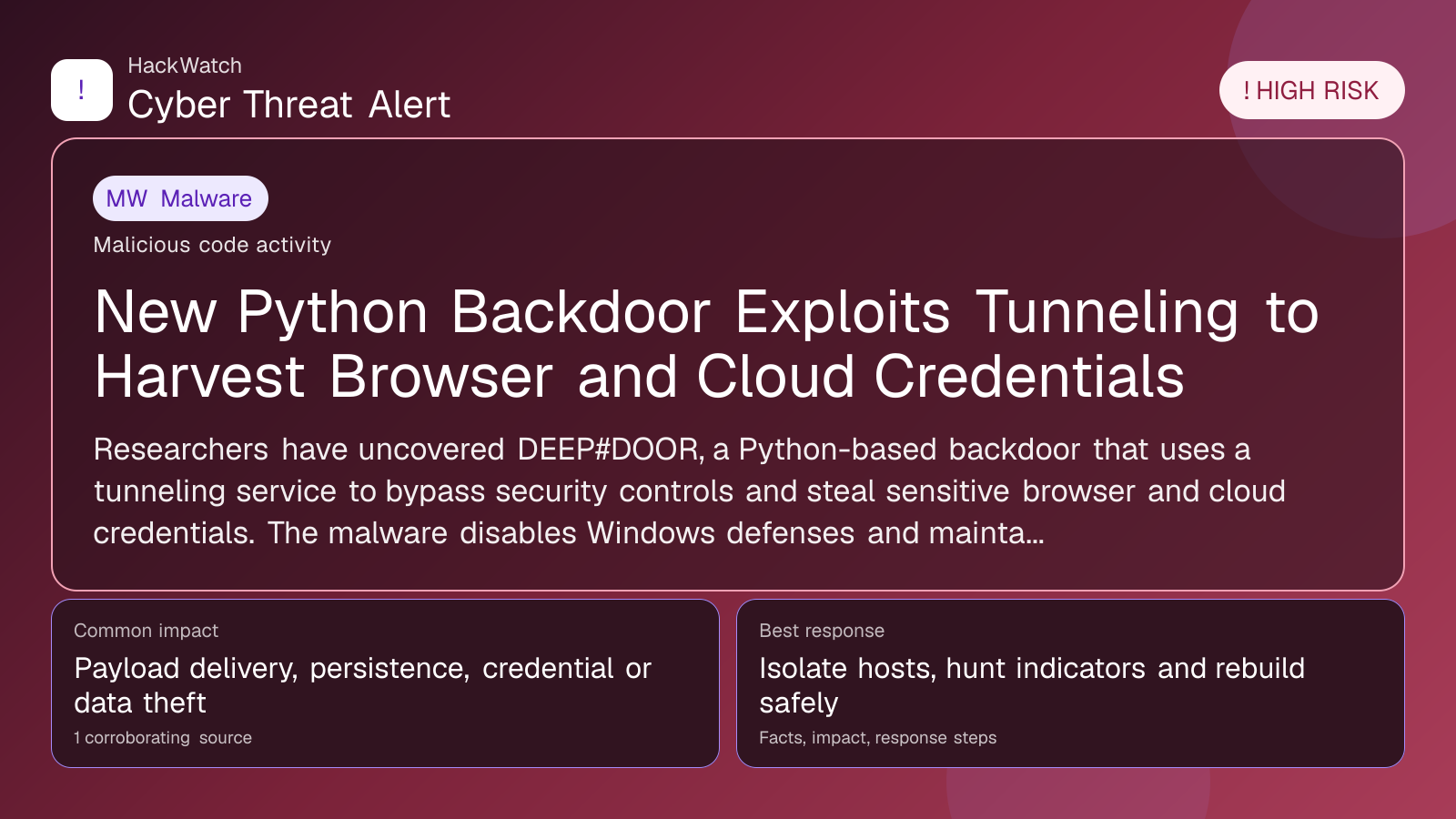
New Python Backdoor Exploits Tunneling to Harvest Browser and Cloud Credentials
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 for server impact, affected-version evidence, privilege or code-execution claims and realistic patch priority. His remediation note follows the same discipline he would use around Juniper routers and production servers: verify scope, preserve useful logs, reduce exposed management access and only then apply the fix or compensating control supported by the 1 corroborating source.
Review our editorial policy or send corrections to [email protected].
Mitigation available. Mitigation guidance or a workaround is available, but defenders should still verify rollout status and exposure.
Researchers have uncovered DEEP#DOOR, a Python-based backdoor that uses a tunneling service to bypass security controls and steal sensitive browser and cloud credentials. The malware disables Windows defenses and maintains persistent access, posing a high risk to compromised systems.
GLOBAL, April 30, 2026, 12:42 UTC
- DEEP#DOOR backdoor uses tunneling to evade detection and steal credentials
- Targets browser data and cloud service accounts for persistent access
- Malware disables Windows security features to maintain foothold
Cybersecurity researchers have revealed a sophisticated Python-based backdoor named DEEP#DOOR that leverages a tunneling service to exfiltrate browser and cloud credentials from infected machines. The malware establishes persistent access by disabling Windows security controls and dynamically extracting its components, according to a report by The Hacker News.
The attack chain initiates with the execution of a batch script, "install_obf.bat," which systematically disables Windows Defender and other native security protections. This step allows the backdoor to operate stealthily without triggering alerts from built-in defenses.
Once active, DEEP#DOOR uses a tunneling service to create an encrypted channel that bypasses network monitoring tools. This technique enables the malware to communicate with its command-and-control infrastructure without raising suspicion, making detection and mitigation more challenging for security teams.
The backdoor harvests a broad spectrum of sensitive data, including saved browser credentials and tokens for cloud platforms. By targeting these credentials, attackers can gain extended access to corporate environments and cloud resources, increasing the risk of data breaches and lateral movement within networks.
The use of Python as the development language allows the backdoor to be cross-platform and easily modified, complicating efforts to create universal detection signatures. Researchers noted that the malware’s modular design facilitates the addition of new capabilities over time.
This discovery comes amid growing concerns over credential theft campaigns that exploit legitimate cloud services and browsers as gateways into enterprise systems. The tunneling method used by DEEP#DOOR highlights a shift towards more covert communication channels in malware operations.
Organizations should review their endpoint detection and response (EDR) configurations to identify unusual batch script executions and monitor for disabled security features. Network teams must also scrutinize outbound traffic for anomalous tunneling connections that could indicate data exfiltration.
While no widespread outbreaks have been reported yet, the high-risk profile of DEEP#DOOR warrants immediate attention from security professionals. Early detection and response can prevent attackers from establishing long-term control over affected systems.
The evolving threat landscape underscores the importance of multi-factor authentication and regular credential rotation, especially for cloud accounts. Users should also be cautious about running unverified scripts that could disable critical security protections.
Further analysis of DEEP#DOOR is ongoing, with researchers urging organizations to share indicators of compromise (IOCs) to enhance collective defense. The malware’s ability to blend into normal network traffic via tunneling services represents a significant challenge for conventional cybersecurity tools.
In summary, DEEP#DOOR exemplifies the increasing sophistication of backdoors that combine stealth, persistence, and credential theft. Its discovery reinforces the need for layered security strategies that encompass endpoint hardening, network monitoring, and user awareness.
As attackers continue to innovate, defenders must adapt quickly to detect and disrupt these advanced intrusion techniques before they can cause significant damage.
---
What to Do Now
- Audit systems for disabled Windows security features and unexpected batch script executions.
- Monitor network traffic for unauthorized tunneling connections.
- Enforce multi-factor authentication on all cloud and browser accounts.
- Rotate credentials regularly and review access logs for anomalies.
- Deploy updated endpoint detection tools capable of identifying Python-based backdoors.
How to Secure Yourself
- Avoid running scripts from untrusted sources.
- Keep operating systems and security software up to date.
- Use password managers to generate and store strong, unique passwords.
- Enable alerts for unusual login activities on cloud platforms.
- Educate users about phishing tactics that may deliver such backdoors.
2026 Update
By the end of 2026, DEEP#DOOR variants have incorporated additional evasion techniques, including polymorphic code and encrypted payloads. Security vendors have responded by integrating behavioral detection methods that focus on suspicious tunneling activity and credential access patterns. However, attackers continue to refine their methods, making vigilance and rapid incident response critical.
---
Source: [The Hacker News](https://thehackernews.com/2026/04/new-python-backdoor-uses-tunneling.html)
Sources used for this article
The Hacker News
