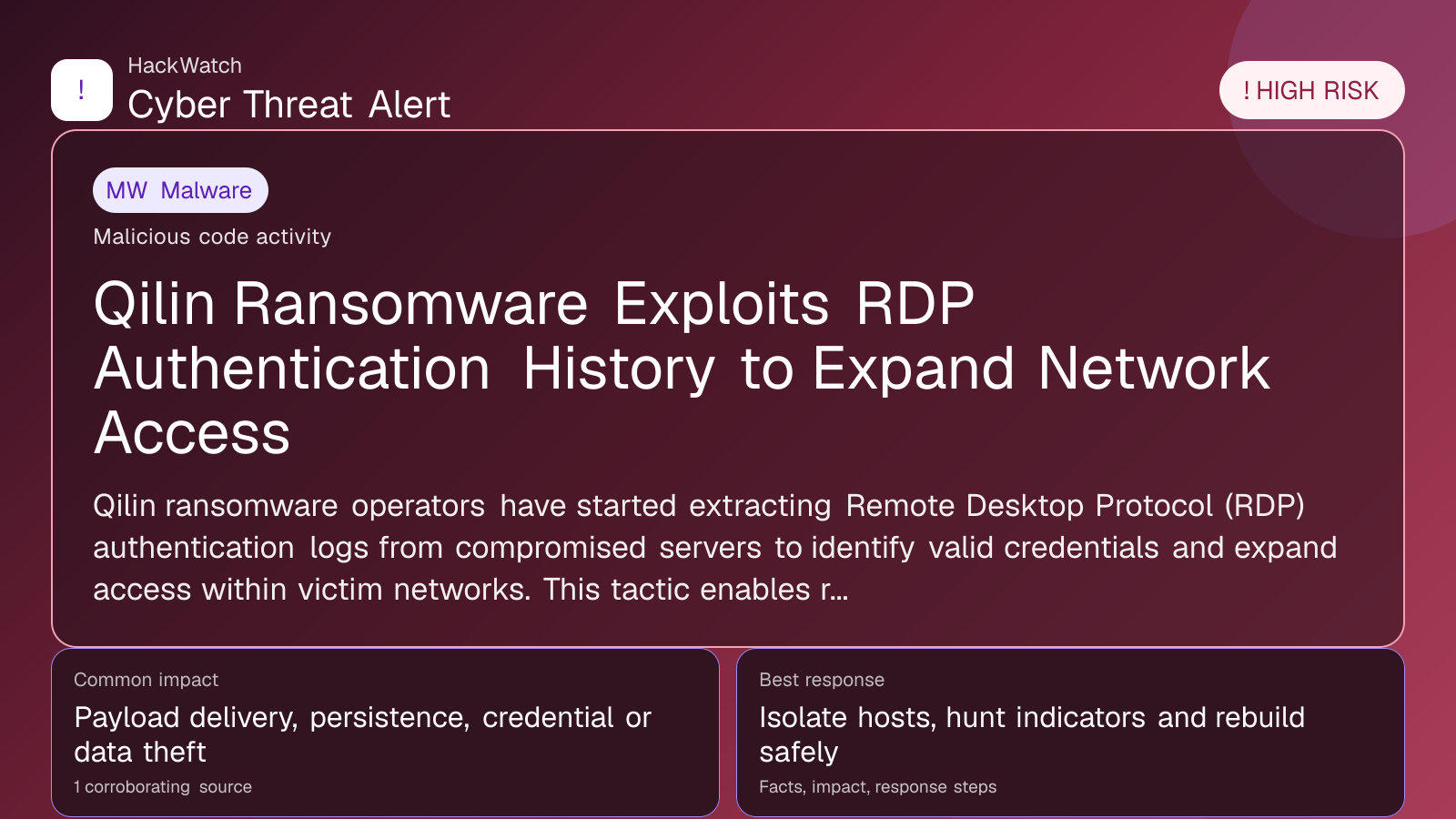
Qilin Ransomware Exploits RDP Authentication History to Expand Network Access
Malware coverage focused on infection paths, containment steps and indicators defenders should watch.
Trust note:This alert is maintained under HackWatch's editorial policy, with visible source records, a named responsible editor and a correction channel for disputed facts.
AI tools may assist HackWatch with initial monitoring and source clustering. The public article is reviewed, fact-checked and edited by a real HackWatch reviewer before publication or material updates. Last human review: Apr 30, 2026.
Technical reviewer note: Marcin Pocztowski reviewed this alert on Apr 30, 2026 as a network administrator, looking first at device role, exposed management planes, VPN or routing impact and the order in which changes can be made without breaking production traffic. His note is deliberately operational: on Juniper-style edge or firewall environments, isolate admin access and preserve logs before patching, and do not claim broader exposure than the 1 corroborating source can prove.
Review our editorial policy or send corrections to [email protected].
Active threat. The incident should still be treated as active until confirmed mitigation or patch adoption is verified.
Qilin ransomware operators have started extracting Remote Desktop Protocol (RDP) authentication logs from compromised servers to identify valid credentials and expand access within victim networks. This tactic enables rapid lateral movement, increasing the scale and stealth of attacks. Security experts advise organizations to strengthen RDP controls and monitor authentication events closely to reduce exposure.
GLOBAL, April 30, 2026, 16:43 UTC
- Qilin ransomware now harvests RDP authentication logs to map networks.
- Attackers use stolen credentials to move laterally and escalate attacks.
- Organizations urged to tighten RDP security and monitor authentication events.
Qilin ransomware operators have adopted a new tactic that involves extracting Remote Desktop Protocol (RDP) authentication history from compromised servers, according to a recent report by Cyber Security News. This method helps attackers identify valid credentials and additional systems within victim networks, enabling faster and quieter lateral movement.
RDP, a common protocol for remote server management, has long been exploited due to weak authentication and exposed endpoints. By enumerating login records stored on compromised hosts, Qilin operators bypass some traditional security measures and expand their reach without immediate detection.
Security researchers warn this technique raises risks for organizations relying on RDP, especially those lacking robust logging, strong password policies, or multi-factor authentication (MFA). Attackers can quietly harvest credentials and systematically compromise multiple servers before deploying ransomware.
The development highlights the need for continuous monitoring of authentication events and swift response to unusual login activity. Organizations should regularly audit RDP access logs and enforce strict access controls to limit exposure.
Beyond credential harvesting, Qilin ransomware continues to encrypt critical data and demand substantial ransoms. The group has been linked to several high-impact incidents worldwide, causing operational disruptions and financial damage.
Experts recommend disabling RDP where possible or restricting access through VPNs and enforcing MFA. Network segmentation can further reduce attackers’ ability to move laterally using harvested credentials.
This technique reflects a broader trend of ransomware groups refining intrusion methods to evade detection and maximize impact. Qilin’s use of RDP authentication log enumeration exemplifies this adaptive approach.
Organizations should verify recent RDP access on their systems and scrutinize authentication logs for anomalies. Early detection of compromised credentials can prevent further spread and reduce ransomware success rates.
Failure to address these vulnerabilities risks more extensive breaches and higher ransom demands. The evolving threat landscape requires proactive security focused on access management and real-time monitoring.
As Qilin ransomware evolves, cybersecurity teams must prioritize RDP security hardening and incident response preparedness to mitigate this high-risk attack vector.
For additional details, see the original Cyber Security News report: https://cybersecuritynews.com/qilin-ransomware-enumerates-rdp-authentication/
Sources used for this article
cybersecuritynews.com
