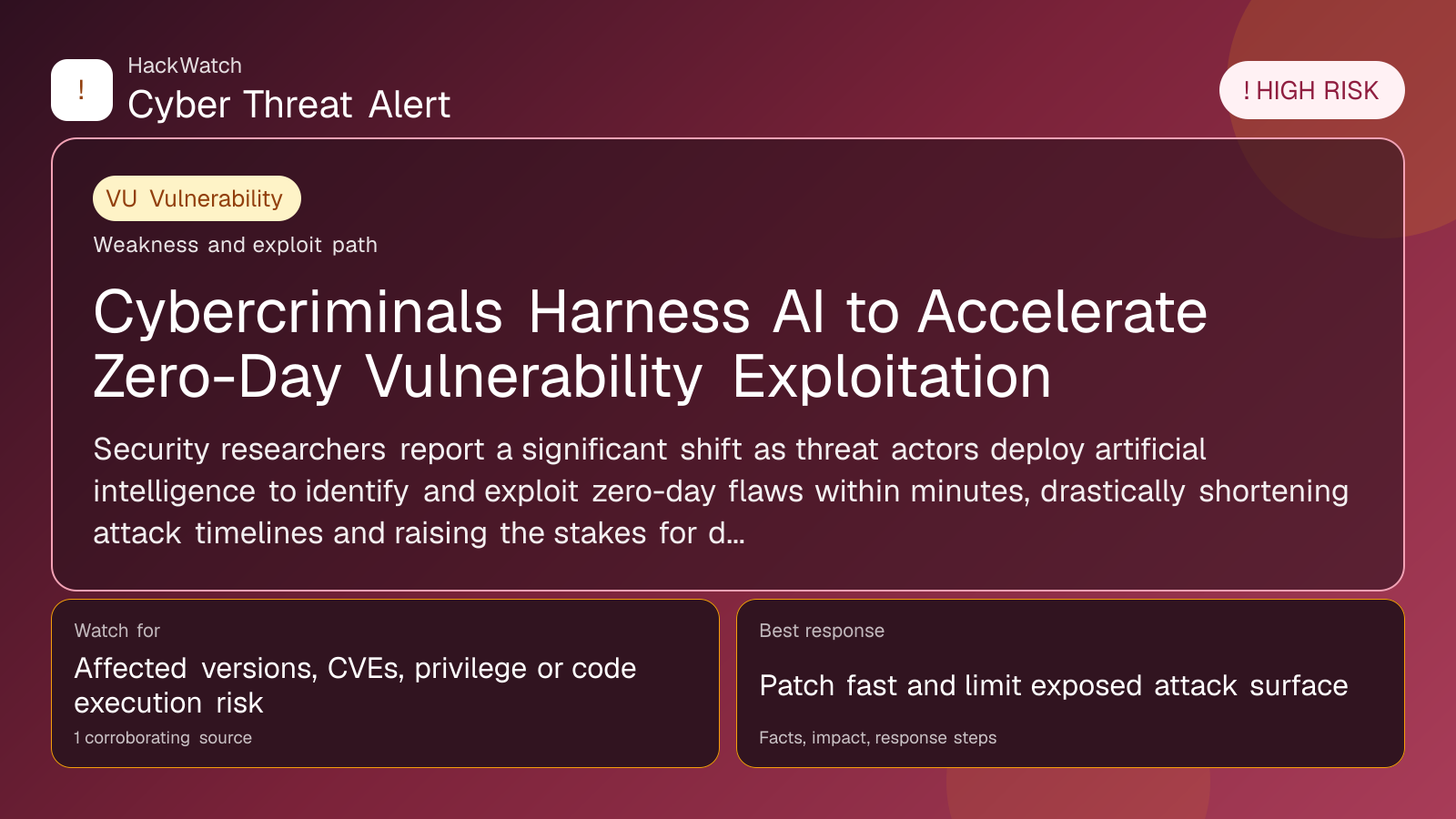
Cybercriminals Harness AI to Accelerate Zero-Day Vulnerability Exploitation
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 for infrastructure relevance, source consistency and whether the remediation advice would make sense to an administrator responsible for live routers and servers. His note keeps the action list grounded: validate scope, reduce exposed management paths, keep evidence intact and avoid claims that go beyond the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
Security researchers report a significant shift as threat actors deploy artificial intelligence to identify and exploit zero-day flaws within minutes, drastically shortening attack timelines and raising the stakes for defenders.
GLOBAL, May 4, 2026, 12:33 UTC
Cybersecurity analysts have observed a dramatic change in how threat actors discover and weaponize zero-day vulnerabilities, with artificial intelligence now enabling exploitation at unprecedented speeds.
Researchers at Cyberthint documented this shift, noting that attackers have moved beyond using AI as a mere research tool. Instead, AI systems actively scan software for unknown security flaws and generate exploits in a matter of minutes rather than the months or years previously required.
This acceleration compresses the window defenders have to detect and patch critical vulnerabilities, increasing the risk of widespread breaches. The automation of zero-day discovery and exploitation means that traditional manual methods of vulnerability hunting are becoming obsolete.
The implications are severe for organizations relying on patch management cycles that cannot keep pace with AI-driven attacks. Security teams must now anticipate threats evolving at machine speed, which demands faster incident response and more proactive threat hunting.
Cyberthint's findings, first identified in late 2024, signal a structural transformation in cyberattack methodologies. The firm warns that this trend will likely expand as AI capabilities continue to mature and become more accessible to malicious actors.
Experts suggest that defenders invest in AI-powered detection tools to counterbalance attackers' advantages. Enhanced behavioral analytics and real-time monitoring may help identify exploitation attempts earlier in the attack lifecycle.
The rapid emergence of AI-enabled zero-day exploitation also raises concerns about the effectiveness of current vulnerability disclosure programs. Traditional coordination between software vendors and security researchers may struggle to keep up with the pace of automated attacks.
Companies are urged to prioritize zero-trust architectures and implement strict access controls to limit the damage potential of zero-day exploits. Regular penetration testing and threat modeling can help identify weak points before attackers do.
While AI offers defenders new capabilities, the asymmetric advantage currently favors attackers who can automate complex tasks at scale. This dynamic underscores the urgency for the cybersecurity community to adapt defensive strategies accordingly.
The risk landscape remains uncertain as AI tools become more sophisticated and widely distributed. Organizations should prepare for evolving threats by fostering collaboration between industry, government, and academia to develop resilient security frameworks.
Source: https://securityboulevard.com/2026/05/threat-actors-use-ai-to-automate-zero-day-discovery-and-exploitation-at-machine-speed/
Sources used for this article
securityboulevard.com
