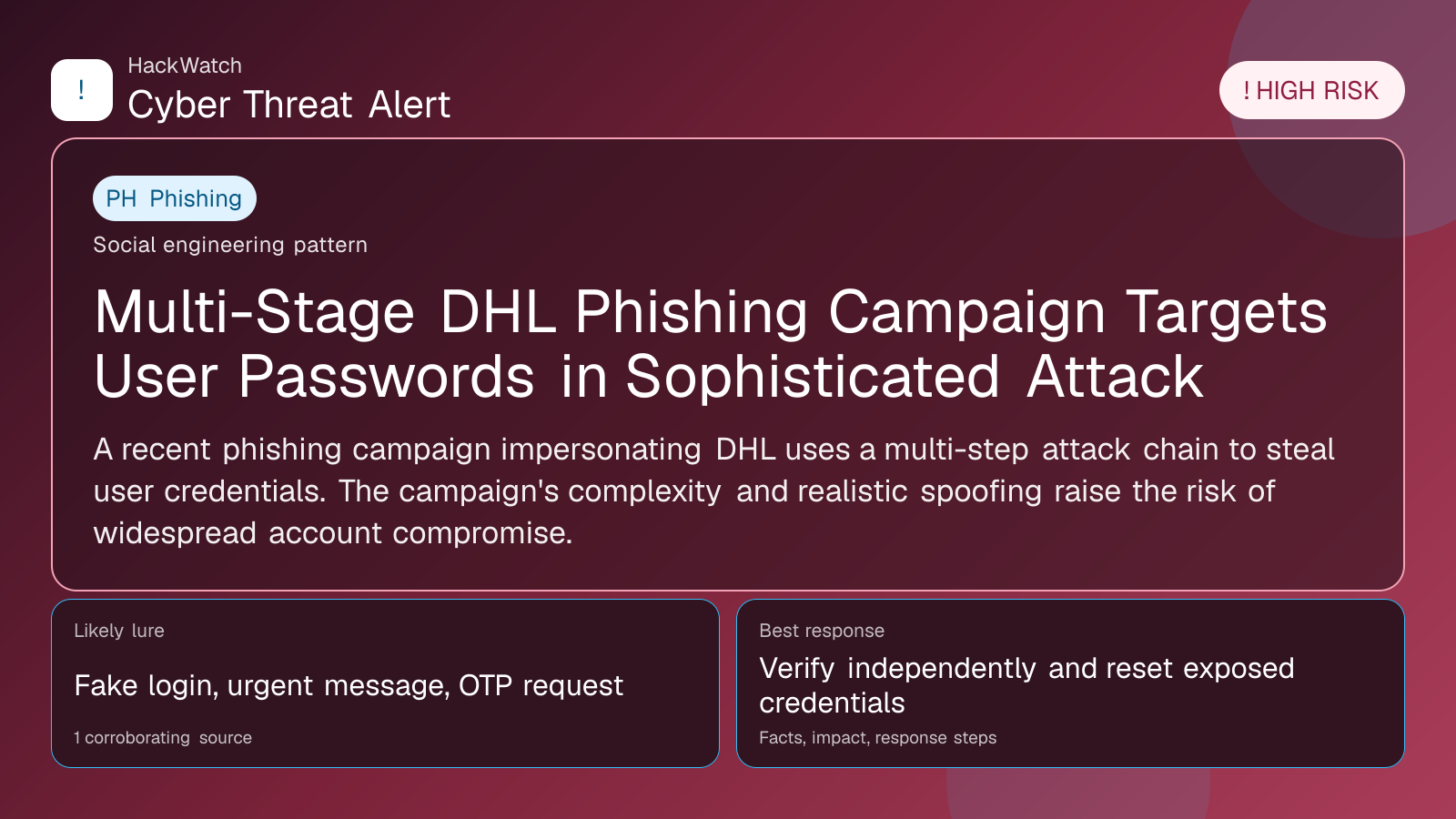
Multi-Stage DHL Phishing Campaign Targets User Passwords in Sophisticated Attack
Verification-lure coverage focused on fake messages, cloned pages and account defense steps.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 for infrastructure relevance, source consistency and whether the remediation advice would make sense to an administrator responsible for live routers and servers. His note keeps the action list grounded: validate scope, reduce exposed management paths, keep evidence intact and avoid claims that go beyond the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A recent phishing campaign impersonating DHL uses a multi-step attack chain to steal user credentials. The campaign's complexity and realistic spoofing raise the risk of widespread account compromise.
GLOBAL, April 30, 2026, 16:39 UTC
- Threat actors launched a multi-stage phishing campaign spoofing DHL to harvest passwords.
- The attack chain involves several steps to evade detection and increase success rates.
Cybersecurity researchers have uncovered a sophisticated phishing campaign that impersonates DHL, the global logistics provider, to steal users’ passwords through a multi-stage attack chain.
The campaign’s complexity lies in its layered approach, where threat actors first lure victims with convincing DHL-branded emails before guiding them through multiple steps designed to bypass security filters and increase the likelihood of credential theft.
This matters now as phishing remains a top vector for cybercriminals to gain unauthorized access to corporate and personal accounts. The use of a trusted brand like DHL increases the chances that recipients will engage with the malicious content.
According to reports, the initial email often includes a fake delivery notification or shipment alert, prompting users to click on a link that leads to a fraudulent login page closely resembling DHL’s official site.
Once users enter their credentials, the attackers capture the information and may use it to access other accounts if password reuse is detected. The multi-stage nature of the attack may also involve redirecting victims through several domains to obscure the phishing infrastructure.
The campaign’s design shows an evolution in phishing tactics, moving beyond simple one-step scams to more elaborate sequences that exploit user trust and technical blind spots in email security.
Security experts warn that organizations and individuals should be especially vigilant with unsolicited emails related to package deliveries or shipment updates, as these remain common phishing lures.
To mitigate risks, users are advised to verify shipment details directly through official DHL channels and avoid clicking on links or downloading attachments from unexpected emails.
Multi-factor authentication (MFA) is strongly recommended to reduce the impact of stolen credentials, as it adds an additional verification layer beyond just passwords.
While DHL has not publicly commented on this specific campaign, companies in the logistics sector are frequent targets due to their extensive customer base and reliance on email communications.
The campaign underscores the need for continuous user education on phishing recognition and for organizations to deploy advanced email filtering and threat detection tools.
Risks remain high as attackers refine their methods, and the potential for credential reuse across services means a single compromised password can lead to broader account takeovers.
Users should regularly review account activity for suspicious behavior and change passwords immediately if phishing exposure is suspected.
This incident aligns with a broader trend of multi-stage phishing attacks observed across various sectors, emphasizing the importance of proactive cybersecurity measures.
For more detailed guidance on identifying and responding to phishing attempts, users can consult resources provided by cybersecurity authorities and trusted security vendors.
Sources used for this article
scmagazine.com
