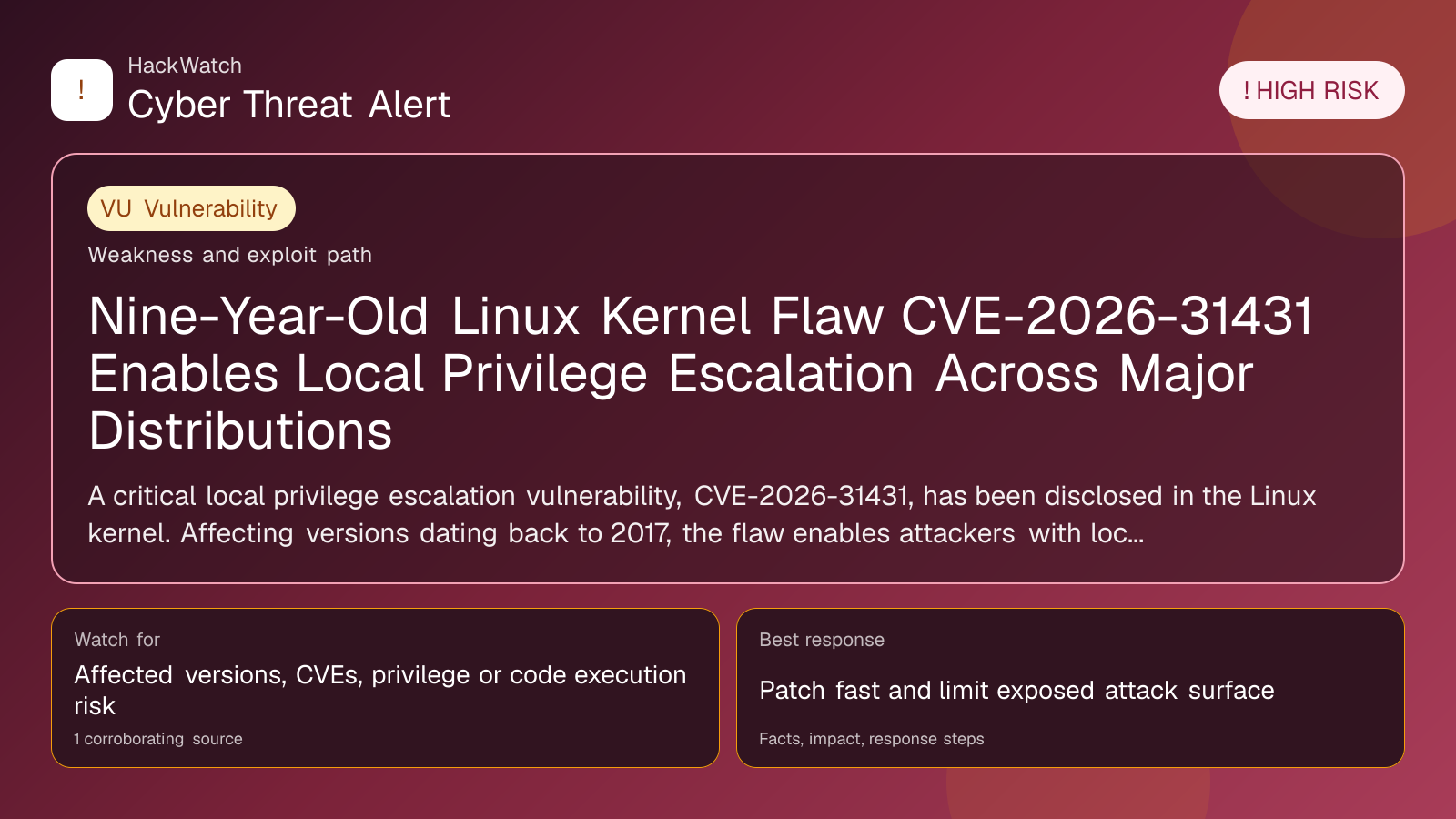
Nine-Year-Old Linux Kernel Flaw CVE-2026-31431 Enables Local Privilege Escalation Across Major Distributions
Vulnerability coverage focused on affected versions, exploitability and patch or mitigation decisions.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 from an administrator's point of view, checking CVE-2026-31431, CVE-2026-31431 against vendor, CVE and advisory context before accepting the risk language. His remediation check is practical: confirm the affected version first, restrict reachable management surfaces as he would on Juniper, Cisco or Mikrotik routers, then patch or apply vendor mitigations only where the 1 corroborating source supports that scope.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
A critical local privilege escalation vulnerability, CVE-2026-31431, has been disclosed in the Linux kernel. Affecting versions dating back to 2017, the flaw enables attackers with local access to gain root privileges. A public proof-of-concept exploit has surfaced, prompting urgent patching across major Linux distributions.
GLOBAL, April 30, 2026, 12:43 UTC
Security researchers at Theori have uncovered a high-severity local privilege escalation (LPE) vulnerability in the Linux kernel, designated CVE-2026-31431. The flaw, nicknamed "Copy Fail," affects Linux kernel versions released since 2017 and allows users with local access to escalate privileges to root.
This vulnerability stems from a complex interaction of kernel changes over several years, including the introduction of authencesn, an AEAD cryptographic wrapper used by IPsec protocols since 2011. These layered modifications inadvertently created a pathway for privilege escalation.
Theori released a functioning proof-of-concept exploit that reliably triggers the vulnerability. This raises concerns about potential exploitation in corporate, cloud, and personal environments where Linux is widely deployed.
Major Linux distributions including Ubuntu, Fedora, Debian, and Red Hat Enterprise Linux have acknowledged the vulnerability. Patches have been issued or are in progress, but many systems remain exposed due to delayed updates or unmanaged deployments.
The flaw is particularly urgent because Linux underpins critical infrastructure such as servers, cloud platforms, and embedded devices. An attacker with local access—whether through a compromised account or insider threat—could leverage this to gain full system control.
System administrators are advised to apply the latest kernel patches immediately. Where patching is not feasible, restricting local user access and monitoring system logs for anomalies can help mitigate risk.
Theori’s analysis underscores the challenges in kernel development, where incremental changes may unintentionally weaken security. The incident highlights the need for continuous, rigorous auditing of kernel code and its dependencies.
Although no widespread exploitation campaigns have been reported, the availability of a public exploit increases the urgency for remediation. Organizations should review patch management practices and verify kernel versions to ensure protection.
Users can check their current kernel version by running `uname -r` in the terminal and should consult their distribution’s security advisories for update instructions. Prompt application of patches remains the most effective defense.
Local privilege escalation vulnerabilities are not unique to Linux, but the longevity and scope of CVE-2026-31431 make this a significant event in open-source security.
Looking forward, the Linux community and vendors are expected to enhance testing frameworks to catch such complex interaction flaws earlier. This case serves as a reminder that even mature, widely used software can harbor critical vulnerabilities for years.
For now, swift patching and vigilant monitoring are essential to reduce the threat posed by CVE-2026-31431.
Source: https://www.helpnetsecurity.com/2026/04/30/copyfail-linux-lpe-vulnerability-cve-2026-31431/
Sources used for this article
helpnetsecurity.com
