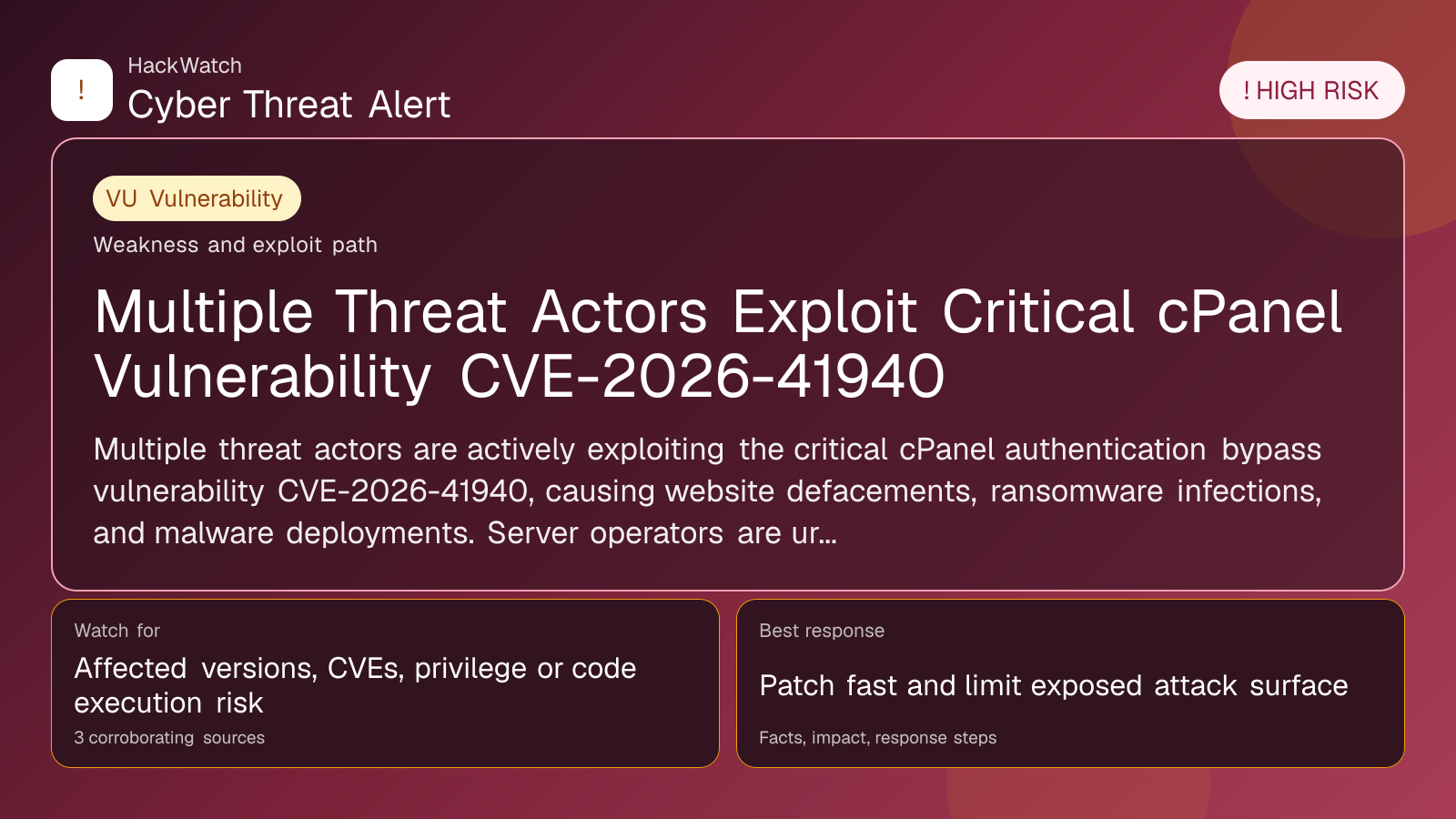
Multiple Threat Actors Exploit Critical cPanel Vulnerability CVE-2026-41940
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
The published article is checked against public sources before publication, and material corrections are reflected in the article update date.
Technical reviewer note: Marcin Pocztowski reviewed this alert on May 04, 2026 from an administrator's point of view, checking CVE-2026-41940, CVE-2026-41940 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 3 corroborating sources supports that scope.
Review our editorial policy or send corrections to [email protected].
Resolved or patched. Source coverage indicates that a fix or formal remediation has been published. Verify that updates are applied in your environment.
Multiple threat actors are actively exploiting the critical cPanel authentication bypass vulnerability CVE-2026-41940, causing website defacements, ransomware infections, and malware deployments. Server operators are urged to apply patches immediately to prevent further damage.
GLOBAL, May 4, 2026, 15:18 UTC
Cybercriminal groups have intensified attacks exploiting the critical cPanel authentication bypass flaw CVE-2026-41940, a report by Help Net Security shows.
Initially detected as scanning activity, these intrusions have escalated into coordinated campaigns targeting vulnerable cPanel servers exposed to the internet. The attacks have resulted in widespread website defacements, ransomware infections, and the installation of malicious software.
CVE-2026-41940 allows attackers to circumvent authentication controls, granting unauthorized access to cPanel’s server management interface. This access enables threat actors to alter websites, exfiltrate data, and deploy ransomware without valid credentials.
One ransomware variant identified in these attacks is a Golang-based Linux encryptor called "Sorry." It encrypts files on compromised servers, appending a distinct extension that locks out legitimate users and demands ransom payments.
Organizations affected by these exploits report service outages and data loss. The attacks pose significant risks to businesses using cPanel for web hosting, particularly those running outdated or unpatched versions.
The urgency to apply patches is driven by the rapid spread and involvement of multiple threat groups. Security researchers warn that delays in updating increase exposure to compromise and operational disruption.
cPanel issued a security update to address CVE-2026-41940 soon after its discovery, but many systems remain vulnerable due to slow patch adoption.
Administrators should verify their cPanel version and install the latest patches immediately. Additional precautions include monitoring server logs for anomalies and implementing network-level controls to restrict unauthorized access.
This ongoing exploitation underscores persistent challenges in securing web hosting infrastructure against automated and targeted attacks. It also illustrates how a single critical vulnerability can be leveraged by various independent actors for financial gain and disruption.
No direct attribution to specific threat groups has been confirmed, but the range of tactics and payloads suggests broad interest in exploiting this flaw.
Organizations are advised to review incident response plans and backup procedures to mitigate potential damage from ransomware.
The threat remains active as attackers continue scanning for unpatched cPanel servers. Prompt remediation and continuous vigilance are essential to defend against this evolving risk.
Further updates are expected as security firms analyze attack methods and release detection tools.
https://www.helpnetsecurity.com/2026/05/04/multiple-threat-actors-actively-exploit-cpanel-vulnerability-cve-2026-41940/
Sources used for this article
gbhackers.com, cybersecuritynews.com, Multiple verified sources, helpnetsecurity.com
